Intelligent Transport Systems - Telenor
Intelligent Transport Systems - Telenor
Intelligent Transport Systems - Telenor
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
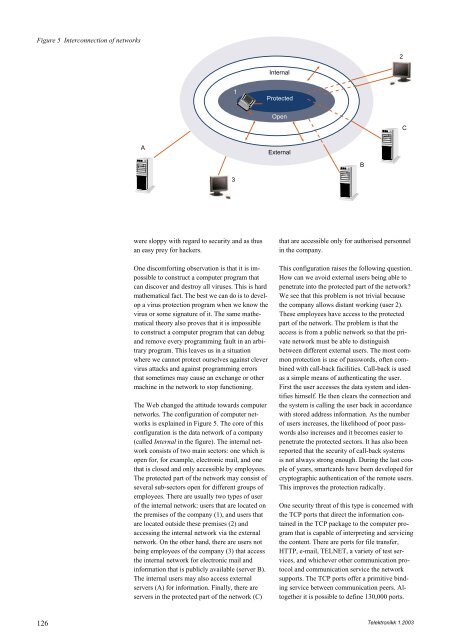
Figure 5 Interconnection of networks<br />
126<br />
A<br />
were sloppy with regard to security and as thus<br />
an easy prey for hackers.<br />
One discomforting observation is that it is impossible<br />
to construct a computer program that<br />
can discover and destroy all viruses. This is hard<br />
mathematical fact. The best we can do is to develop<br />
a virus protection program when we know the<br />
virus or some signature of it. The same mathematical<br />
theory also proves that it is impossible<br />
to construct a computer program that can debug<br />
and remove every programming fault in an arbitrary<br />
program. This leaves us in a situation<br />
where we cannot protect ourselves against clever<br />
virus attacks and against programming errors<br />
that sometimes may cause an exchange or other<br />
machine in the network to stop functioning.<br />
The Web changed the attitude towards computer<br />
networks. The configuration of computer networks<br />
is explained in Figure 5. The core of this<br />
configuration is the data network of a company<br />
(called Internal in the figure). The internal network<br />
consists of two main sectors: one which is<br />
open for, for example, electronic mail, and one<br />
that is closed and only accessible by employees.<br />
The protected part of the network may consist of<br />
several sub-sectors open for different groups of<br />
employees. There are usually two types of user<br />
of the internal network: users that are located on<br />
the premises of the company (1), and users that<br />
are located outside these premises (2) and<br />
accessing the internal network via the external<br />
network. On the other hand, there are users not<br />
being employees of the company (3) that access<br />
the internal network for electronic mail and<br />
information that is publicly available (server B).<br />
The internal users may also access external<br />
servers (A) for information. Finally, there are<br />
servers in the protected part of the network (C)<br />
1<br />
3<br />
Internal<br />
Protected<br />
Open<br />
External<br />
that are accessible only for authorised personnel<br />
in the company.<br />
This configuration raises the following question.<br />
How can we avoid external users being able to<br />
penetrate into the protected part of the network?<br />
We see that this problem is not trivial because<br />
the company allows distant working (user 2).<br />
These employees have access to the protected<br />
part of the network. The problem is that the<br />
access is from a public network so that the private<br />
network must be able to distinguish<br />
between different external users. The most common<br />
protection is use of passwords, often combined<br />
with call-back facilities. Call-back is used<br />
as a simple means of authenticating the user.<br />
First the user accesses the data system and identifies<br />
himself. He then clears the connection and<br />
the system is calling the user back in accordance<br />
with stored address information. As the number<br />
of users increases, the likelihood of poor passwords<br />
also increases and it becomes easier to<br />
penetrate the protected sectors. It has also been<br />
reported that the security of call-back systems<br />
is not always strong enough. During the last couple<br />
of years, smartcards have been developed for<br />
cryptographic authentication of the remote users.<br />
This improves the protection radically.<br />
One security threat of this type is concerned with<br />
the TCP ports that direct the information contained<br />
in the TCP package to the computer program<br />
that is capable of interpreting and servicing<br />
the content. There are ports for file transfer,<br />
HTTP, e-mail, TELNET, a variety of test services,<br />
and whichever other communication protocol<br />
and communication service the network<br />
supports. The TCP ports offer a primitive binding<br />
service between communication peers. Altogether<br />
it is possible to define 130,000 ports.<br />
B<br />
2<br />
C<br />
Telektronikk 1.2003