VGB POWERTECH 7 (2021) - International Journal for Generation and Storage of Electricity and Heat
VGB PowerTech - International Journal for Generation and Storage of Electricity and Heat. Issue 7 (2021). Technical Journal of the VGB PowerTech Association. Energy is us! Optimisation of power plants. Thermal waste utilisation.
VGB PowerTech - International Journal for Generation and Storage of Electricity and Heat. Issue 7 (2021).
Technical Journal of the VGB PowerTech Association. Energy is us!
Optimisation of power plants. Thermal waste utilisation.
- No tags were found...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Digital trans<strong>for</strong>mation <strong>of</strong> the coal sector <strong>VGB</strong> PowerTech 7 l <strong>2021</strong><br />
Present<br />
<strong>Electricity</strong>, produced by a<br />
central power plant, flows<br />
one way to customers<br />
Sub stations convert<br />
high voltage to<br />
lower voltage<br />
Future<br />
<strong>Electricity</strong>, produced by a<br />
central power plant, wind<br />
turbines <strong>and</strong> solar panels,<br />
flows to customers<br />
<strong>Electricity</strong> is stored<br />
in utility batteries<br />
Industrial<br />
customer<br />
Industrial cutomers both<br />
consume <strong>and</strong> produce electricity<br />
lndustral customers commumcate usage<br />
in<strong>for</strong>mation back to the power provider<br />
<strong>Electricity</strong> is stored in utility batteries<br />
Residential <strong>and</strong><br />
business customers<br />
commumcate usage<br />
m<strong>for</strong>mation back to<br />
the power provider<br />
Smart appliances, electric<br />
cars <strong>and</strong> street lights are<br />
some <strong>of</strong> the devices that<br />
will communicate to the<br />
power provider<br />
Business<br />
customer<br />
Residential<br />
customer<br />
Residential <strong>and</strong> business customers both<br />
consume <strong>and</strong> produce electricity using<br />
solar panels <strong>and</strong> wind turbines<br />
<strong>Electricity</strong> is stored<br />
in batteries<br />
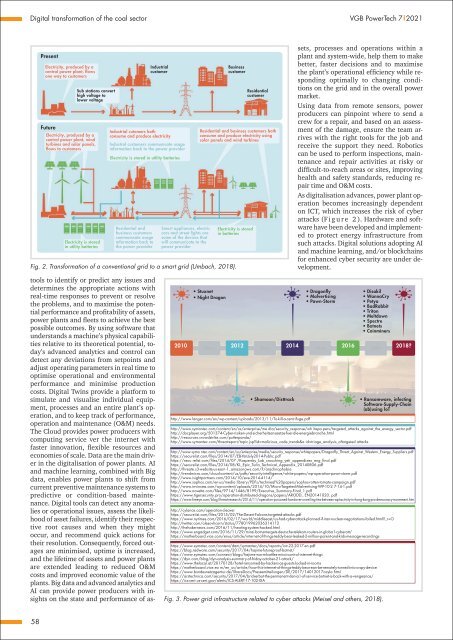
Fig. 2. Trans<strong>for</strong>mation <strong>of</strong> a conventional grid to a smart grid (Umbach, 2018).<br />
tools to identify or predict any issues <strong>and</strong><br />
determines the appropriate actions with<br />
real-time responses to prevent or resolve<br />
the problems, <strong>and</strong> to maximise the potential<br />
per<strong>for</strong>mance <strong>and</strong> pr<strong>of</strong>itability <strong>of</strong> assets,<br />
power plants <strong>and</strong> fleets to achieve the best<br />
possible outcomes. By using s<strong>of</strong>tware that<br />
underst<strong>and</strong>s a machine’s physical capabilities<br />
relative to its theoretical potential, today’s<br />
advanced analytics <strong>and</strong> control can<br />
detect any deviations from setpoints <strong>and</strong><br />
adjust operating parameters in real time to<br />
optimise operational <strong>and</strong> environmental<br />
per<strong>for</strong>mance <strong>and</strong> minimise production<br />
costs. Digital Twins provide a plat<strong>for</strong>m to<br />
simulate <strong>and</strong> visualise individual equipment,<br />
processes <strong>and</strong> an entire plant’s operation,<br />
<strong>and</strong> to keep track <strong>of</strong> per<strong>for</strong>mance,<br />
operation <strong>and</strong> maintenance (O&M) needs.<br />
The Cloud provides power producers with<br />
computing service ver the internet with<br />
faster innovation, flexible resources <strong>and</strong><br />
economies <strong>of</strong> scale. Data are the main driver<br />
in the digitalisation <strong>of</strong> power plants. AI<br />
<strong>and</strong> machine learning, combined with Big<br />
data, enables power plants to shift from<br />
current preventive maintenance systems to<br />
predictive or condition-based maintenance.<br />
Digital tools can detect any anomalies<br />
or operational issues, assess the likelihood<br />
<strong>of</strong> asset failures, identify their respective<br />
root causes <strong>and</strong> when they might<br />
occur, <strong>and</strong> recommend quick actions <strong>for</strong><br />
their resolution. Consequently, <strong>for</strong>ced outages<br />
are minimised, uptime is increased,<br />
<strong>and</strong> the lifetime <strong>of</strong> assets <strong>and</strong> power plants<br />
are extended leading to reduced O&M<br />
costs <strong>and</strong> improved economic value <strong>of</strong> the<br />
plants. Big data <strong>and</strong> advanced analytics <strong>and</strong><br />
AI can provide power producers with insights<br />
on the state <strong>and</strong> per<strong>for</strong>mance <strong>of</strong> assets,<br />
processes <strong>and</strong> operations within a<br />
plant <strong>and</strong> system-wide, help them to make<br />
better, faster decisions <strong>and</strong> to maximise<br />
the plant’s operational efficiency while responding<br />
optimally to changing conditions<br />
on the grid <strong>and</strong> in the overall power<br />
market.<br />
Using data from remote sensors, power<br />
producers can pinpoint where to send a<br />
crew <strong>for</strong> a repair, <strong>and</strong> based on an assessment<br />
<strong>of</strong> the damage, ensure the team arrives<br />
with the right tools <strong>for</strong> the job <strong>and</strong><br />
receive the support they need. Robotics<br />
can be used to per<strong>for</strong>m inspections, maintenance<br />
<strong>and</strong> repair activities at risky or<br />
difficult-to-reach areas or sites, improving<br />
health <strong>and</strong> safety st<strong>and</strong>ards, reducing repair<br />
time <strong>and</strong> O&M costs.<br />
As digitalisation advances, power plant operation<br />
becomes increasingly dependent<br />
on ICT, which increases the risk <strong>of</strong> cyber<br />
attacks (F i g u r e 2 ). Hardware <strong>and</strong> s<strong>of</strong>tware<br />
have been developed <strong>and</strong> implemented<br />
to protect energy infrastructure from<br />
such attacks. Digital solutions adopting AI<br />
<strong>and</strong> machine learning, <strong>and</strong>/or blockchains<br />
<strong>for</strong> enhanced cyber security are under development.<br />
• Stuxnet<br />
• Night Dragon<br />
http://www.langer.com/en/wp-content/uploads/2013/11/To-kill-a-centrifuge.pdf<br />
• Dragonfly<br />
• Malvertising<br />
• Pawn-Storm<br />
• Disakil<br />
• WannaCry<br />
• Petya<br />
• BadRabbit<br />
• Triton<br />
• Meltdown<br />
• Spectre<br />
• Botnets<br />
• Coinminers<br />
2010 2012 2014<br />
2016<br />
2018?<br />
• Shamoon/Disttrack<br />
http://www.symantec.com/content/en/us/enterprise/me dia/security_response/wh itepa pers/targeted_attacks_against_the_energy_sector.pdf<br />
http://docplayer.org/501374-Cyber-risiken-und-sicherheitsansaetze-fuer-die-energiebranche.html<br />
http://resources.crowdstrike.com/putterp<strong>and</strong>a/<br />
http://www.symantec.com/threatreport/topic.jsp?id=malicious_code_trends&a id=triage_analysis_<strong>of</strong>targeted attacks<br />
http://www.syma ntec.com/content/en/us/enterprise/media/security_response/whitepapers/Dragonfly_Threat_Against_Western_Energy_Suppliers.pdf<br />
https://securelist.com/files/2014/07/EB-YetiJuly2014-Public.pdf<br />
https://secu relist.com/files/2014/07 /Kaspersky_Lab_crouching_yeti_appendixex_eng_final.pdf<br />
https://securelist.com/files/2014/08/KL_Epic_Turla_TechnicaI_Appendix_20140806.pdf<br />
http://threate.s3-website-us-east -1_amazonaws.com/?/arachnophobia<br />
http://trendmicro.com/cloud-content/us/pdfs/security-intelligence/white-papers/wp-operation-pawn-storm.pdf<br />
http://www.isightpartners.com/2014/10/eve-2014-4114/<br />
http://www.sophos.com/en-us/media library/PDFs/technieal%20papers/sophos-rotten-tomato-campaign.pdf<br />
http://www.invincea.com/wp-content/uploads/2014/10/Micro-Targeted-Malvertising-WP-10-2 7-14-1.pdf<br />
http://www.novetta.com/files/9714/1446/8199/Executive_Summary-Final_1.pdf<br />
https://www.tigersecurity.pro/operation-distributed-dragons/papers/ARODD_ EN20141020. pdf<br />
https://www.fireeye.com/blog/threat-research/2014/11/operation-poisoned-h<strong>and</strong>over-unveiling-ties-between-apt-activity-in-hong-kong-pro-democracy-movement.htm<br />
http://cylance.cam/operation-cleaver<br />
https://secureiist.com/files/2015/02/The-Desert-FaIcons-targeted-attacks.pdf<br />
https://www.nytimes.com/2016/02/17/world/middleeast/us-had-cyberattack-planned-if-iran-nuclear-negotiations-failed.html?_r=O<br />
http://twitter.com/olesovhcorn/status/778019962036314112<br />
http://thehakernews.com/2016/11/heating-system-hacked.html<br />
https://www.engadget.com/2016/11/29/mirai-botnet-tergets-deutsche-telekom-routers-in-globa1-cyberatt/<br />
https://motherboard.vice.com/enus/article/internet-<strong>of</strong>-things-teddy-bear-leaked-2-million-parent-<strong>and</strong>-kids-message-recordings<br />
https://www.symatec.com/content/dam/symantec/docs/reports/istr-22-2017-en.pdf<br />
https://blog.radware.com/security/2017/04/hajime-futurepro<strong>of</strong>-botnet/<br />
https://www.symatec.com/connect/blogs/hajime-worm-battles-mirai-control-internet-things<br />
https://dyn.com/blog/dyn-analysis-summary-<strong>of</strong>-friday-october-21-attack/<br />
https://www.thelocal.at/20170128/hotel-ransomed-by-hackers-as-guests-locked-in-rooms<br />
https://motherboard.vice.eo m/en_us/article/how-this-internet-<strong>of</strong>-things-teddy-bear-ean-be-remotely-turned-into-a-spy-device<br />
https://www.bundesnetzagentur.de/ShareDocs/Pressemitteilungen/DE/2017/14012017cayla.html<br />
https://arstechnica.com/security/2017/04/brickerbot-the-permanent-denia1-<strong>of</strong>-service-botnet-is-back-with-a-vengeance/<br />
https://ics-cert.us-cert.gov/alerts/ICS-ALERT-17-102-0IA<br />
Fig. 3. Power grid infrastructure related to cyber attacks (Meisel <strong>and</strong> others, 2018).<br />
• Ransomware, infecting<br />
S<strong>of</strong>tware-Supply-Chain<br />
(ab)using loT<br />
58