Web Gateway 7.1.5 Product Guide - McAfee
Web Gateway 7.1.5 Product Guide - McAfee
Web Gateway 7.1.5 Product Guide - McAfee
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
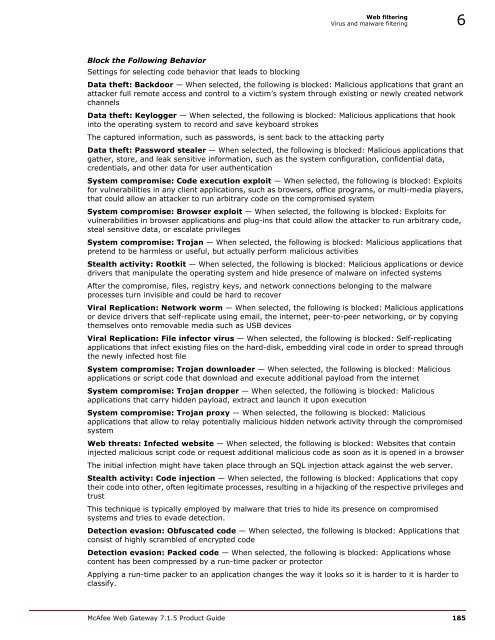
<strong>Web</strong> filtering<br />
Virus and malware filtering 6<br />
Block the Following Behavior<br />
Settings for selecting code behavior that leads to blocking<br />
Data theft: Backdoor — When selected, the following is blocked: Malicious applications that grant an<br />
attacker full remote access and control to a victim’s system through existing or newly created network<br />
channels<br />
Data theft: Keylogger — When selected, the following is blocked: Malicious applications that hook<br />
into the operating system to record and save keyboard strokes<br />
The captured information, such as passwords, is sent back to the attacking party<br />
Data theft: Password stealer — When selected, the following is blocked: Malicious applications that<br />
gather, store, and leak sensitive information, such as the system configuration, confidential data,<br />
credentials, and other data for user authentication<br />
System compromise: Code execution exploit — When selected, the following is blocked: Exploits<br />
for vulnerabilities in any client applications, such as browsers, office programs, or multi-media players,<br />
that could allow an attacker to run arbitrary code on the compromised system<br />
System compromise: Browser exploit — When selected, the following is blocked: Exploits for<br />
vulnerabilities in browser applications and plug-ins that could allow the attacker to run arbitrary code,<br />
steal sensitive data, or escalate privileges<br />
System compromise: Trojan — When selected, the following is blocked: Malicious applications that<br />
pretend to be harmless or useful, but actually perform malicious activities<br />
Stealth activity: Rootkit — When selected, the following is blocked: Malicious applications or device<br />
drivers that manipulate the operating system and hide presence of malware on infected systems<br />
After the compromise, files, registry keys, and network connections belonging to the malware<br />
processes turn invisible and could be hard to recover<br />
Viral Replication: Network worm — When selected, the following is blocked: Malicious applications<br />
or device drivers that self-replicate using email, the internet, peer-to-peer networking, or by copying<br />
themselves onto removable media such as USB devices<br />
Viral Replication: File infector virus — When selected, the following is blocked: Self-replicating<br />
applications that infect existing files on the hard-disk, embedding viral code in order to spread through<br />
the newly infected host file<br />
System compromise: Trojan downloader — When selected, the following is blocked: Malicious<br />
applications or script code that download and execute additional payload from the internet<br />
System compromise: Trojan dropper — When selected, the following is blocked: Malicious<br />
applications that carry hidden payload, extract and launch it upon execution<br />
System compromise: Trojan proxy — When selected, the following is blocked: Malicious<br />
applications that allow to relay potentially malicious hidden network activity through the compromised<br />
system<br />
<strong>Web</strong> threats: Infected website — When selected, the following is blocked: <strong>Web</strong>sites that contain<br />
injected malicious script code or request additional malicious code as soon as it is opened in a browser<br />
The initial infection might have taken place through an SQL injection attack against the web server.<br />
Stealth activity: Code injection — When selected, the following is blocked: Applications that copy<br />
their code into other, often legitimate processes, resulting in a hijacking of the respective privileges and<br />
trust<br />
This technique is typically employed by malware that tries to hide its presence on compromised<br />
systems and tries to evade detection.<br />
Detection evasion: Obfuscated code — When selected, the following is blocked: Applications that<br />
consist of highly scrambled of encrypted code<br />
Detection evasion: Packed code — When selected, the following is blocked: Applications whose<br />
content has been compressed by a run-time packer or protector<br />
Applying a run-time packer to an application changes the way it looks so it is harder to it is harder to<br />
classify.<br />
<strong>McAfee</strong> <strong>Web</strong> <strong>Gateway</strong> <strong>7.1.5</strong> <strong>Product</strong> <strong>Guide</strong> 185