You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
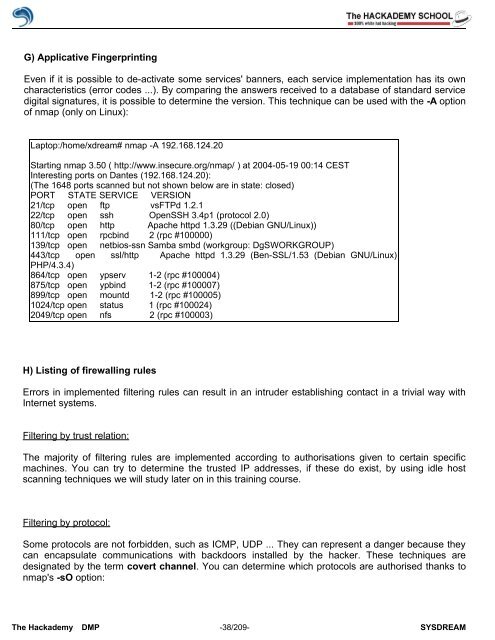
G) Applicative Fingerprinting<br />
Even if it is possible to de-activate some services' banners, each service implementation has its own<br />
characteristics (error codes ...). By comparing the answers received to a database <strong>of</strong> standard service<br />
digital signatures, it is possible to determine the version. This technique can be used with the -A option<br />
<strong>of</strong> nmap (only on Linux):<br />
Laptop:/home/xdream# nmap -A 192.168.124.20<br />
Starting nmap 3.50 ( http://www.insecure.org/nmap/ ) at 2004-05-19 00:14 CEST<br />
Interesting ports on Dantes (192.168.124.20):<br />
(The 1648 ports scanned but not shown below are in state: closed)<br />
PORT STATE SERVICE VERSION<br />
21/tcp open ftp vsFTPd 1.2.1<br />
22/tcp open ssh OpenSSH 3.4p1 (protocol 2.0)<br />
80/tcp open http Apache httpd 1.3.29 ((Debian GNU/Linux))<br />
111/tcp open rpcbind 2 (rpc #100000)<br />
139/tcp open netbios-ssn Samba smbd (workgroup: DgSWORKGROUP)<br />
443/tcp open ssl/http Apache httpd 1.3.29 (Ben-SSL/1.53 (Debian GNU/Linux)<br />
PHP/4.3.4)<br />
864/tcp open ypserv 1-2 (rpc #100004)<br />
875/tcp open ypbind 1-2 (rpc #100007)<br />
899/tcp open mountd 1-2 (rpc #100005)<br />
1024/tcp open status 1 (rpc #100024)<br />
2049/tcp open nfs 2 (rpc #100003)<br />
H) Listing <strong>of</strong> firewalling rules<br />
Errors in implemented filtering rules can result in an intruder establishing contact in a trivial way with<br />
Internet systems.<br />
Filtering by trust relation:<br />
The majority <strong>of</strong> filtering rules are implemented according to authorisations given to certain specific<br />
machines. You can try to determine the trusted IP addresses, if these do exist, by using idle host<br />
scanning techniques we will study later on in this training course.<br />
Filtering by protocol:<br />
Some protocols are not forbidden, such as ICMP, UDP ... They can represent a danger because they<br />
can encapsulate communications with backdoors installed by the hacker. These techniques are<br />
designated by the term covert channel. You can determine which protocols are authorised thanks to<br />
nmap's -sO option:<br />
The <strong>Hack</strong>ademy DMP -38/209- SYSDREAM