FortiGate IPSec VPN User Guide - FirewallShop.com
FortiGate IPSec VPN User Guide - FirewallShop.com
FortiGate IPSec VPN User Guide - FirewallShop.com
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
How to work with overlapping subnets<br />
Gateway-to-gateway configurations<br />
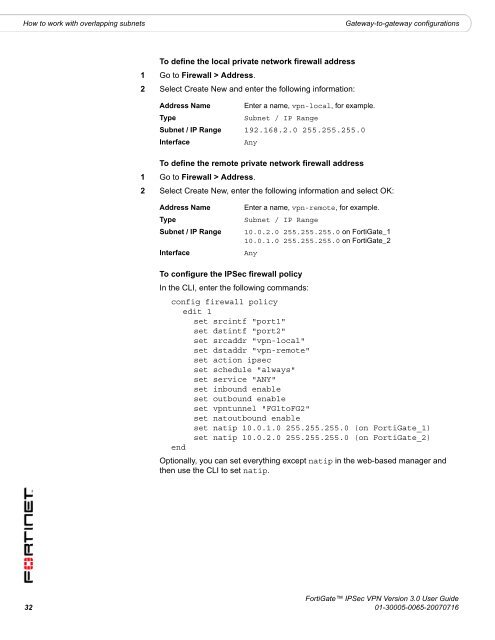
To define the local private network firewall address<br />
1 Go to Firewall > Address.<br />
2 Select Create New and enter the following information:<br />
Address Name Enter a name, vpn-local, for example.<br />
Type<br />
Subnet / IP Range<br />
Subnet / IP Range 192.168.2.0 255.255.255.0<br />
Interface<br />
Any<br />
To define the remote private network firewall address<br />
1 Go to Firewall > Address.<br />
2 Select Create New, enter the following information and select OK:<br />
Address Name<br />
Type<br />
Subnet / IP Range<br />
Interface<br />
Enter a name, vpn-remote, for example.<br />
Subnet / IP Range<br />
10.0.2.0 255.255.255.0 on <strong>FortiGate</strong>_1<br />
10.0.1.0 255.255.255.0 on <strong>FortiGate</strong>_2<br />
Any<br />
To configure the <strong>IPSec</strong> firewall policy<br />
In the CLI, enter the following <strong>com</strong>mands:<br />
config firewall policy<br />
edit 1<br />
set srcintf "port1"<br />
set dstintf "port2"<br />
set srcaddr "vpn-local"<br />
set dstaddr "vpn-remote"<br />
set action ipsec<br />
set schedule "always"<br />
set service "ANY"<br />
set inbound enable<br />
set outbound enable<br />
set vpntunnel "FG1toFG2"<br />
set natoutbound enable<br />
set natip 10.0.1.0 255.255.255.0 (on <strong>FortiGate</strong>_1)<br />
set natip 10.0.2.0 255.255.255.0 (on <strong>FortiGate</strong>_2)<br />
end<br />
Optionally, you can set everything except natip in the web-based manager and<br />
then use the CLI to set natip.<br />
<strong>FortiGate</strong> <strong>IPSec</strong> <strong>VPN</strong> Version 3.0 <strong>User</strong> <strong>Guide</strong><br />
32 01-30005-0065-20070716