Securitas AB Annual Report 2005
Securitas AB Annual Report 2005
Securitas AB Annual Report 2005
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
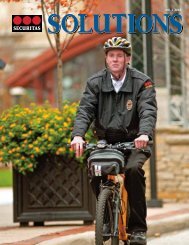
<strong>Securitas</strong> Systems<br />
Bell Security, acquired in 2004, is today a fully-integrated part of the company. Jon Morris (left), Project Manager<br />
at Bell Security, discusses an installation with a customer. Service Technician Matt Daniels (right), installs an alarm<br />
in Tower 42, the tallest building in London’s fi nancial district.<br />
Other companies within <strong>Securitas</strong> Systems have adopted<br />
the product, which offers distinct benefi ts for customers,<br />
especially banks with their own communication<br />
networks and high demands on reliable, cost-effective<br />
alarm monitoring.<br />
Objectives and strategies<br />
<strong>Securitas</strong> Systems has two main fi nancial objectives:<br />
■ annual sales growth of 8–10 percent<br />
■ a return on capital employed exceeding 20 percent<br />
Sales growth of 8–10 percent is estimated to be reasonable<br />
and is important in order to create portfolio growth<br />
and a reasonable profi tability level. Signifi cantly lower<br />
growth would mean the loss of market share.<br />
The long-term objective of at least a 20 percent return<br />
on capital employed is important in order to maintain<br />
focus on capital use and profi tability in a business where<br />
acquisitions are part of the strategy. Acquisitions should<br />
offer the potential to reach this objective within 2–5<br />
years. The timeframe varies depending on the size of<br />
the acquisition, whether it marks the launch of a new<br />
segment or new geographical market, or whether it<br />
complements an established business.<br />
To create growth and improve profi tability, <strong>Securitas</strong><br />
Systems follows a strategy focused on customer segmentation,<br />
centralized purchasing and acquisitions.<br />
The value chain<br />
Product Development<br />
Specifi cation of<br />
end user needs<br />
Sales and project<br />
management<br />
Customer segmentation<br />
One of the main reasons for segmenting customers is<br />
that it provides the basis for a greater understanding of<br />
their security needs. This knowledge makes it possible<br />
to adapt the entire value chain to each customer’s needs.<br />
Segmentation also facilitates identifi cation and integration<br />
of acquisitions. All acquisitions must be specialized<br />
in a specifi c segment.<br />
Banking and fi nance<br />
The strongest established segment in <strong>Securitas</strong> Systems<br />
is Banking and fi nance. The offering consists of security<br />
solutions for banks’ head and regional offi ces, comprising<br />
products, installation and a number of services such<br />
as “helpdesks”, alarm monitoring and response, remote<br />
monitoring and training of alarm and security specialists.<br />
Retail chains<br />
Retail chains typically have many similar units spread<br />
out across a large area, often an entire country or several<br />
countries. Customers want a uniform security concept,<br />
an overview over costs and functions, and some form of<br />
functional guarantee. This segment is growing quickly in<br />
Europe and the USA, and <strong>Securitas</strong> Systems will expand<br />
its presence in the segment.<br />
Service and<br />
maintenance<br />
Anna Jansson deputy branch manager at<br />
the Security Center in Stockholm. Thanks<br />
to state-of-the-art technology, operators are<br />
able to identify the signal in question when<br />
an alarm goes off, and thus quickly determine<br />
the type of response required.<br />
Monitoring and<br />
customer support<br />
A clear value chain allows <strong>Securitas</strong> Systems to enhance its offering to the customer. The offering is based on pure installation<br />
and service concepts which are adapted to various segments, such as banking and retail chain customers. Product development<br />
and production lie completely outside <strong>Securitas</strong> Systems’ value chain. Technical solutions and systems are procured via<br />
selected external partners in order to obtain favorable pricing and be able to infl uence product functionality and design.<br />
58 SECURITAS <strong>2005</strong>