Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
1.Intrusion detection systems<br />
Intrusion detection systems are probes that are placed on the network to listen to all transiting network<br />
frames. Their main functions are:<br />
– Detecting port scans.<br />
– Detecting applicative and web attacks, by comparing the contents <strong>of</strong> network fames to<br />
databases <strong>of</strong> attack signatures.<br />
The reference when it comes to intrusion detection today is SNORT, which <strong>of</strong>fers a large array <strong>of</strong><br />
possibilities. What's more, it can be used on both Linux and Windows.<br />
The first security rule to have when using an IDS is to not configure one's network card. It is put in<br />
promiscuous mode in order to examine all transiting frames, and in no way needs to be configured to<br />
communicate with other machines <strong>of</strong> the LAN. So, in case <strong>of</strong> intrusion, it is not possible for the hacker<br />
to try to attack this probe. That way you can be sure <strong>of</strong> having real results in case <strong>of</strong> a successful<br />
intrusion. Also, an IDS must be installed on a clean machine. As it is the only non-falsifiable source <strong>of</strong><br />
information, any other service could be a potential danger for the integrity <strong>of</strong> the system, and therefore<br />
<strong>of</strong> the results obtained.<br />
We are going to start by installing snort on a Linux system, with a mysql medium, and a log reading via<br />
a php interface called ACID.<br />
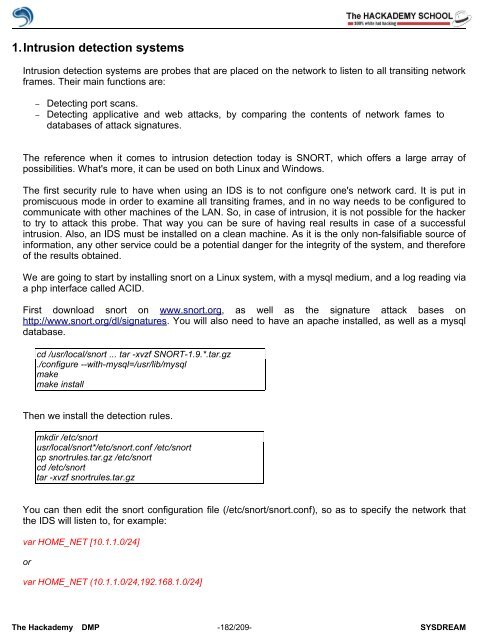
First download snort on www.snort.org, as well as the signature attack bases on<br />
http://www.snort.org/dl/signatures. You will also need to have an apache installed, as well as a mysql<br />
database.<br />
cd /usr/local/snort ... tar -xvzf SNORT-1.9.*.tar.gz<br />
./configure --with-mysql=/usr/lib/mysql<br />
make<br />
make install<br />
Then we install the detection rules.<br />
mkdir /etc/snort<br />
usr/local/snort*/etc/snort.conf /etc/snort<br />
cp snortrules.tar.gz /etc/snort<br />
cd /etc/snort<br />
tar -xvzf snortrules.tar.gz<br />
You can then edit the snort configuration file (/etc/snort/snort.conf), so as to specify the network that<br />
the IDS will listen to, for example:<br />
var HOME_NET [10.1.1.0/24]<br />
or<br />
var HOME_NET (10.1.1.0/24,192.168.1.0/24]<br />
The <strong>Hack</strong>ademy DMP -182/209- SYSDREAM