You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
2.PHP Vulnerabilities<br />
In some cases, the hacker can use vulnerable PHP scripts to execute commands, display the file<br />
sources, list the contents <strong>of</strong> directories or upload files on a server in order to finally take total control <strong>of</strong><br />
or steal the contents <strong>of</strong> a database. There are several vulnerabilities at the PHP level; those coming<br />
from the PHP source code and those due to improper website development by the webmaster.<br />
For a start, here are several examples <strong>of</strong> vulnerabilities coming from the PHP source code which we<br />
will not attempt to detail in order not to lose time on details where a good knowledge <strong>of</strong> applicative<br />
vulnerabilities is needed:<br />
http://www.securityfocus.com/archive/1/368864<br />
http://www.securityfocus.com/archive/1/368861<br />
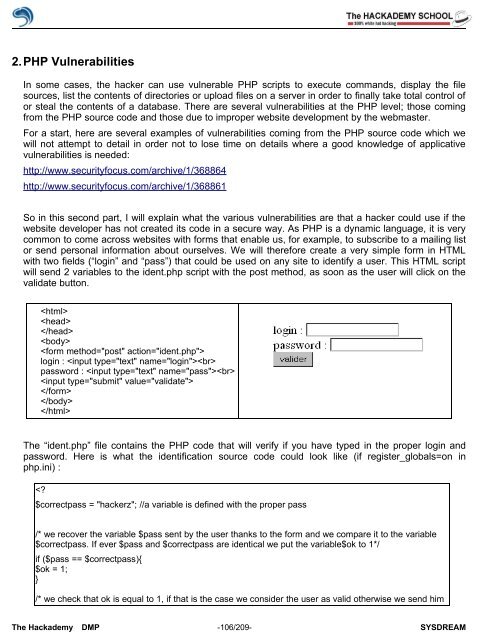
So in this second part, I will explain what the various vulnerabilities are that a hacker could use if the<br />
website developer has not created its code in a secure way. As PHP is a dynamic language, it is very<br />
common to come across websites with forms that enable us, for example, to subscribe to a mailing list<br />
or send personal information about ourselves. We will therefore create a very simple form in HTML<br />
with two fields (“login” and “pass”) that could be used on any site to identify a user. This HTML script<br />
will send 2 variables to the ident.php script with the post method, as soon as the user will click on the<br />
validate button.<br />
<br />
<br />
<br />
<br />
<br />
login : <br />
password : <br />
<br />
<br />
<br />
<br />
The “ident.php” file contains the PHP code that will verify if you have typed in the proper login and<br />
password. Here is what the identification source code could look like (if register_globals=on in<br />
php.ini) :<br />