CCNA Complete Guide 2nd Edition.pdf - Cisco Learning Home
CCNA Complete Guide 2nd Edition.pdf - Cisco Learning Home
CCNA Complete Guide 2nd Edition.pdf - Cisco Learning Home
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
Wireless Security<br />
- Organizations that are not deploying WLANs fast enough often find their employees take the<br />
matter themselves and deploy unauthorized access points and WLANs – rogue access points,<br />
which would create significant security breaches in the network infrastructure.<br />
- Wireless eavesdropping, war driving hacking, and rogue access points (unauthorized access<br />
points that allow unauthorized access to a network) are the main security concerns of WLANs.<br />
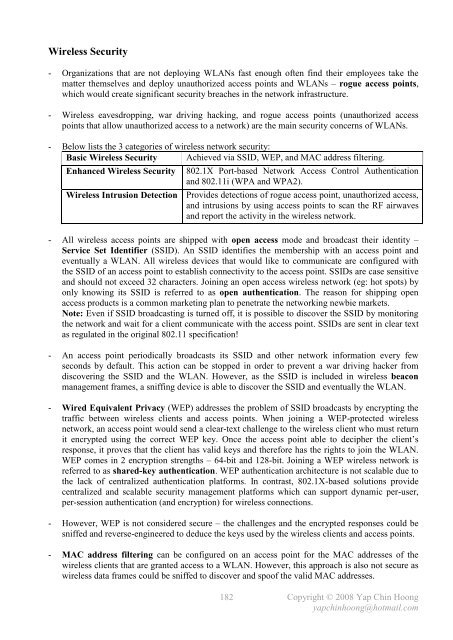
- Below lists the 3 categories of wireless network security:<br />
Basic Wireless Security Achieved via SSID, WEP, and MAC address filtering.<br />
Enhanced Wireless Security 802.1X Port-based Network Access Control Authentication<br />
and 802.11i (WPA and WPA2).<br />
Wireless Intrusion Detection Provides detections of rogue access point, unauthorized access,<br />
and intrusions by using access points to scan the RF airwaves<br />
and report the activity in the wireless network.<br />
- All wireless access points are shipped with open access mode and broadcast their identity –<br />
Service Set Identifier (SSID). An SSID identifies the membership with an access point and<br />
eventually a WLAN. All wireless devices that would like to communicate are configured with<br />
the SSID of an access point to establish connectivity to the access point. SSIDs are case sensitive<br />
and should not exceed 32 characters. Joining an open access wireless network (eg: hot spots) by<br />
only knowing its SSID is referred to as open authentication. The reason for shipping open<br />
access products is a common marketing plan to penetrate the networking newbie markets.<br />
Note: Even if SSID broadcasting is turned off, it is possible to discover the SSID by monitoring<br />
the network and wait for a client communicate with the access point. SSIDs are sent in clear text<br />
as regulated in the original 802.11 specification!<br />
- An access point periodically broadcasts its SSID and other network information every few<br />
seconds by default. This action can be stopped in order to prevent a war driving hacker from<br />
discovering the SSID and the WLAN. However, as the SSID is included in wireless beacon<br />
management frames, a sniffing device is able to discover the SSID and eventually the WLAN.<br />
- Wired Equivalent Privacy (WEP) addresses the problem of SSID broadcasts by encrypting the<br />
traffic between wireless clients and access points. When joining a WEP-protected wireless<br />
network, an access point would send a clear-text challenge to the wireless client who must return<br />
it encrypted using the correct WEP key. Once the access point able to decipher the client’s<br />
response, it proves that the client has valid keys and therefore has the rights to join the WLAN.<br />
WEP comes in 2 encryption strengths – 64-bit and 128-bit. Joining a WEP wireless network is<br />
referred to as shared-key authentication. WEP authentication architecture is not scalable due to<br />
the lack of centralized authentication platforms. In contrast, 802.1X-based solutions provide<br />
centralized and scalable security management platforms which can support dynamic per-user,<br />
per-session authentication (and encryption) for wireless connections.<br />
- However, WEP is not considered secure – the challenges and the encrypted responses could be<br />
sniffed and reverse-engineered to deduce the keys used by the wireless clients and access points.<br />
- MAC address filtering can be configured on an access point for the MAC addresses of the<br />
wireless clients that are granted access to a WLAN. However, this approach is also not secure as<br />
wireless data frames could be sniffed to discover and spoof the valid MAC addresses.<br />
182<br />
Copyright © 2008 Yap Chin Hoong<br />
yapchinhoong@hotmail.com