MPED-X-Routing-Tender20080721 - Madhya Pradesh State Excise
MPED-X-Routing-Tender20080721 - Madhya Pradesh State Excise
MPED-X-Routing-Tender20080721 - Madhya Pradesh State Excise
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
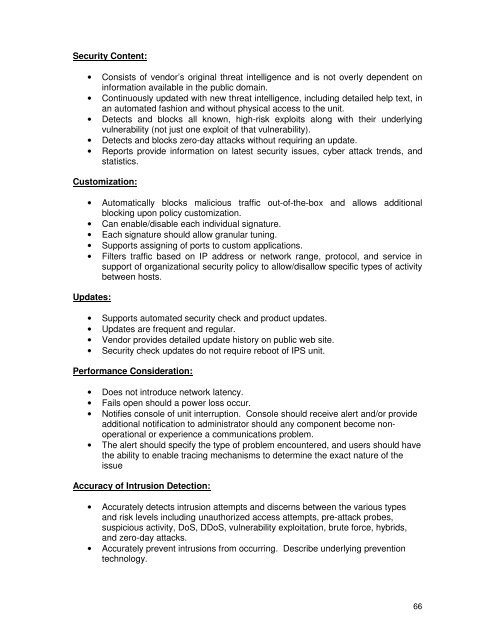
Security Content:<br />
• Consists of vendor’s original threat intelligence and is not overly dependent on<br />
information available in the public domain.<br />
• Continuously updated with new threat intelligence, including detailed help text, in<br />
an automated fashion and without physical access to the unit.<br />
• Detects and blocks all known, high-risk exploits along with their underlying<br />
vulnerability (not just one exploit of that vulnerability).<br />
• Detects and blocks zero-day attacks without requiring an update.<br />
• Reports provide information on latest security issues, cyber attack trends, and<br />
statistics.<br />
Customization:<br />
• Automatically blocks malicious traffic out-of-the-box and allows additional<br />
blocking upon policy customization.<br />
• Can enable/disable each individual signature.<br />
• Each signature should allow granular tuning.<br />
• Supports assigning of ports to custom applications.<br />
• Filters traffic based on IP address or network range, protocol, and service in<br />
support of organizational security policy to allow/disallow specific types of activity<br />
between hosts.<br />
Updates:<br />
• Supports automated security check and product updates.<br />
• Updates are frequent and regular.<br />
• Vendor provides detailed update history on public web site.<br />
• Security check updates do not require reboot of IPS unit.<br />
Performance Consideration:<br />
• Does not introduce network latency.<br />
• Fails open should a power loss occur.<br />
• Notifies console of unit interruption. Console should receive alert and/or provide<br />
additional notification to administrator should any component become nonoperational<br />
or experience a communications problem.<br />
• The alert should specify the type of problem encountered, and users should have<br />
the ability to enable tracing mechanisms to determine the exact nature of the<br />
issue<br />
Accuracy of Intrusion Detection:<br />
• Accurately detects intrusion attempts and discerns between the various types<br />
and risk levels including unauthorized access attempts, pre-attack probes,<br />
suspicious activity, DoS, DDoS, vulnerability exploitation, brute force, hybrids,<br />
and zero-day attacks.<br />
• Accurately prevent intrusions from occurring. Describe underlying prevention<br />
technology.<br />
66


![vkcdkjh vk;qDr] e/;izns”k] Xokfy;j dk;kZy; vkcdkjh vk;qDr] e/;izns”k ...](https://img.yumpu.com/46609233/1/190x245/vkcdkjh-vkqdr-e-iznsk-xokfyj-dkkzy-vkcdkjh-vkqdr-e-iznsk-.jpg?quality=85)
![Page 1 wim 55] 3mm, WR, femm' 3 W13 2012-1151 14, 1s1§1933 ...](https://img.yumpu.com/43206412/1/178x260/page-1-wim-55-3mm-wr-femm-3-w13-2012-1151-14-1s11933-.jpg?quality=85)