Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
shell:pr<strong>of</strong>ile<br />
shell:Administrative Tools<br />
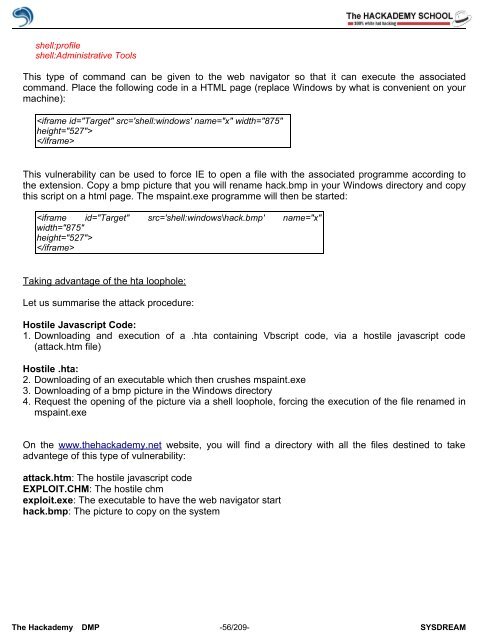
This type <strong>of</strong> command can be given to the web navigator so that it can execute the associated<br />
command. Place the following code in a HTML page (replace Windows by what is convenient on your<br />
machine):<br />
<br />
<br />
This vulnerability can be used to force IE to open a file with the associated programme according to<br />
the extension. Copy a bmp picture that you will rename hack.bmp in your Windows directory and copy<br />
this script on a html page. The mspaint.exe programme will then be started:<br />
<br />
<br />
Taking advantage <strong>of</strong> the hta loophole:<br />
Let us summarise the attack procedure:<br />
Hostile Javascript Code:<br />
1. Downloading and execution <strong>of</strong> a .hta containing Vbscript code, via a hostile javascript code<br />
(attack.htm file)<br />
Hostile .hta:<br />
2. Downloading <strong>of</strong> an executable which then crushes mspaint.exe<br />
3. Downloading <strong>of</strong> a bmp picture in the Windows directory<br />
4. Request the opening <strong>of</strong> the picture via a shell loophole, forcing the execution <strong>of</strong> the file renamed in<br />
mspaint.exe<br />
On the www.thehackademy.net website, you will find a directory with all the files destined to take<br />
advantege <strong>of</strong> this type <strong>of</strong> vulnerability:<br />
attack.htm: The hostile javascript code<br />
EXPLOIT.CHM: The hostile chm<br />
exploit.exe: The executable to have the web navigator start<br />
hack.bmp: The picture to copy on the system<br />
The <strong>Hack</strong>ademy DMP -56/209- SYSDREAM