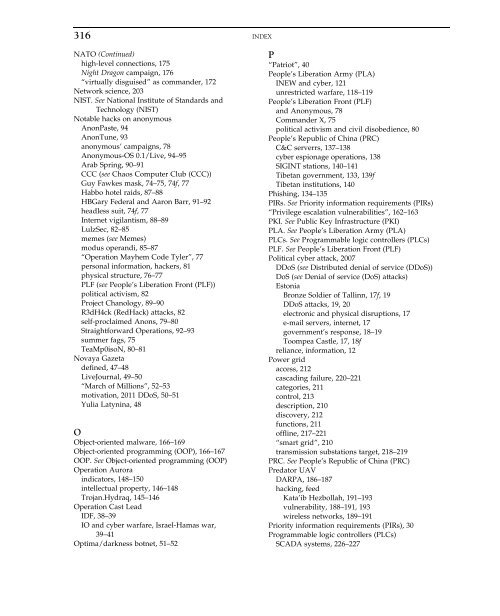
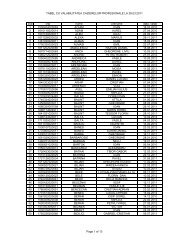
INDEX315INEW. See Integrated network electronic warfare (INEW)Information assuranceauthentication, 7authenticity, 7confidentiality, 8McCumber model, 6–7Information operations (IO)and cyber warfare, 2008 Israel-Hamas war, 39–41Hezbollah, 35–37Information requirements (IRs), 128Information-stealing Trojansforensic analysis, 165hosting companies, 164–165operation, 164–165Information technology vs. industrial control systems,201–203Infrastructure attacks and network <strong>to</strong>pologyminimization, harm, 205–206“node degree”, 205“nodes”/“edges”, 203rail system, 203–204Integrated network electronic warfare (INEW), 121Internet pro<strong>to</strong>col (IP)Hezbollah hijacks, addresses, 37–38, 37fRussian, 26Internet vigilantism, 88–89IO. See Information operations (IO)IP. See Internet pro<strong>to</strong>col (IP)Iranian <strong>Cyber</strong> Army (ICA)controls, 58domain name hijacking, 57–58Iranian nuclear facilities attack, Stuxneteffectiveness, Natanz Facility, 229–231FEP targeting, 228Iran, 228–229malware, 232–233Natanz Fuel Enrichment Facility, 224–226reactions, Iranian regime, 231–232security assumptions, 233–234Source Code, 229IRs. See Information requirements (IRs)Islamic Revolutionary Guard Corps (IRGC), 191, 193Israel-Hezbollah “July War”, 2006Hezbollah insignia, 34, 35fhijacks, IP address, 37–38, 37fIO, 35–37, 36fIsraeli Defense Force (IDF)destruction, civilian infrastructure, 36–37launch, cyber attacks, 37Spokesperson’s Unit, 39JJuly war. See Israel-Hezbollah “July War”, 2006KKata’ib Hezbollahconnections, 191–193description, 191Kernel mode rootkitscreation, 161description, 161Duqu, 161–162responsibility, 162LLinkedIn connections, 172–177Low Orbit Ion Cannon (LOIC) <strong>to</strong>ol, 13, 14–15LulzSecDDoS and SQL injection vulnerabilitiesexploitation, 84Facebook, 85hacktivities, list of, 245LulzSec’s logo, 82–83, 83f“The Cabin Crew”, 85Twitter, 85MMachbot network, 28Malicious Security (MalSec), 82MalSec. See Malicious Security (MalSec)“March of Millions”, 52–53Maroochy Water BreachMaroochy SCADA system, 206moni<strong>to</strong>ring equipment, 206McCumber model, 6–7Memes, 72–73“Moralfags”, 75Moving target indica<strong>to</strong>r (MTI), 188MTI. See Moving target indica<strong>to</strong>r (MTI)MTS. See Multi-spectral targeting system (MTS)Multi-spectral targeting system (MTS), 188NNashi, 17, 18, 23, 48Natanz Fuel Enrichment FacilityIR-1 centrifuges, 225low-enriched uranium (LEU), 225–226SCADA systems, 226–227Siemens’ Step 7 software, 227–228uranium enrichment, 225, 229Natanz Fuel Enrichment Plant, 228–232National Institute of Standards and Technology (NIST),201–203, 207NATOfalse Facebook accounts, 172
316 INDEXNATO (Continued)high-level connections, 175Night Dragon campaign, 176“virtually disguised” as commander, 172Network science, 203NIST. See National Institute of Standards andTechnology (NIST)Notable hacks on anonymousAnonPaste, 94AnonTune, 93anonymous’ campaigns, 78Anonymous-OS 0.1/Live, 94–95Arab Spring, 90–91CCC (see Chaos Computer Club (CCC))Guy Fawkes mask, 74–75, 74f, 77Habbo hotel raids, 87–88HBGary Federal and Aaron Barr, 91–92headless suit, 74f, 77Internet vigilantism, 88–89LulzSec, 82–85memes (see Memes)modus operandi, 85–87“Operation Mayhem Code Tyler”, 77personal information, hackers, 81physical structure, 76–77PLF (see People’s Liberation Front (PLF))political activism, 82Project Chanology, 89–90R3dH4ck (RedHack) attacks, 82self-proclaimed Anons, 79–80Straightforward Operations, 92–93summer fags, 75TeaMp0isoN, 80–81Novaya Gazetadefined, 47–48LiveJournal, 49–50“March of Millions”, 52–53motivation, 2011 DDoS, 50–51Yulia Latynina, 48OObject-oriented malware, 166–169Object-oriented programming (OOP), 166–167OOP. See Object-oriented programming (OOP)Operation Auroraindica<strong>to</strong>rs, 148–150intellectual property, 146–148Trojan.Hydraq, 145–146Operation Cast LeadIDF, 38–39IO and cyber warfare, Israel-Hamas war,39–41Optima/darkness botnet, 51–52P“Patriot”, 40People’s Liberation Army (PLA)INEW and cyber, 121unrestricted warfare, 118–119People’s Liberation Front (PLF)and Anonymous, 78Commander X, 75political activism and civil disobedience, 80People’s Republic of China (PRC)C&C serverrs, 137–138cyber espionage operations, 138SIGINT stations, 140–141Tibetan government, 133, 139fTibetan institutions, 140Phishing, 134–135PIRs. See Priority information requirements (PIRs)“Privilege escalation vulnerabilities”, 162–163PKI. See Public Key Infrastructure (PKI)PLA. See People’s Liberation Army (PLA)PLCs. See Programmable logic controllers (PLCs)PLF. See People’s Liberation Front (PLF)Political cyber attack, 2007DDoS (see Distributed denial of service (DDoS))DoS (see Denial of service (DoS) attacks)Es<strong>to</strong>niaBronze Soldier of Tallinn, 17f, 19DDoS attacks, 19, 20electronic and physical disruptions, 17e-mail servers, internet, 17government’s response, 18–19Toompea Castle, 17, 18freliance, information, 12Power gridaccess, 212cascading failure, 220–221categories, 211control, 213description, 210discovery, 212functions, 211offline, 217–221“smart grid”, 210transmission substations target, 218–219PRC. See People’s Republic of China (PRC)Preda<strong>to</strong>r UAVDARPA, 186–187hacking, feedKata’ib Hezbollah, 191–193vulnerability, 188–191, 193wireless networks, 189–191Priority information requirements (PIRs), 30Programmable logic controllers (PLCs)SCADA systems, 226–227
- Page 2 and 3:
INTRODUCTION TOCYBER-WARFARE
- Page 4 and 5:
INTRODUCTIONTO CYBER-WARFAREA Multi
- Page 6 and 7:
ContentsPreface ixForeword xiIntrod
- Page 8 and 9:
CONTENTSviiHow Real-World Dependenc
- Page 10 and 11:
PrefaceSince Stuxnet emerged in 201
- Page 12 and 13:
ForewordThe concept of cyber warfar
- Page 14 and 15:
IntroductionIt is 2006. An American
- Page 16 and 17:
INTRODUCTIONxvinfamous hacking grou
- Page 18 and 19:
BiographyPaulo Shakarian, Ph.D. is
- Page 20 and 21:
C H A P T E R1Cyber Warfare: Here a
- Page 22 and 23:
IS CYBER WAR A CREDIBLE THREAT?3sec
- Page 24 and 25:
ATTRIBUTION, DECEPTION, AND INTELLI
- Page 26 and 27:
INFORMATION ASSURANCE74. Time: Temp
- Page 28 and 29:
P A R T ICYBER ATTACKInformation ha
- Page 30 and 31:
C H A P T E R2Political Cyber Attac
- Page 32 and 33:
RUDIMENTARY BUT EFFECTIVE: DENIAL O
- Page 34 and 35:
THE DIFFICULTY OF ASSIGNING BLAME:
- Page 36 and 37:
ESTONIA IS HIT BY CYBER ATTACKS17FI
- Page 38:
ESTONIA IS HIT BY CYBER ATTACKS19Th
- Page 41 and 42:
22 2. POLITICAL CYBER ATTACK COMES
- Page 43 and 44:
24 3. HOW CYBER ATTACKS AUGMENTED R
- Page 45 and 46:
26 3. HOW CYBER ATTACKS AUGMENTED R
- Page 47 and 48:
28 3. HOW CYBER ATTACKS AUGMENTED R
- Page 49 and 50:
30 3. HOW CYBER ATTACKS AUGMENTED R
- Page 51 and 52:
32 3. HOW CYBER ATTACKS AUGMENTED R
- Page 53 and 54:
34 4. CYBER AND INFORMATION OPERATI
- Page 55 and 56:
36 4. CYBER AND INFORMATION OPERATI
- Page 57 and 58:
38 4. CYBER AND INFORMATION OPERATI
- Page 59 and 60:
40 4. CYBER AND INFORMATION OPERATI
- Page 61 and 62:
42 4. CYBER AND INFORMATION OPERATI
- Page 63 and 64:
44 5. CYBER ATTACK AGAINST INTERNAL
- Page 65 and 66:
46 5. CYBER ATTACK AGAINST INTERNAL
- Page 67 and 68:
48 5. CYBER ATTACK AGAINST INTERNAL
- Page 69 and 70:
50 5. CYBER ATTACK AGAINST INTERNAL
- Page 71 and 72:
52 5. CYBER ATTACK AGAINST INTERNAL
- Page 73 and 74:
54 5. CYBER ATTACK AGAINST INTERNAL
- Page 75 and 76:
56 5. CYBER ATTACK AGAINST INTERNAL
- Page 77 and 78:
58 5. CYBER ATTACK AGAINST INTERNAL
- Page 79 and 80:
60 5. CYBER ATTACK AGAINST INTERNAL
- Page 81 and 82:
62 5. CYBER ATTACK AGAINST INTERNAL
- Page 83 and 84:
64 5. CYBER ATTACK AGAINST INTERNAL
- Page 85 and 86:
66 5. CYBER ATTACK AGAINST INTERNAL
- Page 87 and 88:
68 6. CYBER ATTACKS BY NONSTATE HAC
- Page 89 and 90:
70 6. CYBER ATTACKS BY NONSTATE HAC
- Page 91 and 92:
72 6. CYBER ATTACKS BY NONSTATE HAC
- Page 93 and 94:
74 6. CYBER ATTACKS BY NONSTATE HAC
- Page 95 and 96:
76 6. CYBER ATTACKS BY NONSTATE HAC
- Page 97 and 98:
78 6. CYBER ATTACKS BY NONSTATE HAC
- Page 99 and 100:
80 6. CYBER ATTACKS BY NONSTATE HAC
- Page 101 and 102:
82 6. CYBER ATTACKS BY NONSTATE HAC
- Page 103 and 104:
84 6. CYBER ATTACKS BY NONSTATE HAC
- Page 105 and 106:
86 6. CYBER ATTACKS BY NONSTATE HAC
- Page 107 and 108:
88 6. CYBER ATTACKS BY NONSTATE HAC
- Page 109 and 110:
90 6. CYBER ATTACKS BY NONSTATE HAC
- Page 111 and 112:
92 6. CYBER ATTACKS BY NONSTATE HAC
- Page 113 and 114:
94 6. CYBER ATTACKS BY NONSTATE HAC
- Page 115 and 116:
96 6. CYBER ATTACKS BY NONSTATE HAC
- Page 117 and 118:
98 6. CYBER ATTACKS BY NONSTATE HAC
- Page 119 and 120:
100 6. CYBER ATTACKS BY NONSTATE HA
- Page 121 and 122:
102 6. CYBER ATTACKS BY NONSTATE HA
- Page 123 and 124:
104 6. CYBER ATTACKS BY NONSTATE HA
- Page 125 and 126:
106 6. CYBER ATTACKS BY NONSTATE HA
- Page 127 and 128:
108 6. CYBER ATTACKS BY NONSTATE HA
- Page 129 and 130:
110 6. CYBER ATTACKS BY NONSTATE HA
- Page 131 and 132:
Intentionally left as blank
- Page 133 and 134:
114 7. WHY CYBER ESPIONAGE IS A KEY
- Page 135 and 136:
116 7. WHY CYBER ESPIONAGE IS A KEY
- Page 137 and 138:
118 7. WHY CYBER ESPIONAGE IS A KEY
- Page 139 and 140:
120 7. WHY CYBER ESPIONAGE IS A KEY
- Page 141 and 142:
122 7. WHY CYBER ESPIONAGE IS A KEY
- Page 143 and 144:
124 7. WHY CYBER ESPIONAGE IS A KEY
- Page 145 and 146:
126 7. WHY CYBER ESPIONAGE IS A KEY
- Page 147 and 148:
128 7. WHY CYBER ESPIONAGE IS A KEY
- Page 149 and 150:
130 7. WHY CYBER ESPIONAGE IS A KEY
- Page 151 and 152:
132 7. WHY CYBER ESPIONAGE IS A KEY
- Page 153 and 154:
134 7. WHY CYBER ESPIONAGE IS A KEY
- Page 155 and 156:
136 7. WHY CYBER ESPIONAGE IS A KEY
- Page 157 and 158:
138 7. WHY CYBER ESPIONAGE IS A KEY
- Page 159 and 160:
140 7. WHY CYBER ESPIONAGE IS A KEY
- Page 161 and 162:
142 7. WHY CYBER ESPIONAGE IS A KEY
- Page 163 and 164:
144 7. WHY CYBER ESPIONAGE IS A KEY
- Page 165 and 166:
146 7. WHY CYBER ESPIONAGE IS A KEY
- Page 167 and 168:
148 7. WHY CYBER ESPIONAGE IS A KEY
- Page 169 and 170:
150 7. WHY CYBER ESPIONAGE IS A KEY
- Page 171 and 172:
152 7. WHY CYBER ESPIONAGE IS A KEY
- Page 173 and 174:
154 7. WHY CYBER ESPIONAGE IS A KEY
- Page 175 and 176:
156 7. WHY CYBER ESPIONAGE IS A KEY
- Page 177 and 178:
Intentionally left as blank
- Page 179 and 180:
160 8. DUQU, FLAME, GAUSS, THE NEXT
- Page 181 and 182:
162 8. DUQU, FLAME, GAUSS, THE NEXT
- Page 183 and 184:
164 8. DUQU, FLAME, GAUSS, THE NEXT
- Page 185 and 186:
166 8. DUQU, FLAME, GAUSS, THE NEXT
- Page 187 and 188:
168 8. DUQU, FLAME, GAUSS, THE NEXT
- Page 189 and 190:
170 8. DUQU, FLAME, GAUSS, THE NEXT
- Page 191 and 192:
172 9. LOSING TRUST IN YOUR FRIENDS
- Page 193 and 194:
174 9. LOSING TRUST IN YOUR FRIENDS
- Page 195 and 196:
176 9. LOSING TRUST IN YOUR FRIENDS
- Page 197 and 198:
178 9. LOSING TRUST IN YOUR FRIENDS
- Page 199 and 200:
180 9. LOSING TRUST IN YOUR FRIENDS
- Page 201 and 202:
182 9. LOSING TRUST IN YOUR FRIENDS
- Page 203 and 204:
Intentionally left as blank
- Page 205 and 206:
186 10. INFORMATION THEFT ON THE TA
- Page 207 and 208:
188 10. INFORMATION THEFT ON THE TA
- Page 209 and 210:
190 10. INFORMATION THEFT ON THE TA
- Page 211 and 212:
192 10. INFORMATION THEFT ON THE TA
- Page 213 and 214:
194 10. INFORMATION THEFT ON THE TA
- Page 215 and 216:
196 10. INFORMATION THEFT ON THE TA
- Page 217 and 218:
Intentionally left as blank
- Page 219 and 220:
200 11. CYBER WARFARE AGAINST INDUS
- Page 221 and 222:
202 11. CYBER WARFARE AGAINST INDUS
- Page 223 and 224:
204 11. CYBER WARFARE AGAINST INDUS
- Page 225 and 226:
206 11. CYBER WARFARE AGAINST INDUS
- Page 227 and 228:
208 11. CYBER WARFARE AGAINST INDUS
- Page 229 and 230:
210 12. CYBER ATTACKS AGAINST POWER
- Page 231 and 232:
212 12. CYBER ATTACKS AGAINST POWER
- Page 233 and 234:
214 12. CYBER ATTACKS AGAINST POWER
- Page 235 and 236:
216 12. CYBER ATTACKS AGAINST POWER
- Page 237 and 238:
218 12. CYBER ATTACKS AGAINST POWER
- Page 239 and 240:
220 12. CYBER ATTACKS AGAINST POWER
- Page 241 and 242:
222 12. CYBER ATTACKS AGAINST POWER
- Page 243 and 244:
224 13. ATTACKING IRANIAN NUCLEAR F
- Page 245 and 246:
226 13. ATTACKING IRANIAN NUCLEAR F
- Page 247 and 248:
228 13. ATTACKING IRANIAN NUCLEAR F
- Page 249 and 250:
230 13. ATTACKING IRANIAN NUCLEAR F
- Page 251 and 252:
232 13. ATTACKING IRANIAN NUCLEAR F
- Page 253 and 254:
234 13. ATTACKING IRANIAN NUCLEAR F
- Page 255 and 256:
236 13. ATTACKING IRANIAN NUCLEAR F
- Page 257 and 258:
238 13. ATTACKING IRANIAN NUCLEAR F
- Page 259 and 260:
Intentionally left as blank
- Page 261 and 262:
242 CONCLUSION AND THE FUTURE OF CY
- Page 263 and 264:
Intentionally left as blank
- Page 265 and 266:
246 APPENDIX I. CHAPTER 6: LULZSEC
- Page 267 and 268:
248 APPENDIX I. CHAPTER 6: LULZSEC
- Page 269 and 270:
250 APPENDIX I. CHAPTER 6: LULZSEC
- Page 271 and 272:
252 APPENDIX I. CHAPTER 6: LULZSEC
- Page 273 and 274:
254 APPENDIX I. CHAPTER 6: LULZSEC
- Page 275 and 276:
256 APPENDIX I. CHAPTER 6: LULZSEC
- Page 277 and 278:
258 APPENDIX II. CHAPTER 6: ANONYMO
- Page 279 and 280:
260 APPENDIX II. CHAPTER 6: ANONYMO
- Page 281 and 282:
262 APPENDIX II. CHAPTER 6: ANONYMO
- Page 283 and 284: 264 APPENDIX II. CHAPTER 6: ANONYMO
- Page 285 and 286: 266 APPENDIX II. CHAPTER 6: ANONYMO
- Page 287 and 288: 268 APPENDIX II. CHAPTER 6: ANONYMO
- Page 289 and 290: 270 APPENDIX II. CHAPTER 6: ANONYMO
- Page 291 and 292: 272 APPENDIX II. CHAPTER 6: ANONYMO
- Page 293 and 294: 274 APPENDIX II. CHAPTER 6: ANONYMO
- Page 295 and 296: 276 APPENDIX II. CHAPTER 6: ANONYMO
- Page 297 and 298: 278 APPENDIX II. CHAPTER 6: ANONYMO
- Page 299 and 300: 280 APPENDIX II. CHAPTER 6: ANONYMO
- Page 301 and 302: 282 APPENDIX II. CHAPTER 6: ANONYMO
- Page 303 and 304: 284 APPENDIX II. CHAPTER 6: ANONYMO
- Page 305 and 306: 286 APPENDIX II. CHAPTER 6: ANONYMO
- Page 307 and 308: 288 APPENDIX II. CHAPTER 6: ANONYMO
- Page 309 and 310: 290 APPENDIX II. CHAPTER 6: ANONYMO
- Page 311 and 312: 292 APPENDIX II. CHAPTER 6: ANONYMO
- Page 313 and 314: 294 APPENDIX II. CHAPTER 6: ANONYMO
- Page 315 and 316: 296 APPENDIX II. CHAPTER 6: ANONYMO
- Page 317 and 318: 298 APPENDIX II. CHAPTER 6: ANONYMO
- Page 319 and 320: 300 APPENDIX II. CHAPTER 6: ANONYMO
- Page 321 and 322: 302 APPENDIX II. CHAPTER 6: ANONYMO
- Page 323 and 324: 304 APPENDIX II. CHAPTER 6: ANONYMO
- Page 325 and 326: Intentionally left as blank
- Page 327 and 328: 308 GLOSSARYDDoS distributed denial
- Page 329 and 330: 310 GLOSSARYNIST National Institute
- Page 331 and 332: Intentionally left as blank
- Page 333: 314 INDEXCyber exploitation (Contin
- Page 337: 318 INDEXTechnical intelligence (TE