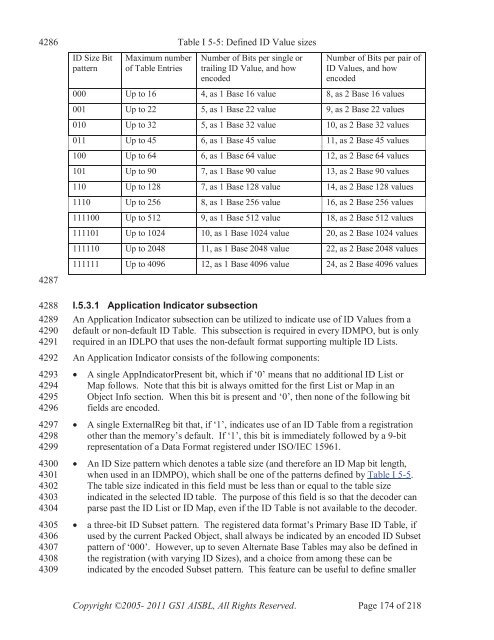
428642874288428942904291429242934294429542964297429842994300430143024303430443054306430743084309ID Size BitpatternMaximum numberof Table EntriesTable I 5-5: Defined ID Value sizesNumber of Bits per single ortrailing ID Value, and howencodedNumber of Bits per pair ofID Values, and howencoded000 Up to 16 4, as 1 Base 16 value 8, as 2 Base 16 values001 Up to 22 5, as 1 Base 22 value 9, as 2 Base 22 values010 Up to 32 5, as 1 Base 32 value 10, as 2 Base 32 values011 Up to 45 6, as 1 Base 45 value 11, as 2 Base 45 values100 Up to 64 6, as 1 Base 64 value 12, as 2 Base 64 values101 Up to 90 7, as 1 Base 90 value 13, as 2 Base 90 values110 Up to 128 7, as 1 Base 128 value 14, as 2 Base 128 values1110 Up to 256 8, as 1 Base 256 value 16, as 2 Base 256 values111100 Up to 512 9, as 1 Base 512 value 18, as 2 Base 512 values111101 Up to 1024 10, as 1 Base 1024 value 20, as 2 Base 1024 values111110 Up to 2048 11, as 1 Base 2048 value 22, as 2 Base 2048 values111111 Up to 4096 12, as 1 Base 4096 value 24, as 2 Base 4096 valuesI.5.3.1 Application Indicator subsectionAn Application Indicator subsection can be utilized to indicate use of ID Values from adefault or non-default ID Table. This subsection is required in every IDMPO, but is onlyrequired in an IDLPO that uses the non-default format supporting multiple ID Lists.An Application Indicator consists of the following components:A single AppIndicatorPresent bit, which if ‘0’ means that no additional ID List orMap follows. Note that this bit is always omitted for the first List or Map in anObject Info section. When this bit is present and ‘0’, then none of the following bitfields are encoded.A single ExternalReg bit that, if ‘1’, indicates use of an ID Table from a registrationother than the memory’s default. If ‘1’, this bit is immediately followed by a 9-bitrepresentation of a <strong>Data</strong> Format registered under ISO/IEC 15961.An ID Size pattern which denotes a table size (and therefore an ID Map bit length,when used in an IDMPO), which shall be one of the patterns defined by Table I 5-5.The table size indicated in this field must be less than or equal to the table sizeindicated in the selected ID table. The purpose of this field is so that the decoder canparse past the ID List or ID Map, even if the ID Table is not available to the decoder.a three-bit ID Subset pattern. The registered data format’s Primary Base ID Table, ifused by the current Packed Object, shall always be indicated by an encoded ID Subsetpattern of ‘000’. However, up to seven Alternate Base Tables may also be defined inthe registration (with varying ID Sizes), and a choice from among these can beindicated by the encoded Subset pattern. This feature can be useful to define smallerCopyright ©2005- 2011 <strong>GS1</strong> AISBL, All Rights Reserved. Page 174 of 218
431043114312431343144315431643174318431943204321432243234324432543264327432843294330433143324333433443354336433743384339434043414342434343444345434643474348434943504351sector-specific or application-specific subsets of a full data system, thus substantiallyreducing the size of the encoded ID Map.I.5.3.2 Full/Restricted Use bitsWhen contemplating the use of new ID Table registrations, or registrations for externaldata systems, application designers may utilize a “restricted use” encoding option thatadds some overhead to a Packed Object but in exchange results in a format that can befully decoded by receiving systems not in possession of the new or external ID table.With the exception of a IDLPO using the default Object Info format, one Full/RestrictedUse bit is encoded immediately after each ID table is represented in the ID Map sectionor ID Lists section of a <strong>Data</strong> or Directory Packed Object. In a Directory Packed object,this bit shall always be set to '0' and its value ignored. If an encoder wishes to utilize the“restricted use” option in an IDLPO, it shall preface the IDLPO with a Format Flagssection invoking the non-default Object Info format.If a “Full/Restricted Use” bit is ‘0’ then the encoding of data strings from thecorresponding registered ID Table makes full use of the ID Table’s IDstring andFormatString information. If the bit is ‘1’, then this signifies that some encodingoverhead was added to the Secondary ID section and (in the case of Packed-Objectcompaction) the Aux Format section, so that a decoder without access to the table cannonetheless output OIDs and data from the Packed Object according to the schemespecified in J.4.1. Specifically, a Full/Restricted Use bit set to ‘1’ indicates that: for each encoded ID Value, the encoder added an EBV-3 indicator to the SecondaryID section, to indicate how many Secondary ID bits were invoked by that ID Value.If the EBV-3 is nonzero, then the Secondary ID bits (as indicated by the table entry)immediately follow, followed in turn by another EBV-3, until the entire list of IDValues has been represented. the encoder did not take advantage of the information from the referenced table’sFormatString column. Instead, corresponding to each ID Value, the encoder insertedan EBV-3 into the Aux Format section, indicating the number of discrete data stringlengths invoked by the ID Value (which could be more than one due to combinationsand/or optional components), followed by the indicated number of string lengths,each length encoded as though there were no FormatString in the ID table. All dataitems were encoded in the A/N subsection of the <strong>Data</strong> section.I.5.4 ID Values representation in an ID Value-list Packed ObjectEach ID Value is represented within an IDLPO on a list of bit fields; the number of bitfields on the list is determined from the NumberOfIDs field (see Table I 5-1). Each IDValue bit field’s length is in the range of four to eleven bits, depending on the size of theBase Table index it represents. In the optional non-default format for an IDLPO’s ObjectInfo section, a single Packed Object may contain multiple ID List subsections, eachreferencing a different ID Table. In this non-default format, each ID List subsectionconsists of an Application Indicator subsection (which terminates the ID Lists, if it beginswith a ‘0’ bit), followed by an EBV-3 NumberOfIDs, an ID List, and a Full/RestrictedUse flag.Copyright ©2005- 2011 <strong>GS1</strong> AISBL, All Rights Reserved. Page 175 of 218