You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
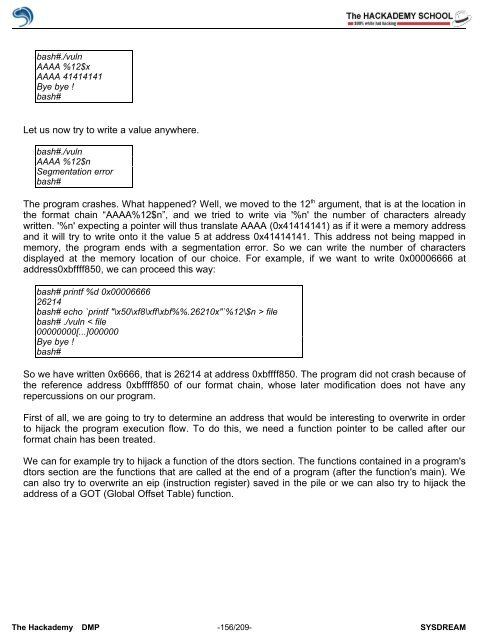
ash#./vuln<br />
AAAA %12$x<br />
AAAA 41414141<br />
Bye bye !<br />
bash#<br />
Let us now try to write a value anywhere.<br />
bash#./vuln<br />
AAAA %12$n<br />
Segmentation error<br />
bash#<br />
The program crashes. What happened? Well, we moved to the 12 th argument, that is at the location in<br />
the format chain “AAAA%12$n”, and we tried to write via '%n' the number <strong>of</strong> characters already<br />
written. '%n' expecting a pointer will thus translate AAAA (0x41414141) as if it were a memory address<br />
and it will try to write onto it the value 5 at address 0x41414141. This address not being mapped in<br />
memory, the program ends with a segmentation error. So we can write the number <strong>of</strong> characters<br />
displayed at the memory location <strong>of</strong> our choice. For example, if we want to write 0x00006666 at<br />
address0xbffff850, we can proceed this way:<br />
bash# printf %d 0x00006666<br />
26214<br />
bash# echo `printf "\x50\xf8\xff\xbf%%.26210x"`%12\$n > file<br />
bash# ./vuln < file<br />
00000000[...]000000<br />
Bye bye !<br />
bash#<br />
So we have written 0x6666, that is 26214 at address 0xbffff850. The program did not crash because <strong>of</strong><br />
the reference address 0xbffff850 <strong>of</strong> our format chain, whose later modification does not have any<br />
repercussions on our program.<br />
First <strong>of</strong> all, we are going to try to determine an address that would be interesting to overwrite in order<br />
to hijack the program execution flow. To do this, we need a function pointer to be called after our<br />
format chain has been treated.<br />
We can for example try to hijack a function <strong>of</strong> the dtors section. The functions contained in a program's<br />
dtors section are the functions that are called at the end <strong>of</strong> a program (after the function's main). We<br />
can also try to overwrite an eip (instruction register) saved in the pile or we can also try to hijack the<br />
address <strong>of</strong> a GOT (Global Offset Table) function.<br />
The <strong>Hack</strong>ademy DMP -156/209- SYSDREAM