OS6860(E)_AOS_8.1.1.R01_Switch_Management_Guide
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Managing <strong>Switch</strong> Security<br />
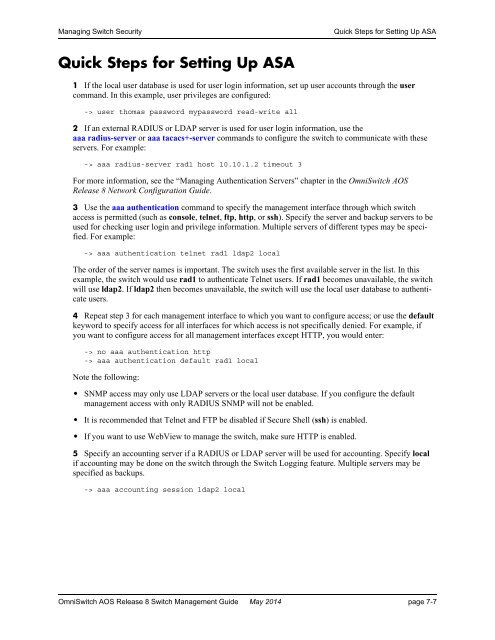
Quick Steps for Setting Up ASA<br />
Quick Steps for Setting Up ASA<br />
1 If the local user database is used for user login information, set up user accounts through the user<br />
command. In this example, user privileges are configured:<br />
-> user thomas password mypassword read-write all<br />
2 If an external RADIUS or LDAP server is used for user login information, use the<br />
aaa radius-server or aaa tacacs+-server commands to configure the switch to communicate with these<br />
servers. For example:<br />
-> aaa radius-server rad1 host 10.10.1.2 timeout 3<br />
For more information, see the “Managing Authentication Servers” chapter in the Omni<strong>Switch</strong> <strong>AOS</strong><br />
Release 8 Network Configuration <strong>Guide</strong>.<br />
3 Use the aaa authentication command to specify the management interface through which switch<br />
access is permitted (such as console, telnet, ftp, http, or ssh). Specify the server and backup servers to be<br />
used for checking user login and privilege information. Multiple servers of different types may be specified.<br />
For example:<br />
-> aaa authentication telnet rad1 ldap2 local<br />
The order of the server names is important. The switch uses the first available server in the list. In this<br />
example, the switch would use rad1 to authenticate Telnet users. If rad1 becomes unavailable, the switch<br />
will use ldap2. If ldap2 then becomes unavailable, the switch will use the local user database to authenticate<br />
users.<br />
4 Repeat step 3 for each management interface to which you want to configure access; or use the default<br />
keyword to specify access for all interfaces for which access is not specifically denied. For example, if<br />
you want to configure access for all management interfaces except HTTP, you would enter:<br />
-> no aaa authentication http<br />
-> aaa authentication default rad1 local<br />
Note the following:<br />
• SNMP access may only use LDAP servers or the local user database. If you configure the default<br />
management access with only RADIUS SNMP will not be enabled.<br />
• It is recommended that Telnet and FTP be disabled if Secure Shell (ssh) is enabled.<br />
• If you want to use WebView to manage the switch, make sure HTTP is enabled.<br />
5 Specify an accounting server if a RADIUS or LDAP server will be used for accounting. Specify local<br />
if accounting may be done on the switch through the <strong>Switch</strong> Logging feature. Multiple servers may be<br />
specified as backups.<br />
-> aaa accounting session ldap2 local<br />
Omni<strong>Switch</strong> <strong>AOS</strong> Release 8 <strong>Switch</strong> <strong>Management</strong> <strong>Guide</strong> May 2014 page 7-7