FortiGate IPSec VPN User Guide - FirewallShop.com
FortiGate IPSec VPN User Guide - FirewallShop.com
FortiGate IPSec VPN User Guide - FirewallShop.com
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
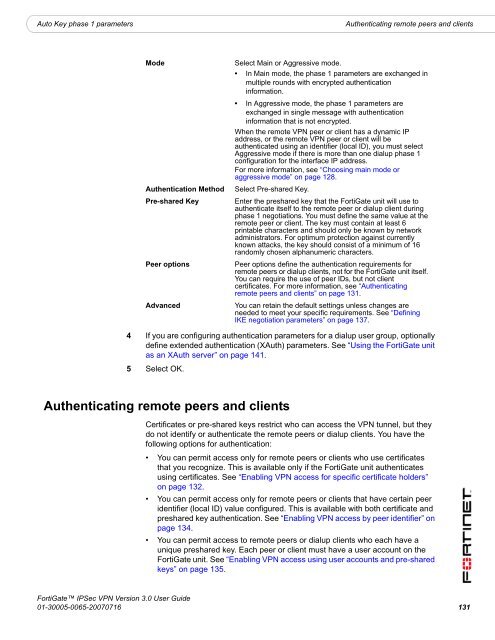
Auto Key phase 1 parameters<br />
Authenticating remote peers and clients<br />
Mode<br />
Authentication Method<br />
Pre-shared Key<br />
Peer options<br />
Advanced<br />
Select Main or Aggressive mode.<br />
• In Main mode, the phase 1 parameters are exchanged in<br />
multiple rounds with encrypted authentication<br />
information.<br />
• In Aggressive mode, the phase 1 parameters are<br />
exchanged in single message with authentication<br />
information that is not encrypted.<br />
When the remote <strong>VPN</strong> peer or client has a dynamic IP<br />
address, or the remote <strong>VPN</strong> peer or client will be<br />
authenticated using an identifier (local ID), you must select<br />
Aggressive mode if there is more than one dialup phase 1<br />
configuration for the interface IP address.<br />
For more information, see “Choosing main mode or<br />
aggressive mode” on page 128.<br />
Select Pre-shared Key.<br />
Enter the preshared key that the <strong>FortiGate</strong> unit will use to<br />
authenticate itself to the remote peer or dialup client during<br />
phase 1 negotiations. You must define the same value at the<br />
remote peer or client. The key must contain at least 6<br />
printable characters and should only be known by network<br />
administrators. For optimum protection against currently<br />
known attacks, the key should consist of a minimum of 16<br />
randomly chosen alphanumeric characters.<br />
Peer options define the authentication requirements for<br />
remote peers or dialup clients, not for the <strong>FortiGate</strong> unit itself.<br />
You can require the use of peer IDs, but not client<br />
certificates. For more information, see “Authenticating<br />
remote peers and clients” on page 131.<br />
You can retain the default settings unless changes are<br />
needed to meet your specific requirements. See “Defining<br />
IKE negotiation parameters” on page 137.<br />
4 If you are configuring authentication parameters for a dialup user group, optionally<br />
define extended authentication (XAuth) parameters. See “Using the <strong>FortiGate</strong> unit<br />
as an XAuth server” on page 141.<br />
5 Select OK.<br />
Authenticating remote peers and clients<br />
Certificates or pre-shared keys restrict who can access the <strong>VPN</strong> tunnel, but they<br />
do not identify or authenticate the remote peers or dialup clients. You have the<br />
following options for authentication:<br />
• You can permit access only for remote peers or clients who use certificates<br />
that you recognize. This is available only if the <strong>FortiGate</strong> unit authenticates<br />
using certificates. See “Enabling <strong>VPN</strong> access for specific certificate holders”<br />
on page 132.<br />
• You can permit access only for remote peers or clients that have certain peer<br />
identifier (local ID) value configured. This is available with both certificate and<br />
preshared key authentication. See “Enabling <strong>VPN</strong> access by peer identifier” on<br />
page 134.<br />
• You can permit access to remote peers or dialup clients who each have a<br />
unique preshared key. Each peer or client must have a user account on the<br />
<strong>FortiGate</strong> unit. See “Enabling <strong>VPN</strong> access using user accounts and pre-shared<br />
keys” on page 135.<br />
<strong>FortiGate</strong> <strong>IPSec</strong> <strong>VPN</strong> Version 3.0 <strong>User</strong> <strong>Guide</strong><br />
01-30005-0065-20070716 131