Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
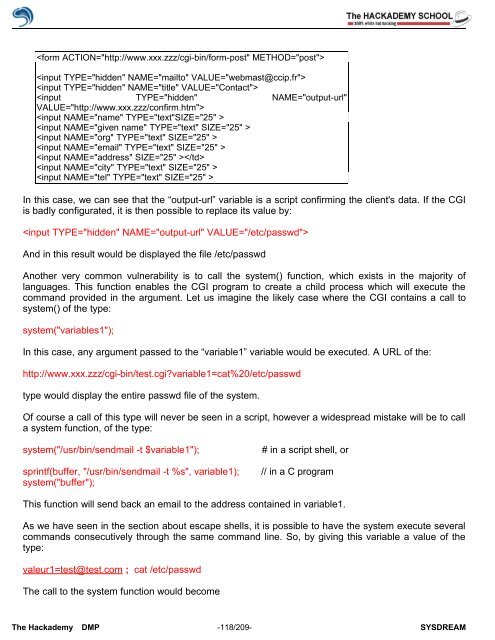
In this case, we can see that the “output-url” variable is a script confirming the client's data. If the CGI<br />
is badly configurated, it is then possible to replace its value by:<br />
<br />
And in this result would be displayed the file /etc/passwd<br />
Another very common vulnerability is to call the system() function, which exists in the majority <strong>of</strong><br />
languages. This function enables the CGI program to create a child process which will execute the<br />
command provided in the argument. Let us imagine the likely case where the CGI contains a call to<br />
system() <strong>of</strong> the type:<br />
system("variables1");<br />
In this case, any argument passed to the “variable1” variable would be executed. A URL <strong>of</strong> the:<br />
http://www.xxx.zzz/cgi-bin/test.cgi?variable1=cat%20/etc/passwd<br />
type would display the entire passwd file <strong>of</strong> the system.<br />
Of course a call <strong>of</strong> this type will never be seen in a script, however a widespread mistake will be to call<br />
a system function, <strong>of</strong> the type:<br />
system("/usr/bin/sendmail -t $variable1"); # in a script shell, or<br />
sprintf(buffer, "/usr/bin/sendmail -t %s", variable1); // in a C program<br />
system("buffer");<br />
This function will send back an email to the address contained in variable1.<br />
As we have seen in the section about escape shells, it is possible to have the system execute several<br />
commands consecutively through the same command line. So, by giving this variable a value <strong>of</strong> the<br />
type:<br />
valeur1=test@test.com ; cat /etc/passwd<br />
The call to the system function would become<br />
The <strong>Hack</strong>ademy DMP -118/209- SYSDREAM