4.0
1NSchAb
1NSchAb
- No tags were found...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
169<br />
Web Application Penetration Testing<br />
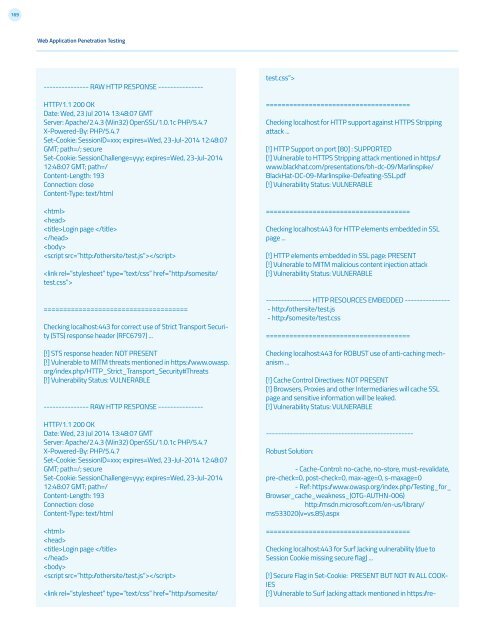
--------------- RAW HTTP RESPONSE ---------------<br />
HTTP/1.1 200 OK<br />
Date: Wed, 23 Jul 2014 13:48:07 GMT<br />
Server: Apache/2.4.3 (Win32) OpenSSL/1.0.1c PHP/5.4.7<br />
X-Powered-By: PHP/5.4.7<br />
Set-Cookie: SessionID=xxx; expires=Wed, 23-Jul-2014 12:48:07<br />
GMT; path=/; secure<br />
Set-Cookie: SessionChallenge=yyy; expires=Wed, 23-Jul-2014<br />
12:48:07 GMT; path=/<br />
Content-Length: 193<br />
Connection: close<br />
Content-Type: text/html<br />
<br />
<br />
Login page <br />
<br />
<br />
<br />
<br />
=====================================<br />
Checking localhost:443 for correct use of Strict Transport Security<br />
(STS) response header (RFC6797) ...<br />
[!] STS response header: NOT PRESENT<br />
[!] Vulnerable to MITM threats mentioned in https:/www.owasp.<br />
org/index.php/HTTP_Strict_Transport_Security#Threats<br />
[!] Vulnerability Status: VULNERABLE<br />
--------------- RAW HTTP RESPONSE ---------------<br />
HTTP/1.1 200 OK<br />
Date: Wed, 23 Jul 2014 13:48:07 GMT<br />
Server: Apache/2.4.3 (Win32) OpenSSL/1.0.1c PHP/5.4.7<br />
X-Powered-By: PHP/5.4.7<br />
Set-Cookie: SessionID=xxx; expires=Wed, 23-Jul-2014 12:48:07<br />
GMT; path=/; secure<br />
Set-Cookie: SessionChallenge=yyy; expires=Wed, 23-Jul-2014<br />
12:48:07 GMT; path=/<br />
Content-Length: 193<br />
Connection: close<br />
Content-Type: text/html<br />
<br />
<br />
Login page <br />
<br />
<br />
<br />
<br />
=====================================<br />
Checking localhost for HTTP support against HTTPS Stripping<br />
attack ...<br />
[!] HTTP Support on port [80] : SUPPORTED<br />
[!] Vulnerable to HTTPS Stripping attack mentioned in https:/<br />
www.blackhat.com/presentations/bh-dc-09/Marlinspike/<br />
BlackHat-DC-09-Marlinspike-Defeating-SSL.pdf<br />
[!] Vulnerability Status: VULNERABLE<br />
=====================================<br />
Checking localhost:443 for HTTP elements embedded in SSL<br />
page ...<br />
[!] HTTP elements embedded in SSL page: PRESENT<br />
[!] Vulnerable to MITM malicious content injection attack<br />
[!] Vulnerability Status: VULNERABLE<br />
--------------- HTTP RESOURCES EMBEDDED ---------------<br />
- http:/othersite/test.js<br />
- http:/somesite/test.css<br />
=====================================<br />
Checking localhost:443 for ROBUST use of anti-caching mechanism<br />
...<br />
[!] Cache Control Directives: NOT PRESENT<br />
[!] Browsers, Proxies and other Intermediaries will cache SSL<br />
page and sensitive information will be leaked.<br />
[!] Vulnerability Status: VULNERABLE<br />
-------------------------------------------------<br />
Robust Solution:<br />
- Cache-Control: no-cache, no-store, must-revalidate,<br />
pre-check=0, post-check=0, max-age=0, s-maxage=0<br />
- Ref: https:/www.owasp.org/index.php/Testing_for_<br />
Browser_cache_weakness_(OTG-AUTHN-006)<br />
http:/msdn.microsoft.com/en-us/library/<br />
ms533020(v=vs.85).aspx<br />
=====================================<br />
Checking localhost:443 for Surf Jacking vulnerability (due to<br />
Session Cookie missing secure flag) ...<br />
[!] Secure Flag in Set-Cookie: PRESENT BUT NOT IN ALL COOK-<br />
IES<br />
[!] Vulnerable to Surf Jacking attack mentioned in https:/re-