4.0
1NSchAb
1NSchAb
- No tags were found...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
160<br />
Web Application Penetration Testing<br />
$ curl -kis http:/example.com/restricted/<br />
HTTP/1.1 401 Authorization Required<br />
Date: Fri, 01 Aug 2013 00:00:00 GMT<br />
WWW-Authenticate: Basic realm=”Restricted Area”<br />
Accept-Ranges: bytes<br />
Vary: Accept-Encoding<br />
Content-Length: 162<br />
Content-Type: text/html<br />
401 Authorization Required<br />
<br />
401 Authorization Required<br />
Invalid login credentials!<br />
<br />
Testing for Weak SSL/TLS Ciphers/Protocols/Keys vulnerabilities<br />
The large number of available cipher suites and quick progress<br />
in cryptanalysis makes testing an SSL server a non-trivial task.<br />
At the time of writing these criteria are widely recognized as<br />
minimum checklist:<br />
• Weak ciphers must not be used (e.g. less than 128 bits [10]; no<br />
NULL ciphers suite, due to no encryption used; no Anonymous<br />
Diffie-Hellmann, due to not provides authentication).<br />
• Weak protocols must be disabled (e.g. SSLv2 must be disabled,<br />
due to known weaknesses in protocol design [11]).<br />
• Renegotiation must be properly configured (e.g. Insecure<br />
Renegotiation must be disabled, due to MiTM attacks [12] and<br />
Client-initiated Renegotiation must be disabled, due to Denial of<br />
Service vulnerability [13]).<br />
• No Export (EXP) level cipher suites, due to can be easly broken<br />
[10].<br />
• X.509 certificates key length must be strong (e.g. if RSA or DSA<br />
is used the key must be at least 1024 bits).<br />
• X.509 certificates must be signed only with secure hashing<br />
algoritms (e.g. not signed using MD5 hash, due to known collision<br />
attacks on this hash).<br />
• Keys must be generated with proper entropy (e.g, Weak Key<br />
Generated with Debian) [14].<br />
A more complete checklist includes:<br />
• Secure Renegotiation should be enabled.<br />
• MD5 should not be used, due to known collision attacks. [35]<br />
• RC4 should not be used, due to crypto-analytical attacks [15].<br />
• Server should be protected from BEAST Attack [16].<br />
• Server should be protected from CRIME attack, TLS compres<br />
sion must be disabled [17].<br />
• Server should support Forward Secrecy [18].<br />
The following standards can be used as reference while assessing<br />
SSL servers:<br />
• PCI-DSS v2.0 in point 4.1 requires compliant parties to use<br />
“strong cryptography” without precisely defining key lengths and<br />
algorithms. Common interpretation, partially based on previous<br />
versions of the standard, is that at least 128 bit key cipher, no<br />
export strength algorithms and no SSLv2 should be used [19].<br />
• Qualys SSL Labs Server Rating Guide [14], Depoloyment best<br />
practice [10] and SSL Threat Model [20] has been proposed to<br />
standardize SSL server assessment and configuration. But is less<br />
updated than the SSL Server tool [21].<br />
• OWASP has a lot of resources about SSL/TLS Security [22],<br />
[23], [24], [25]. [26].<br />
Some tools and scanners both free (e.g. SSLAudit [28] or SSLScan<br />
[29]) and commercial (e.g. Tenable Nessus [27]), can be used to assess<br />
SSL/TLS vulnerabilities. But due to evolution of these vulnerabilities<br />
a good way to test is to check them manually with openssl<br />
[30] or use the tool’s output as an input for manual evaluation using<br />
the references.<br />
Sometimes the SSL/TLS enabled service is not directly accessible<br />
and the tester can access it only via a HTTP proxy using CONNECT<br />
method [36]. Most of the tools will try to connect to desired tcp port<br />
to start SSL/TLS handshake. This will not work since desired port is<br />
accessible only via HTTP proxy. The tester can easily circumvent this<br />
by using relaying software such as socat [37].<br />
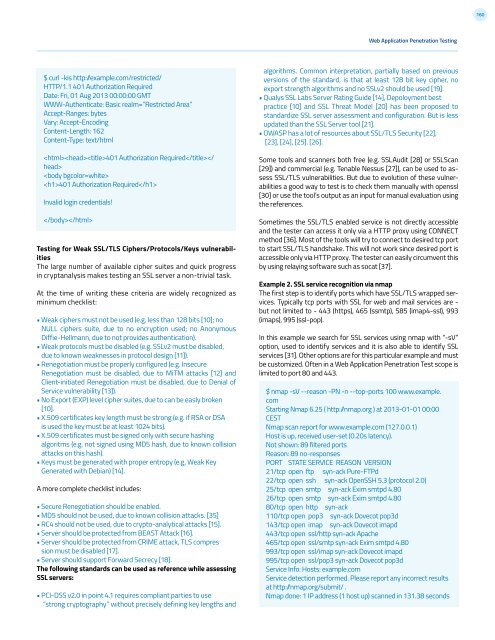
Example 2. SSL service recognition via nmap<br />
The first step is to identify ports which have SSL/TLS wrapped services.<br />
Typically tcp ports with SSL for web and mail services are -<br />
but not limited to - 443 (https), 465 (ssmtp), 585 (imap4-ssl), 993<br />
(imaps), 995 (ssl-pop).<br />
In this example we search for SSL services using nmap with “-sV”<br />
option, used to identify services and it is also able to identify SSL<br />
services [31]. Other options are for this particular example and must<br />
be customized. Often in a Web Application Penetration Test scope is<br />
limited to port 80 and 443.<br />
$ nmap -sV --reason -PN -n --top-ports 100 www.example.<br />
com<br />
Starting Nmap 6.25 ( http:/nmap.org ) at 2013-01-01 00:00<br />
CEST<br />
Nmap scan report for www.example.com (127.0.0.1)<br />
Host is up, received user-set (0.20s latency).<br />
Not shown: 89 filtered ports<br />
Reason: 89 no-responses<br />
PORT STATE SERVICE REASON VERSION<br />
21/tcp open ftp syn-ack Pure-FTPd<br />
22/tcp open ssh syn-ack OpenSSH 5.3 (protocol 2.0)<br />
25/tcp open smtp syn-ack Exim smtpd 4.80<br />
26/tcp open smtp syn-ack Exim smtpd 4.80<br />
80/tcp open http syn-ack<br />
110/tcp open pop3 syn-ack Dovecot pop3d<br />
143/tcp open imap syn-ack Dovecot imapd<br />
443/tcp open ssl/http syn-ack Apache<br />
465/tcp open ssl/smtp syn-ack Exim smtpd 4.80<br />
993/tcp open ssl/imap syn-ack Dovecot imapd<br />
995/tcp open ssl/pop3 syn-ack Dovecot pop3d<br />
Service Info: Hosts: example.com<br />
Service detection performed. Please report any incorrect results<br />
at http:/nmap.org/submit/ .<br />
Nmap done: 1 IP address (1 host up) scanned in 131.38 seconds