4.0
1NSchAb
1NSchAb
- No tags were found...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
67<br />
Web Application Penetration Testing<br />
ture packet headers and to inspect them. You can use any web<br />
proxy that you prefer.<br />
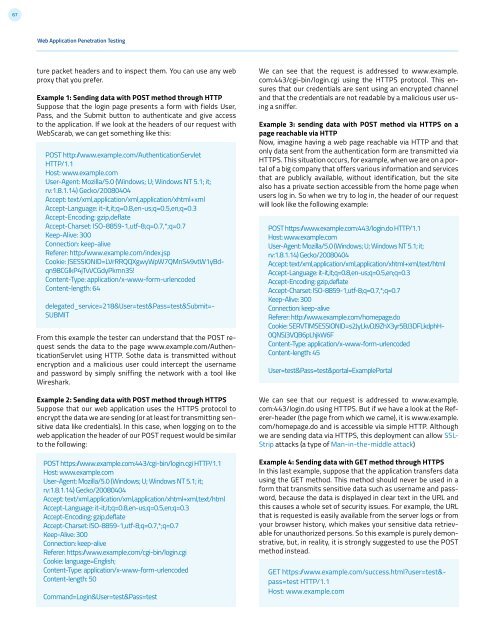
Example 1: Sending data with POST method through HTTP<br />
Suppose that the login page presents a form with fields User,<br />
Pass, and the Submit button to authenticate and give access<br />
to the application. If we look at the headers of our request with<br />
WebScarab, we can get something like this:<br />
POST http:/www.example.com/AuthenticationServlet<br />
HTTP/1.1<br />
Host: www.example.com<br />
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 5.1; it;<br />
rv:1.8.1.14) Gecko/20080404<br />
Accept: text/xml,application/xml,application/xhtml+xml<br />
Accept-Language: it-it,it;q=0.8,en-us;q=0.5,en;q=0.3<br />
Accept-Encoding: gzip,deflate<br />
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.7<br />
Keep-Alive: 300<br />
Connection: keep-alive<br />
Referer: http:/www.example.com/index.jsp<br />
Cookie: JSESSIONID=LVrRRQQXgwyWpW7QMnS49vtW1yBdqn98CGlkP4jTvVCGdyPkmn3S!<br />
Content-Type: application/x-www-form-urlencoded<br />
Content-length: 64<br />
delegated_service=218&User=test&Pass=test&Submit=-<br />
SUBMIT<br />
From this example the tester can understand that the POST request<br />
sends the data to the page www.example.com/AuthenticationServlet<br />
using HTTP. Sothe data is transmitted without<br />
encryption and a malicious user could intercept the username<br />
and password by simply sniffing the network with a tool like<br />
Wireshark.<br />
Example 2: Sending data with POST method through HTTPS<br />
Suppose that our web application uses the HTTPS protocol to<br />
encrypt the data we are sending (or at least for transmitting sensitive<br />
data like credentials). In this case, when logging on to the<br />
web application the header of our POST request would be similar<br />
to the following:<br />
POST https:/www.example.com:443/cgi-bin/login.cgi HTTP/1.1<br />
Host: www.example.com<br />
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 5.1; it;<br />
rv:1.8.1.14) Gecko/20080404<br />
Accept: text/xml,application/xml,application/xhtml+xml,text/html<br />
Accept-Language: it-it,it;q=0.8,en-us;q=0.5,en;q=0.3<br />
Accept-Encoding: gzip,deflate<br />
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.7<br />
Keep-Alive: 300<br />
Connection: keep-alive<br />
Referer: https:/www.example.com/cgi-bin/login.cgi<br />
Cookie: language=English;<br />
Content-Type: application/x-www-form-urlencoded<br />
Content-length: 50<br />
Command=Login&User=test&Pass=test<br />
We can see that the request is addressed to www.example.<br />
com:443/cgi-bin/login.cgi using the HTTPS protocol. This ensures<br />
that our credentials are sent using an encrypted channel<br />
and that the credentials are not readable by a malicious user using<br />
a sniffer.<br />
Example 3: sending data with POST method via HTTPS on a<br />
page reachable via HTTP<br />
Now, imagine having a web page reachable via HTTP and that<br />
only data sent from the authentication form are transmitted via<br />
HTTPS. This situation occurs, for example, when we are on a portal<br />
of a big company that offers various information and services<br />
that are publicly available, without identification, but the site<br />
also has a private section accessible from the home page when<br />
users log in. So when we try to log in, the header of our request<br />
will look like the following example:<br />
POST https:/www.example.com:443/login.do HTTP/1.1<br />
Host: www.example.com<br />
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 5.1; it;<br />
rv:1.8.1.14) Gecko/20080404<br />
Accept: text/xml,application/xml,application/xhtml+xml,text/html<br />
Accept-Language: it-it,it;q=0.8,en-us;q=0.5,en;q=0.3<br />
Accept-Encoding: gzip,deflate<br />
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.7<br />
Keep-Alive: 300<br />
Connection: keep-alive<br />
Referer: http:/www.example.com/homepage.do<br />
Cookie: SERVTIMSESSIONID=s2JyLkvDJ9ZhX3yr5BJ3DFLkdphH-<br />
0QNSJ3VQB6pLhjkW6F<br />
Content-Type: application/x-www-form-urlencoded<br />
Content-length: 45<br />
User=test&Pass=test&portal=ExamplePortal<br />
We can see that our request is addressed to www.example.<br />
com:443/login.do using HTTPS. But if we have a look at the Referer-header<br />
(the page from which we came), it is www.example.<br />
com/homepage.do and is accessible via simple HTTP. Although<br />
we are sending data via HTTPS, this deployment can allow SSL-<br />
Strip attacks (a type of Man-in-the-middle attack)<br />
Example 4: Sending data with GET method through HTTPS<br />
In this last example, suppose that the application transfers data<br />
using the GET method. This method should never be used in a<br />
form that transmits sensitive data such as username and password,<br />
because the data is displayed in clear text in the URL and<br />
this causes a whole set of security issues. For example, the URL<br />
that is requested is easily available from the server logs or from<br />
your browser history, which makes your sensitive data retrievable<br />
for unauthorized persons. So this example is purely demonstrative,<br />
but, in reality, it is strongly suggested to use the POST<br />
method instead.<br />
GET https: /www.example.com/success.html?user=test&-<br />
pass=test HTTP/1.1<br />
Host: www.example.com