Editorial & Advisory Board - Acta Technica Corviniensis
Editorial & Advisory Board - Acta Technica Corviniensis
Editorial & Advisory Board - Acta Technica Corviniensis
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Another technique based on access control<br />
mechanism is proposed by [19]. The authors in [19] use<br />
authorization views that enable transparent querying<br />
which are validated only when the information is<br />
present in the authorization views otherwise they are<br />
not. The benefit provided by this approach is that only<br />
the information and rules present in the authorization<br />
views are accepted and only then the access is granted<br />
otherwise the access is denied to the database.<br />
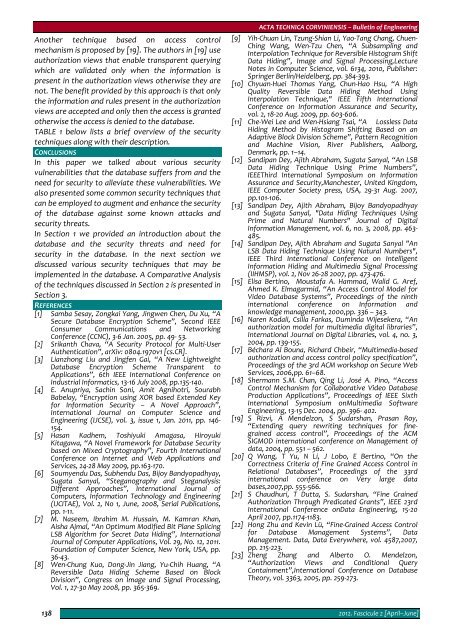
TABLE 1 below lists a brief overview of the security<br />
techniques along with their description.<br />
CONCLUSIONS<br />
In this paper we talked about various security<br />
vulnerabilities that the database suffers from and the<br />
need for security to alleviate these vulnerabilities. We<br />
also presented some common security techniques that<br />
can be employed to augment and enhance the security<br />
of the database against some known attacks and<br />
security threats.<br />
In Section 1 we provided an introduction about the<br />
database and the security threats and need for<br />
security in the database. In the next section we<br />
discussed various security techniques that may be<br />
implemented in the database. A Comparative Analysis<br />
of the techniques discussed in Section 2 is presented in<br />
Section 3.<br />
REFERENCES<br />
[1] Samba Sesay, Zongkai Yang, Jingwen Chen, Du Xu, “A<br />
Secure Database Encryption Scheme”, Second IEEE<br />
Consumer Communications and Networking<br />
Conference (CCNC), 3‐6 Jan. 2005, pp. 49‐ 53.<br />
[2] Srikanth Chava, “A Security Protocol for Multi‐User<br />
Authentication”, arXiv: 0804.1970v1 [cs.CR].<br />
[3] Lianzhong Liu and Jingfen Gai, “A New Lightweight<br />
Database Encryption Scheme Transparent to<br />
Applications”, 6th IEEE International Conference on<br />
Industrial Informatics, 13‐16 July 2008, pp.135‐140.<br />
[4] E. Anupriya, Sachin Soni, Amit Agnihotri, Sourabh<br />
Babelay, “Encryption using XOR based Extended Key<br />
for Information Security – A Novel Approach”,<br />
International Journal on Computer Science and<br />
Engineering (IJCSE), vol. 3, issue 1, Jan. 2011, pp. 146‐<br />
154.<br />
[5] Hasan Kadhem, Toshiyuki Amagasa, Hiroyuki<br />
Kitagawa, “A Novel Framework for Database Security<br />
based on Mixed Cryptography”, Fourth International<br />
Conference on Internet and Web Applications and<br />
Services, 24‐28 May 2009, pp.163‐170.<br />
[6] Soumyendu Das, Subhendu Das, Bijoy Bandyopadhyay,<br />
Sugata Sanyal, “Steganography and Steganalysis:<br />
Different Approaches”, International Journal of<br />
Computers, Information Technology and Engineering<br />
(IJCITAE), Vol. 2, No 1, June, 2008, Serial Publications,<br />
pp. 1‐11.<br />
[7] M. Naseem, Ibrahim M. Hussain, M. Kamran Khan,<br />
Aisha Ajmal, “An Optimum Modified Bit Plane Splicing<br />
LSB Algorithm for Secret Data Hiding”, International<br />
Journal of Computer Applications, Vol. 29, No. 12, 2011.<br />
Foundation of Computer Science, New York, USA, pp.<br />
36‐43.<br />
[8] Wen‐Chung Kuo, Dong‐Jin Jiang, Yu‐Chih Huang, “A<br />
Reversible Data Hiding Scheme Based on Block<br />
Division”, Congress on Image and Signal Processing,<br />
Vol. 1, 27‐30 May 2008, pp. 365‐369.<br />
ACTA TECHNICA CORVINIENSIS – Bulletin of Engineering<br />
[9] Yih‐Chuan Lin, Tzung‐Shian Li, Yao‐Tang Chang, Chuen‐<br />
Ching Wang, Wen‐Tzu Chen, “A Subsampling and<br />
Interpolation Technique for Reversible Histogram Shift<br />
Data Hiding”, Image and Signal Processing,Lecture<br />
Notes in Computer Science, vol. 6134, 2010, Publisher:<br />
Springer Berlin/Heidelberg, pp. 384‐393.<br />
[10] Chyuan‐Huei Thomas Yang, Chun‐Hao Hsu, “A High<br />
Quality Reversible Data Hiding Method Using<br />
Interpolation Technique," IEEE Fifth International<br />
Conference on Information Assurance and Security,<br />
vol. 2, 18‐20 Aug. 2009, pp. 603‐606.<br />
[11] Che‐Wei Lee and Wen‐Hsiang Tsai, “A Lossless Data<br />
Hiding Method by Histogram Shifting Based on an<br />
Adaptive Block Division Scheme”, Pattern Recognition<br />
and Machine Vision, River Publishers, Aalborg,<br />
Denmark, pp. 1–14.<br />
[12] Sandipan Dey, Ajith Abraham, Sugata Sanyal, “An LSB<br />
Data Hiding Technique Using Prime Numbers”,<br />
IEEEThird International Symposium on Information<br />
Assurance and Security,Manchester, United Kingdom,<br />
IEEE Computer Society press, USA, 29‐31 Aug. 2007,<br />
pp.101‐106.<br />
[13] Sandipan Dey, Ajith Abraham, Bijoy Bandyopadhyay<br />
and Sugata Sanyal, "Data Hiding Techniques Using<br />
Prime and Natural Numbers" Journal of Digital<br />
Information Management, vol. 6, no. 3, 2008, pp. 463‐<br />
485.<br />
[14] Sandipan Dey, Ajith Abraham and Sugata Sanyal "An<br />
LSB Data Hiding Technique Using Natural Numbers",<br />
IEEE Third International Conference on Intelligent<br />
Information Hiding and Multimedia Signal Processing<br />
(IIHMSP), vol. 2, Nov 26‐28 2007, pp. 473‐476.<br />
[15] Elisa Bertino, Moustafa A. Hammad, Walid G. Aref,<br />
Ahmed K. Elmagarmid, “An Access Control Model for<br />
Video Database Systems”, Proceedings of the ninth<br />
international conference on Information and<br />
knowledge management, 2000,pp. 336 – 343.<br />
[16] Naren Kodali, Csilla Farkas, Duminda Wijesekera, “An<br />
authorization model for multimedia digital libraries”,<br />
International Journal on Digital Libraries, vol. 4, no. 3,<br />
2004, pp. 139‐155.<br />
[17] Béchara Al Bouna, Richard Chbeir, “Multimedia‐based<br />
authorization and access control policy specification”,<br />
Proceedings of the 3rd ACM workshop on Secure Web<br />
Services, 2006,pp. 61–68.<br />
[18] Shermann S.M. Chan, Qing Li, José A. Pino, “Access<br />
Control Mechanism for Collaborative Video Database<br />
Production Applications”, Proceedings of IEEE Sixth<br />
International Symposium onMultimedia Software<br />
Engineering, 13‐15 Dec. 2004, pp. 396‐ 402.<br />
[19] S Rizvi, A Mendelzon, S Sudarshan, Prasan Roy,<br />
“Extending query rewriting techniques for finegrained<br />
access control”, Proceedings of the ACM<br />
SIGMOD international conference on Management of<br />
data, 2004, pp. 551 – 562.<br />
[20] Q Wang, T Yu, N Li, J Lobo, E Bertino, “On the<br />
Correctness Criteria of Fine Grained Access Control in<br />
Relational Databases”, Proceedings of the 33rd<br />
international conference on Very large data<br />
bases,2007,pp. 555‐566.<br />
[21] S Chaudhuri, T Dutta, S. Sudarshan, “Fine Grained<br />
Authorization Through Predicated Grants”, IEEE 23rd<br />
International Conference onData Engineering, 15‐20<br />
April 2007, pp.1174‐1183.<br />
[22] Hong Zhu and Kevin Lü, “Fine‐Grained Access Control<br />
for Database Management Systems”, Data<br />
Management. Data, Data Everywhere, vol. 4587,2007,<br />
pp. 215‐223.<br />
[23] Zheng Zhang and Alberto O. Mendelzon,<br />
“Authorization Views and Conditional Query<br />
Containment”,International Conference on Database<br />
Theory, vol. 3363, 2005, pp. 259‐273.<br />
138<br />
2012. Fascicule 2 [April–June]