- Page 1: WorkSpace On-Demand 2.0 Feature for
- Page 4 and 5: Take Note! Before using this inform
- Page 6 and 7: Chapter 3. Installation and plannin
- Page 8 and 9: 5.6.2 Enabling network adapters on
- Page 10 and 11: How to get ITSO redbooks ..........
- Page 12 and 13: 41. Windows95Programmenu,beforecust
- Page 14 and 15: xii WorkSpace On-Demand 2.0 Feature
- Page 16 and 17: computer science from the Universit
- Page 18 and 19: Aidon Jennery IBM Network Computing
- Page 20 and 21: xviii WorkSpace On-Demand 2.0 Featu
- Page 22 and 23: Workspace On-Demand Manager Client
- Page 24 and 25: A secure, enterprise-targeted opera
- Page 26 and 27: will have its own response file con
- Page 28 and 29: Other versions of Windows 95 are no
- Page 30 and 31: Again, the more memory you have ava
- Page 32 and 33: 12 WorkSpace On-Demand 2.0 Feature
- Page 34 and 35: Workspace On-Demand Manager Client
- Page 36 and 37: For example, client-side graphics,
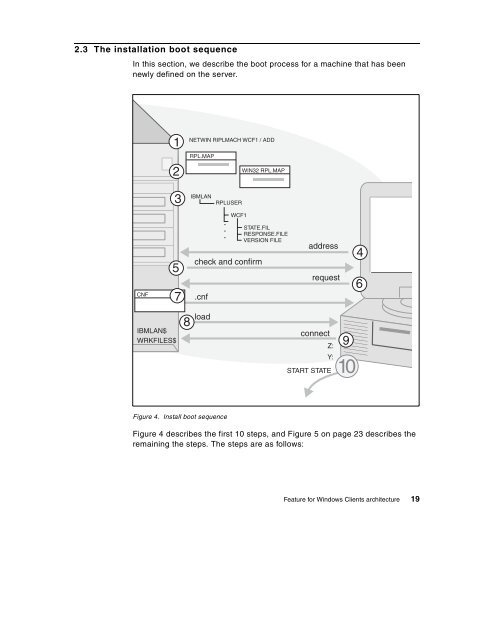
- Page 40 and 41: 1. The systems administrator define
- Page 42 and 43: machine_name represents the name of
- Page 44 and 45: 12.It then gets the primary partiti
- Page 46 and 47: 2.4 RPL control files the server re
- Page 48 and 49: The Workstation Record The workstat
- Page 50 and 51: The Server Record The server record
- Page 52 and 53: s defines the state of the remote I
- Page 54 and 55: Server record R_DTK_NDIS Workstatio
- Page 56 and 57: ; DOS Boot Block Configuration (IBM
- Page 58 and 59: Entry Description DRV A CNF file ma
- Page 60 and 61: contains. The only values supported
- Page 62 and 63: subdirectory. The clients subdirect
- Page 64 and 65: The functions that are required to
- Page 66 and 67: for storage. Hives can then be relo
- Page 68 and 69: x:\IBMLAN\REPL\IMPORT\SCRIPTS Figur
- Page 70 and 71: Windows User Profile already exists
- Page 72 and 73: DCDB directory. This is a batch fil
- Page 74 and 75: Command Line Interface NET.ACC and
- Page 76 and 77: 3.1.2 Multiple-server environments
- Page 78 and 79: The location selected for the user
- Page 80 and 81: File and Print Sharing Remote IPL S
- Page 82 and 83: Note We strongly recommend that you
- Page 84 and 85: Figure 17. Feature for Windows Clie
- Page 86 and 87: space on the drive should be at lea
- Page 88 and 89:
The default response file bbwfcid.r
- Page 90 and 91:
the WIN32APP subdirectory, unless y
- Page 92 and 93:
For more information about GETRPL a
- Page 94 and 95:
since the are some Year 2000 compla
- Page 96 and 97:
3.7 Initial testing 4. Open the IBM
- Page 98 and 99:
Note 3.8 Tivoli Management Agent (T
- Page 100 and 101:
3.9 Client performance At the botto
- Page 102 and 103:
Please consider the factors mention
- Page 104 and 105:
Install Application Figure 23. Appl
- Page 106 and 107:
Install Application Figure 24. Crea
- Page 108 and 109:
4.2 Application type The type of ap
- Page 110 and 111:
When selecting applications for the
- Page 112 and 113:
netwin riplmach nt40sp4 /add /mac:0
- Page 114 and 115:
Note To maintain security, store ap
- Page 116 and 117:
Windows NT or Windows 9X Sandbox Sa
- Page 118 and 119:
customizing StarOffice. To install
- Page 120 and 121:
4.3.4.3 Completing the application
- Page 122 and 123:
Note A Windows NT application packa
- Page 124 and 125:
The APPSTORE.INI file is in the \WI
- Page 126 and 127:
Note The Windows NT client image re
- Page 128 and 129:
appid directory, rename each file t
- Page 130 and 131:
If you have multiple RENFILE.BAT fi
- Page 132 and 133:
14.. Open the file LOGONCLT.BAT in
- Page 134 and 135:
16.In the LOGONCLT.BAT file, after
- Page 136 and 137:
In our StarOffice example, to add t
- Page 138 and 139:
directory and Client Application In
- Page 140 and 141:
primary domain controller, or remot
- Page 142 and 143:
The application packages must be ma
- Page 144 and 145:
4.7 Application commands The two ke
- Page 146 and 147:
Size Limitations on Windows 9x Due
- Page 148 and 149:
localpath Specifies a fully-qualifi
- Page 150 and 151:
Windows User Profile The Windows us
- Page 152 and 153:
following parameters must also be s
- Page 154 and 155:
=delete. For example: /PRINTER:prin
- Page 156 and 157:
TYPE{:WIN95 | WIN98 | WINNT} Specif
- Page 158 and 159:
[OptionalComponents] "Paint"=0 "Com
- Page 160 and 161:
Parameter values may not contain a
- Page 162 and 163:
winnt [/s:sourcepath] [/i:inf_file]
- Page 164 and 165:
Windows NT Workstation 4.0 retail v
- Page 166 and 167:
[version] signature="$Windows NT$"
- Page 168 and 169:
Table 14 describes the parameters.
- Page 170 and 171:
Switch Description /ig Allows setup
- Page 172 and 173:
em rename c:\windows\tasks\sa.dat s
- Page 174 and 175:
5.3 Summary chart You can choose to
- Page 176 and 177:
IBM PC750 machines, The machine con
- Page 178 and 179:
driver = d1,mga64.sys,mga64 dll = d
- Page 180 and 181:
3. Find the device ID for the drive
- Page 182 and 183:
Note The machine setup may not list
- Page 184 and 185:
1. The driver files for IBM EtherJe
- Page 186 and 187:
5.7.1 Windows 9x printing For Windo
- Page 188 and 189:
NT expects to find the printer driv
- Page 190 and 191:
TC = TCPIPParameters [TCPIPParamete
- Page 192 and 193:
WindowTitle=keystrokes The document
- Page 194 and 195:
C:\CRYSTAL\SCRIPTIT\SCRIPTIT.EXE c:
- Page 196 and 197:
(machinename represents the client
- Page 198 and 199:
the user runtime access to the appl
- Page 200 and 201:
the text that follows, we use the w
- Page 202 and 203:
Figure 37. Windows 95, Password Pro
- Page 204 and 205:
Figure 39. Windows 95 Display Prope
- Page 206 and 207:
C:\WINDOWS\Profiles\indrann\Start M
- Page 208 and 209:
9. Empty the recycle bin and clear
- Page 210 and 211:
10.Change directories to C:\. 11.Op
- Page 212 and 213:
Does Default User Policy exist? YES
- Page 214 and 215:
Policy Files A policy file is valid
- Page 216 and 217:
Figure 47. Policy template options
- Page 218 and 219:
When administering System Policies,
- Page 220 and 221:
6.4.6 Changing the Windows NT syste
- Page 222 and 223:
5. Start Microsoft Poledit. 6. In P
- Page 224 and 225:
Figure 49. Setting up a custom prog
- Page 226 and 227:
7.2 The Tivoli Management Framework
- Page 228 and 229:
7.4 The role of the TMA The Tivoli
- Page 230 and 231:
2. The endpoint manager selects the
- Page 232 and 233:
IBMLAN\RPL\W95\C\$TIVOLI for Window
- Page 234 and 235:
From the desktop: Select Control Pa
- Page 236 and 237:
environment is, by definition, a th
- Page 238 and 239:
The second key technology Citrix ha
- Page 240 and 241:
NetPC ICA PC PC RDP Windowsbased Te
- Page 242 and 243:
Application Architecture Target App
- Page 244 and 245:
easons as well as the need to suppo
- Page 246 and 247:
226 WorkSpace On-Demand 2.0 Feature
- Page 248 and 249:
3COM3C509B-Combo IBM LanStreamer PC
- Page 250 and 251:
3COM3C509B-Combo IBM LanStreamer PC
- Page 252 and 253:
abbreviations, REXX instructions ar
- Page 254 and 255:
234 WorkSpace On-Demand 2.0 Feature
- Page 256 and 257:
esponsibility and depends on the cu
- Page 258 and 259:
238 WorkSpace On-Demand 2.0 Feature
- Page 260 and 261:
240 RS/6000 SP Software Maintenance
- Page 262 and 263:
IBM Redbook Fax order form Please s
- Page 264 and 265:
esource’s alias, without regard t
- Page 266 and 267:
systems without the need to pass th
- Page 268 and 269:
248 WorkSpace On-Demand 2.0 Feature
- Page 270 and 271:
Customized desktops 17 Customizing
- Page 272 and 273:
New desktops 181 NEWFILE.LST 102 NT
- Page 274 and 275:
WorkSpace On-Demand 6 Application M
- Page 276:
SG24-5396-00 PrintedintheU.S.A. Wor