4.0
1NSchAb
1NSchAb
- No tags were found...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
136<br />
Web Application Penetration Testing<br />
foo><br />
<br />
]>&xxe;<br />
<br />
]>&xxe;<br />
<br />
]>&xxe;<br />
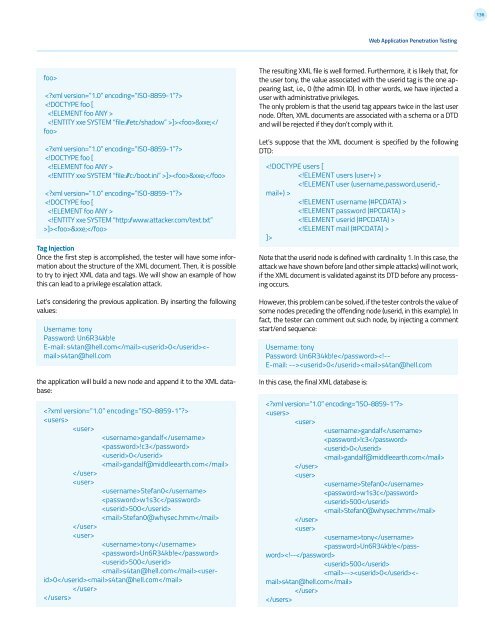
Tag Injection<br />
Once the first step is accomplished, the tester will have some information<br />
about the structure of the XML document. Then, it is possible<br />
to try to inject XML data and tags. We will show an example of how<br />
this can lead to a privilege escalation attack.<br />
Let’s considering the previous application. By inserting the following<br />
values:<br />
Username: tony<br />
Password: Un6R34kb!e<br />
E-mail: s4tan@hell.com0s4tan@hell.com<br />
the application will build a new node and append it to the XML database:<br />
<br />
<br />
<br />
gandalf<br />
!c3<br />
0<br />
gandalf@middleearth.com<br />
<br />
<br />
Stefan0<br />
w1s3c<br />
500<br />
Stefan0@whysec.hmm<br />
<br />
<br />
tony<br />
Un6R34kb!e<br />
500<br />
s4tan@hell.com0s4tan@hell.com<br />
<br />
<br />
The resulting XML file is well formed. Furthermore, it is likely that, for<br />
the user tony, the value associated with the userid tag is the one appearing<br />
last, i.e., 0 (the admin ID). In other words, we have injected a<br />
user with administrative privileges.<br />
The only problem is that the userid tag appears twice in the last user<br />
node. Often, XML documents are associated with a schema or a DTD<br />
and will be rejected if they don’t comply with it.<br />
Let’s suppose that the XML document is specified by the following<br />
DTD:<br />
<br />
<br />
<br />
<br />
<br />
]><br />
Note that the userid node is defined with cardinality 1. In this case, the<br />
attack we have shown before (and other simple attacks) will not work,<br />
if the XML document is validated against its DTD before any processing<br />
occurs.<br />
However, this problem can be solved, if the tester controls the value of<br />
some nodes preceding the offending node (userid, in this example). In<br />
fact, the tester can comment out such node, by injecting a comment<br />
start/end sequence:<br />
Username: tony<br />
Password: Un6R34kb!e0s4tan@hell.com<br />
In this case, the final XML database is:<br />
<br />
<br />
<br />
gandalf<br />
!c3<br />
0<br />
gandalf@middleearth.com<br />
<br />
<br />
Stefan0<br />
w1s3c<br />
500<br />
Stefan0@whysec.hmm<br />
<br />
<br />
tony<br />
Un6R34kb!e0s4tan@hell.com<br />
<br />