Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
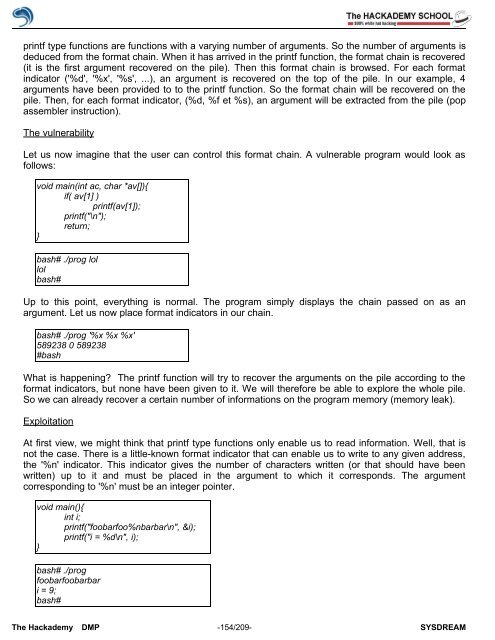
printf type functions are functions with a varying number <strong>of</strong> arguments. So the number <strong>of</strong> arguments is<br />
deduced from the format chain. When it has arrived in the printf function, the format chain is recovered<br />
(it is the first argument recovered on the pile). Then this format chain is browsed. For each format<br />
indicator ('%d', '%x', '%s', ...), an argument is recovered on the top <strong>of</strong> the pile. In our example, 4<br />
arguments have been provided to to the printf function. So the format chain will be recovered on the<br />
pile. Then, for each format indicator, (%d, %f et %s), an argument will be extracted from the pile (pop<br />
assembler instruction).<br />
The vulnerability<br />
Let us now imagine that the user can control this format chain. A vulnerable program would look as<br />
follows:<br />
void main(int ac, char *av[]){<br />
if( av[1] )<br />
printf(av[1]);<br />
printf("\n");<br />
return;<br />
}<br />
bash# ./prog lol<br />
lol<br />
bash#<br />
Up to this point, everything is normal. The program simply displays the chain passed on as an<br />
argument. Let us now place format indicators in our chain.<br />
bash# ./prog '%x %x %x'<br />
589238 0 589238<br />
#bash<br />
What is happening? The printf function will try to recover the arguments on the pile according to the<br />
format indicators, but none have been given to it. We will therefore be able to explore the whole pile.<br />
So we can already recover a certain number <strong>of</strong> informations on the program memory (memory leak).<br />
Exploitation<br />
At first view, we might think that printf type functions only enable us to read information. Well, that is<br />
not the case. There is a little-known format indicator that can enable us to write to any given address,<br />
the '%n' indicator. This indicator gives the number <strong>of</strong> characters written (or that should have been<br />
written) up to it and must be placed in the argument to which it corresponds. The argument<br />
corresponding to '%n' must be an integer pointer.<br />
void main(){<br />
int i;<br />
printf("foobarfoo%nbarbar\n", &i);<br />
printf("i = %d\n", i);<br />
}<br />
bash# ./prog<br />
foobarfoobarbar<br />
i = 9;<br />
bash#<br />
The <strong>Hack</strong>ademy DMP -154/209- SYSDREAM