MPED-X-Routing-Tender20080721 - Madhya Pradesh State Excise
MPED-X-Routing-Tender20080721 - Madhya Pradesh State Excise
MPED-X-Routing-Tender20080721 - Madhya Pradesh State Excise
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
o<br />
o<br />
o<br />
o<br />
o<br />
o<br />
o<br />
o<br />
o<br />
o<br />
o<br />
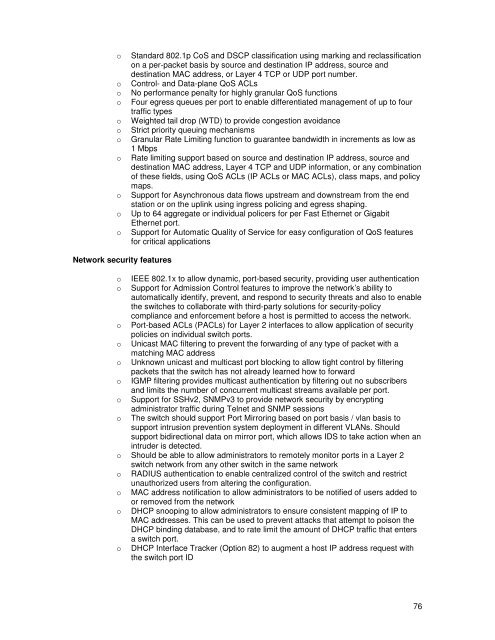
Standard 802.1p CoS and DSCP classification using marking and reclassification<br />
on a per-packet basis by source and destination IP address, source and<br />
destination MAC address, or Layer 4 TCP or UDP port number.<br />
Control- and Data-plane QoS ACLs<br />
No performance penalty for highly granular QoS functions<br />
Four egress queues per port to enable differentiated management of up to four<br />
traffic types<br />
Weighted tail drop (WTD) to provide congestion avoidance<br />
Strict priority queuing mechanisms<br />
Granular Rate Limiting function to guarantee bandwidth in increments as low as<br />
1 Mbps<br />
Rate limiting support based on source and destination IP address, source and<br />
destination MAC address, Layer 4 TCP and UDP information, or any combination<br />
of these fields, using QoS ACLs (IP ACLs or MAC ACLs), class maps, and policy<br />
maps.<br />
Support for Asynchronous data flows upstream and downstream from the end<br />
station or on the uplink using ingress policing and egress shaping.<br />
Up to 64 aggregate or individual policers for per Fast Ethernet or Gigabit<br />
Ethernet port.<br />
Support for Automatic Quality of Service for easy configuration of QoS features<br />
for critical applications<br />
Network security features<br />
o IEEE 802.1x to allow dynamic, port-based security, providing user authentication<br />
o Support for Admission Control features to improve the network’s ability to<br />
automatically identify, prevent, and respond to security threats and also to enable<br />
the switches to collaborate with third-party solutions for security-policy<br />
compliance and enforcement before a host is permitted to access the network.<br />
o Port-based ACLs (PACLs) for Layer 2 interfaces to allow application of security<br />
policies on individual switch ports.<br />
o Unicast MAC filtering to prevent the forwarding of any type of packet with a<br />
matching MAC address<br />
o Unknown unicast and multicast port blocking to allow tight control by filtering<br />
packets that the switch has not already learned how to forward<br />
o IGMP filtering provides multicast authentication by filtering out no subscribers<br />
and limits the number of concurrent multicast streams available per port.<br />
o Support for SSHv2, SNMPv3 to provide network security by encrypting<br />
administrator traffic during Telnet and SNMP sessions<br />
o The switch should support Port Mirroring based on port basis / vlan basis to<br />
support intrusion prevention system deployment in different VLANs. Should<br />
support bidirectional data on mirror port, which allows IDS to take action when an<br />
intruder is detected.<br />
o Should be able to allow administrators to remotely monitor ports in a Layer 2<br />
switch network from any other switch in the same network<br />
o RADIUS authentication to enable centralized control of the switch and restrict<br />
unauthorized users from altering the configuration.<br />
o MAC address notification to allow administrators to be notified of users added to<br />
or removed from the network<br />
o DHCP snooping to allow administrators to ensure consistent mapping of IP to<br />
MAC addresses. This can be used to prevent attacks that attempt to poison the<br />
DHCP binding database, and to rate limit the amount of DHCP traffic that enters<br />
a switch port.<br />
o DHCP Interface Tracker (Option 82) to augment a host IP address request with<br />
the switch port ID<br />
76


![vkcdkjh vk;qDr] e/;izns”k] Xokfy;j dk;kZy; vkcdkjh vk;qDr] e/;izns”k ...](https://img.yumpu.com/46609233/1/190x245/vkcdkjh-vkqdr-e-iznsk-xokfyj-dkkzy-vkcdkjh-vkqdr-e-iznsk-.jpg?quality=85)
![Page 1 wim 55] 3mm, WR, femm' 3 W13 2012-1151 14, 1s1§1933 ...](https://img.yumpu.com/43206412/1/178x260/page-1-wim-55-3mm-wr-femm-3-w13-2012-1151-14-1s11933-.jpg?quality=85)