4.0
1NSchAb
1NSchAb
- No tags were found...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
45<br />
Web Application Penetration Testing<br />
less, it is recommended to check the whole document since it can be<br />
useful for other purposes such as inspection of other useful comments<br />
and hidden fields.<br />
Specific files and folders<br />
Apart from information gathered from HTML sources, there is another<br />
approach which greatly helps an attacker to determine the<br />
application with high accuracy. Every application has its own specific<br />
file and folder structure on the server. It has been pointed out<br />
that one can see the specific path from the HTML page source but<br />
sometimes they are not explicitly presented there and still reside<br />
on the server.<br />
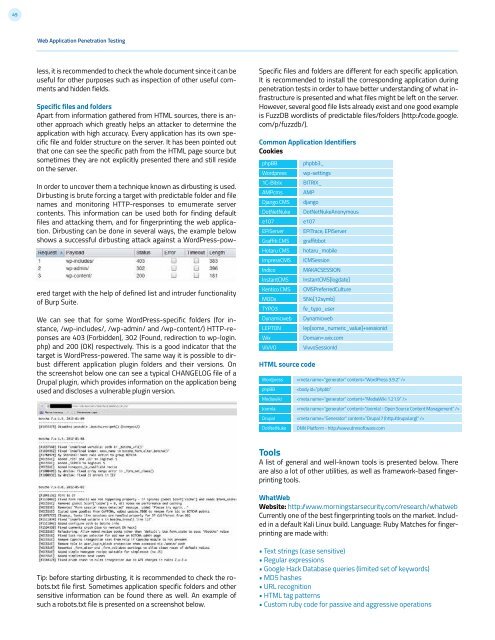
In order to uncover them a technique known as dirbusting is used.<br />
Dirbusting is brute forcing a target with predictable folder and file<br />
names and monitoring HTTP-responses to emumerate server<br />
contents. This information can be used both for finding default<br />
files and attacking them, and for fingerprinting the web application.<br />
Dirbusting can be done in several ways, the example below<br />
shows a successful dirbusting attack against a WordPress-powered<br />
target with the help of defined list and intruder functionality<br />
of Burp Suite.<br />
We can see that for some WordPress-specific folders (for instance,<br />
/wp-includes/, /wp-admin/ and /wp-content/) HTTP-reponses<br />
are 403 (Forbidden), 302 (Found, redirection to wp-login.<br />
php) and 200 (OK) respectively. This is a good indicator that the<br />
target is WordPress-powered. The same way it is possible to dirbust<br />
different application plugin folders and their versions. On<br />
the screenshot below one can see a typical CHANGELOG file of a<br />
Drupal plugin, which provides information on the application being<br />
used and discloses a vulnerable plugin version.<br />
Specific files and folders are different for each specific application.<br />
It is recommended to install the corresponding application during<br />
penetration tests in order to have better understanding of what infrastructure<br />
is presented and what files might be left on the server.<br />
However, several good file lists already exist and one good example<br />
is FuzzDB wordlists of predictable files/folders (http: /code.google.<br />
com/p/fuzzdb/).<br />
Common Application Identifiers<br />
Cookies<br />
phpBB<br />
Wordpress<br />
1C-Bitrix<br />
AMPcms<br />
Django CMS<br />
DotNetNuke<br />
e107<br />
EPiServer<br />
Graffiti CMS<br />
Hotaru CMS<br />
ImpressCMS<br />
Indico<br />
InstantCMS<br />
Kentico CMS<br />
MODx<br />
TYPO3<br />
Dynamicweb<br />
LEPTON<br />
Wix<br />
VIVVO<br />
HTML source code<br />
Wordpress<br />
phpBB<br />
Mediawiki<br />
Joomla<br />
Drupal<br />
DotNetNuke<br />
phpbb3_<br />
wp-settings<br />
BITRIX_<br />
AMP<br />
django<br />
DotNetNukeAnonymous<br />
e107<br />
EPiTrace, EPiServer<br />
graffitibot<br />
hotaru_mobile<br />
ICMSession<br />
MAKACSESSION<br />
InstantCMS[logdate]<br />
CMSPreferredCulture<br />
SN4[12symb]<br />
fe_typo_user<br />
Dynamicweb<br />
lep[some_numeric_value]+sessionid<br />
Domain=.wix.com<br />
VivvoSessionId<br />
<br />