You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
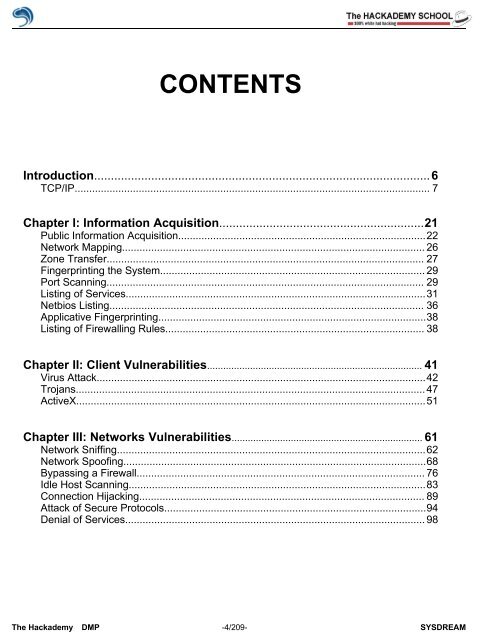
CONTENTS<br />
Introduction....................................................................................................6<br />
TCP/IP.......................................................................................................................... 7<br />
Chapter I: Information Acquisition.............................................................21<br />
Public Information Acquisition.....................................................................................22<br />
Network Mapping........................................................................................................ 26<br />
Zone Transfer............................................................................................................. 27<br />
Fingerprinting the System........................................................................................... 29<br />
Port Scanning............................................................................................................. 29<br />
Listing <strong>of</strong> Services.......................................................................................................31<br />
Netbios Listing............................................................................................................ 36<br />
Applicative Fingerprinting............................................................................................38<br />
Listing <strong>of</strong> Firewalling Rules......................................................................................... 38<br />
Chapter II: Client Vulnerabilities................................................................................ 41<br />
Virus Attack.................................................................................................................42<br />
Trojans........................................................................................................................ 47<br />
ActiveX........................................................................................................................51<br />
Chapter III: Networks Vulnerabilities....................................................................... 61<br />
Network Sniffing..........................................................................................................62<br />
Network Spo<strong>of</strong>ing........................................................................................................68<br />
Bypassing a Firewall................................................................................................... 76<br />
Idle Host Scanning......................................................................................................83<br />
Connection Hijacking.................................................................................................. 89<br />
Attack <strong>of</strong> Secure <strong>Pro</strong>tocols..........................................................................................94<br />
Denial <strong>of</strong> Services....................................................................................................... 98<br />
The <strong>Hack</strong>ademy DMP -4/209- SYSDREAM