4.0
1NSchAb
1NSchAb
- No tags were found...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
197<br />
Web Application Penetration Testing<br />
Testing for Cross site flashing<br />
(OTG-CLIENT-008)<br />
Summary<br />
ActionScript is the language, based on ECMAScript, used by Flash<br />
applications when dealing with interactive needs. There are three<br />
versions of the ActionScript language. ActionScript 1.0 and Action-<br />
Script 2.0 are very similar with ActionScript 2.0 being an extension of<br />
ActionScript 1.0. ActionScript 3.0, introduced with Flash Player 9, is a<br />
rewrite of the language to support object orientated design.<br />
ActionScript, like every other language, has some implementation<br />
patterns which could lead to security issues. In particular, since Flash<br />
applications are often embedded in browsers, vulnerabilities like<br />
DOM based Cross-Site Scripting (XSS) could be present in flawed<br />
Flash applications.<br />
How to Test<br />
Since the first publication of “Testing Flash Applications” [1], new<br />
versions of Flash player were released in order to mitigate some of<br />
the attacks which will be described. Nevertheless, some issues still<br />
remain exploitable because they are the result of insecure programming<br />
practices.<br />
Decompilation<br />
Since SWF files are interpreted by a virtual machine embedded in the<br />
player itself, they can be potentially decompiled and analysed. The<br />
most known and free ActionScript 2.0 decompiler is flare.<br />
To decompile a SWF file with flare just type:<br />
$ flare hello.swf<br />
it will result in a new file called hello.flr.<br />
Decompilation helps testers because it allows for source code assisted,<br />
or white-box, testing of the Flash applications. HP’s free<br />
SWFScan tool can decompile both ActionScript 2.0 and ActionScript<br />
3.0 SWFScan<br />
The OWASP Flash Security Project maintains a list of current disassemblers,<br />
decompilers and other Adobe Flash related testing tools.<br />
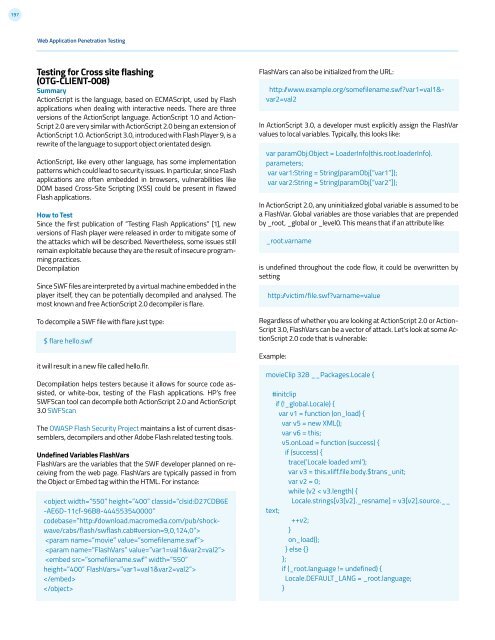
Undefined Variables FlashVars<br />
FlashVars are the variables that the SWF developer planned on receiving<br />
from the web page. FlashVars are typically passed in from<br />
the Object or Embed tag within the HTML. For instance:<br />
<br />
<br />
<br />
<br />
<br />
<br />
FlashVars can also be initialized from the URL:<br />
http: /www.example.org/somefilename.swf?var1=val1&-<br />
var2=val2<br />
In ActionScript 3.0, a developer must explicitly assign the FlashVar<br />
values to local variables. Typically, this looks like:<br />
var paramObj:Object = LoaderInfo(this.root.loaderInfo).<br />
parameters;<br />
var var1:String = String(paramObj[“var1”]);<br />
var var2:String = String(paramObj[“var2”]);<br />
In ActionScript 2.0, any uninitialized global variable is assumed to be<br />
a FlashVar. Global variables are those variables that are prepended<br />
by _root, _global or _level0. This means that if an attribute like:<br />
_root.varname<br />
is undefined throughout the code flow, it could be overwritten by<br />
setting<br />
http: /victim/file.swf?varname=value<br />
Regardless of whether you are looking at ActionScript 2.0 or Action-<br />
Script 3.0, FlashVars can be a vector of attack. Let’s look at some ActionScript<br />
2.0 code that is vulnerable:<br />
Example:<br />
movieClip 328 __Packages.Locale {<br />
#initclip<br />
if (!_global.Locale) {<br />
var v1 = function (on_load) {<br />
var v5 = new XML();<br />
var v6 = this;<br />
v5.onLoad = function (success) {<br />
if (success) {<br />
trace(‘Locale loaded xml’);<br />
var v3 = this.xliff.file.body.$trans_unit;<br />
var v2 = 0;<br />
while (v2 < v3.length) {<br />
Locale.strings[v3[v2]._resname] = v3[v2].source.__<br />
text;<br />
++v2;<br />
}<br />
on_load();<br />
} else {}<br />
};<br />
if (_root.language != undefined) {<br />
Locale.DEFAULT_LANG = _root.language;<br />
}