FortiGate IPSec VPN User Guide - FirewallShop.com
FortiGate IPSec VPN User Guide - FirewallShop.com
FortiGate IPSec VPN User Guide - FirewallShop.com
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Auto Key phase 1 parameters<br />
Defining IKE negotiation parameters<br />
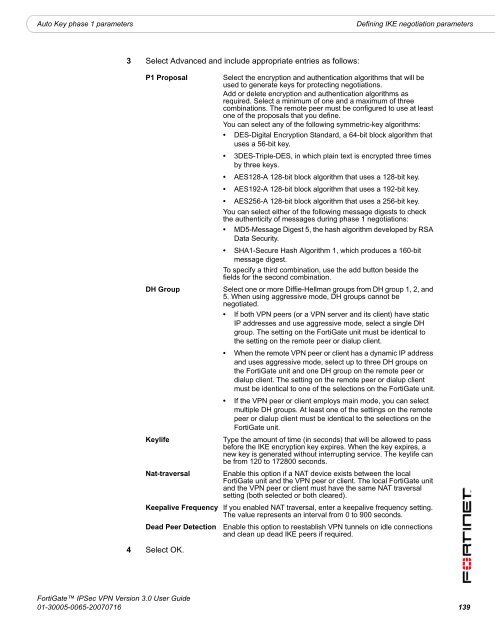
3 Select Advanced and include appropriate entries as follows:<br />
P1 Proposal<br />
DH Group<br />
Keylife<br />
4 Select OK.<br />
Select the encryption and authentication algorithms that will be<br />
used to generate keys for protecting negotiations.<br />
Add or delete encryption and authentication algorithms as<br />
required. Select a minimum of one and a maximum of three<br />
<strong>com</strong>binations. The remote peer must be configured to use at least<br />
one of the proposals that you define.<br />
You can select any of the following symmetric-key algorithms:<br />
• DES-Digital Encryption Standard, a 64-bit block algorithm that<br />
uses a 56-bit key.<br />
• 3DES-Triple-DES, in which plain text is encrypted three times<br />
by three keys.<br />
• AES128-A 128-bit block algorithm that uses a 128-bit key.<br />
• AES192-A 128-bit block algorithm that uses a 192-bit key.<br />
• AES256-A 128-bit block algorithm that uses a 256-bit key.<br />
You can select either of the following message digests to check<br />
the authenticity of messages during phase 1 negotiations:<br />
• MD5-Message Digest 5, the hash algorithm developed by RSA<br />
Data Security.<br />
• SHA1-Secure Hash Algorithm 1, which produces a 160-bit<br />
message digest.<br />
To specify a third <strong>com</strong>bination, use the add button beside the<br />
fields for the second <strong>com</strong>bination.<br />
Select one or more Diffie-Hellman groups from DH group 1, 2, and<br />
5. When using aggressive mode, DH groups cannot be<br />
negotiated.<br />
• If both <strong>VPN</strong> peers (or a <strong>VPN</strong> server and its client) have static<br />
IP addresses and use aggressive mode, select a single DH<br />
group. The setting on the <strong>FortiGate</strong> unit must be identical to<br />
the setting on the remote peer or dialup client.<br />
• When the remote <strong>VPN</strong> peer or client has a dynamic IP address<br />
and uses aggressive mode, select up to three DH groups on<br />
the <strong>FortiGate</strong> unit and one DH group on the remote peer or<br />
dialup client. The setting on the remote peer or dialup client<br />
must be identical to one of the selections on the <strong>FortiGate</strong> unit.<br />
• If the <strong>VPN</strong> peer or client employs main mode, you can select<br />
multiple DH groups. At least one of the settings on the remote<br />
peer or dialup client must be identical to the selections on the<br />
<strong>FortiGate</strong> unit.<br />
Type the amount of time (in seconds) that will be allowed to pass<br />
before the IKE encryption key expires. When the key expires, a<br />
new key is generated without interrupting service. The keylife can<br />
be from 120 to 172800 seconds.<br />
Nat-traversal Enable this option if a NAT device exists between the local<br />
<strong>FortiGate</strong> unit and the <strong>VPN</strong> peer or client. The local <strong>FortiGate</strong> unit<br />
and the <strong>VPN</strong> peer or client must have the same NAT traversal<br />
setting (both selected or both cleared).<br />
Keepalive Frequency If you enabled NAT traversal, enter a keepalive frequency setting.<br />
The value represents an interval from 0 to 900 seconds.<br />
Dead Peer Detection Enable this option to reestablish <strong>VPN</strong> tunnels on idle connections<br />
and clean up dead IKE peers if required.<br />
<strong>FortiGate</strong> <strong>IPSec</strong> <strong>VPN</strong> Version 3.0 <strong>User</strong> <strong>Guide</strong><br />
01-30005-0065-20070716 139