4.0
1NSchAb
1NSchAb
- No tags were found...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
162<br />
Web Application Penetration Testing<br />
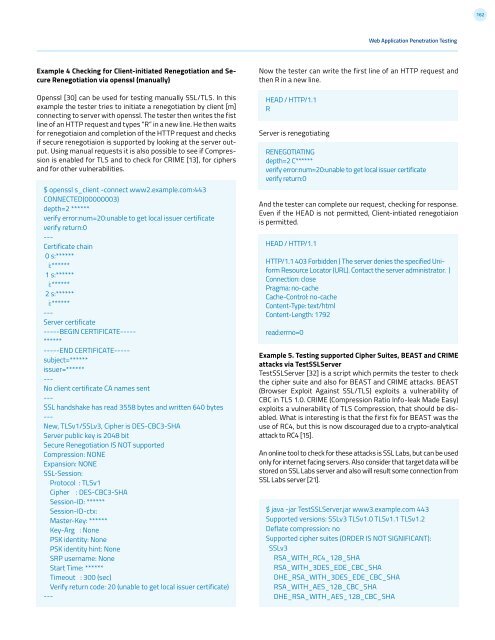
Example 4 Checking for Client-initiated Renegotiation and Secure<br />
Renegotiation via openssl (manually)<br />
Openssl [30] can be used for testing manually SSL/TLS. In this<br />
example the tester tries to initiate a renegotiation by client [m]<br />
connecting to server with openssl. The tester then writes the fist<br />
line of an HTTP request and types “R” in a new line. He then waits<br />
for renegotiaion and completion of the HTTP request and checks<br />
if secure renegotiaion is supported by looking at the server output.<br />
Using manual requests it is also possible to see if Compression<br />
is enabled for TLS and to check for CRIME [13], for ciphers<br />
and for other vulnerabilities.<br />
$ openssl s_client -connect www2.example.com:443<br />
CONNECTED(00000003)<br />
depth=2 ******<br />
verify error:num=20:unable to get local issuer certificate<br />
verify return:0<br />
---<br />
Certificate chain<br />
0 s:******<br />
i:******<br />
1 s:******<br />
i:******<br />
2 s:******<br />
i:******<br />
---<br />
Server certificate<br />
-----BEGIN CERTIFICATE-----<br />
******<br />
-----END CERTIFICATE-----<br />
subject=******<br />
issuer=******<br />
---<br />
No client certificate CA names sent<br />
---<br />
SSL handshake has read 3558 bytes and written 640 bytes<br />
---<br />
New, TLSv1/SSLv3, Cipher is DES-CBC3-SHA<br />
Server public key is 2048 bit<br />
Secure Renegotiation IS NOT supported<br />
Compression: NONE<br />
Expansion: NONE<br />
SSL-Session:<br />
Protocol : TLSv1<br />
Cipher : DES-CBC3-SHA<br />
Session-ID: ******<br />
Session-ID-ctx:<br />
Master-Key: ******<br />
Key-Arg : None<br />
PSK identity: None<br />
PSK identity hint: None<br />
SRP username: None<br />
Start Time: ******<br />
Timeout : 300 (sec)<br />
Verify return code: 20 (unable to get local issuer certificate)<br />
---<br />
Now the tester can write the first line of an HTTP request and<br />
then R in a new line.<br />
HEAD / HTTP/1.1<br />
R<br />
Server is renegotiating<br />
RENEGOTIATING<br />
depth=2 C******<br />
verify error:num=20:unable to get local issuer certificate<br />
verify return:0<br />
And the tester can complete our request, checking for response.<br />
Even if the HEAD is not permitted, Client-intiated renegotiaion<br />
is permitted.<br />
HEAD / HTTP/1.1<br />
HTTP/1.1 403 Forbidden ( The server denies the specified Uniform<br />
Resource Locator (URL). Contact the server administrator. )<br />
Connection: close<br />
Pragma: no-cache<br />
Cache-Control: no-cache<br />
Content-Type: text/html<br />
Content-Length: 1792<br />
read:errno=0<br />
Example 5. Testing supported Cipher Suites, BEAST and CRIME<br />
attacks via TestSSLServer<br />
TestSSLServer [32] is a script which permits the tester to check<br />
the cipher suite and also for BEAST and CRIME attacks. BEAST<br />
(Browser Exploit Against SSL/TLS) exploits a vulnerability of<br />
CBC in TLS 1.0. CRIME (Compression Ratio Info-leak Made Easy)<br />
exploits a vulnerability of TLS Compression, that should be disabled.<br />
What is interesting is that the first fix for BEAST was the<br />
use of RC4, but this is now discouraged due to a crypto-analytical<br />
attack to RC4 [15].<br />
An online tool to check for these attacks is SSL Labs, but can be used<br />
only for internet facing servers. Also consider that target data will be<br />
stored on SSL Labs server and also will result some connection from<br />
SSL Labs server [21].<br />
$ java -jar TestSSLServer.jar www3.example.com 443<br />
Supported versions: SSLv3 TLSv1.0 TLSv1.1 TLSv1.2<br />
Deflate compression: no<br />
Supported cipher suites (ORDER IS NOT SIGNIFICANT):<br />
SSLv3<br />
RSA_WITH_RC4_128_SHA<br />
RSA_WITH_3DES_EDE_CBC_SHA<br />
DHE_RSA_WITH_3DES_EDE_CBC_SHA<br />
RSA_WITH_AES_128_CBC_SHA<br />
DHE_RSA_WITH_AES_128_CBC_SHA