CCNA Complete Guide 2nd Edition.pdf - Cisco Learning Home
CCNA Complete Guide 2nd Edition.pdf - Cisco Learning Home
CCNA Complete Guide 2nd Edition.pdf - Cisco Learning Home
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
- IPsec-based VPN is comprised of 2 parts – Internet Key Exchange (IKE) protocol and IPsec<br />
security protocols – Authentication Header (AH) and Encapsulating Security Payload (ESP).<br />
Below describes the flow of IPsec events:<br />
i) IKE Phase 1: IKE Security Negotiation – IKE negotiates how to protect IKE by<br />
establishing an authenticated and secure channel between 2 IKE peers called the<br />
IKE Security Association. IKE Phase 1 is consists of Main Mode or Aggressive Mode.<br />
The peer that initiates the session will propose or offer at least one or more configured<br />
ISAKMP policies which specify a combination of encryption algorithm, hash algorithm,<br />
authentication type, Diffie-Hellman group, and the lifetime. The remote peer will then try<br />
to find a matching configured policy that has the same parameters as the one being sent<br />
by its peer. If no matching policy is found, IKE will terminate the negotiation. If a policy<br />
is mutually agreed upon, IKE will complete the negotiation process and an ISAKMP SA<br />
will be created. Additionally, peers in an IPsec session must authenticate themselves<br />
among each other during IKE Phase 1 Main Mode exchange before IKE can proceed.<br />
ii) IKE Phase 2: IPsec Security Negotiation – IKE negotiates how to protect IPsec by<br />
negotiating the IPsec security associations (SAs) and generating the keys for IPsec.<br />
IKE Phase 2 negotiation is done in only 1 mode – Quick Mode. The peer that initiates<br />
the session will propose or offer at least one or more configured transforms which specify<br />
a combination of authentication and/or encryption algorithm. The remote peer will then<br />
try to find a matching configured transform that has the same parameters as the one being<br />
sent by its peer. If no matching transform is found, IKE will terminate negotiation and an<br />
IPsec VPN will not be established. If a policy is mutually agreed upon, IKE will complete<br />
the negotiation process and an IPsec SA will be created.<br />
iii) IPsec transfers the actual data in the VPN tunnel using the authentication and encryption<br />
methods agreed upon the IKE negotiation process.<br />
- Internet Key Exchange (IKE) allows 2 VPN endpoints verify the identity of each other<br />
(using pre-shared keys or RSA) in IKE Phase 1, and negotiate the methods (security policies) for<br />
secured data transmission in IKE Phase 2. IKE manages VPN connections by defining a set of<br />
Security Associations (SAs) for each connection. Each SA has its own SAID.<br />
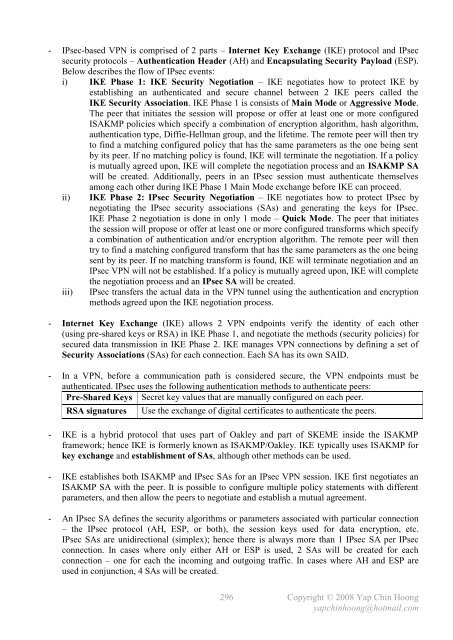
- In a VPN, before a communication path is considered secure, the VPN endpoints must be<br />
authenticated. IPsec uses the following authentication methods to authenticate peers:<br />
Pre-Shared Keys Secret key values that are manually configured on each peer.<br />
RSA signatures Use the exchange of digital certificates to authenticate the peers.<br />
- IKE is a hybrid protocol that uses part of Oakley and part of SKEME inside the ISAKMP<br />
framework; hence IKE is formerly known as ISAKMP/Oakley. IKE typically uses ISAKMP for<br />
key exchange and establishment of SAs, although other methods can be used.<br />
- IKE establishes both ISAKMP and IPsec SAs for an IPsec VPN session. IKE first negotiates an<br />
ISAKMP SA with the peer. It is possible to configure multiple policy statements with different<br />
parameters, and then allow the peers to negotiate and establish a mutual agreement.<br />
- An IPsec SA defines the security algorithms or parameters associated with particular connection<br />
– the IPsec protocol (AH, ESP, or both), the session keys used for data encryption, etc.<br />
IPsec SAs are unidirectional (simplex); hence there is always more than 1 IPsec SA per IPsec<br />
connection. In cases where only either AH or ESP is used, 2 SAs will be created for each<br />
connection – one for each the incoming and outgoing traffic. In cases where AH and ESP are<br />
used in conjunction, 4 SAs will be created.<br />
296<br />
Copyright © 2008 Yap Chin Hoong<br />
yapchinhoong@hotmail.com