Product Manual
Product Manual
Product Manual
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
DES-3526 / DES-3526DC Fast Ethernet Layer 2 Switch<br />
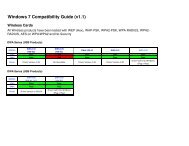
System Utilities Yes No<br />
Factory Reset Yes No<br />
User Account Management<br />
Add/Update/Delete User Accounts Yes No<br />
View User Accounts Yes No<br />
Table 7- 1. Admin and User Privileges<br />
After establishing a User Account with Admin-level privileges, be sure to save the changes by opening<br />
the Maintenance folder, opening the Save Changes window and clicking the Save Configuration<br />
button.<br />
Access Authentication Control<br />
The TACACS/XTACACS/TACACS+/RADIUS commands let you secure access to the Switch using<br />
the TACACS/XTACACS/TACACS+/RADIUS protocols. When a user logs in to the Switch or tries to<br />
access the administrator level privilege, he or she is prompted for a password. If<br />
TACACS/XTACACS/TACACS+/RADIUS authentication is enabled on the Switch, it will contact a<br />
TACACS/XTACACS/TACACS+/RADIUS server to verify the user. If the user is verified, he or she<br />
is granted access to the Switch.<br />
There are currently three versions of the TACACS security protocol, each a separate entity. The<br />
Switch's software supports the following versions of TACACS:<br />
• TACACS (Terminal Access Controller Access Control System) - Provides password checking and<br />
authentication, and notification of user actions for security purposes utilizing via one or more centralized<br />
TACACS servers, utilizing the UDP protocol for packet transmission.<br />
• Extended TACACS (XTACACS) - An extension of the TACACS protocol with the ability to provide more<br />
types of authentication requests and more types of response codes than TACACS. This protocol also uses UDP<br />
to transmit packets.<br />
• TACACS+ (Terminal Access Controller Access Control System plus) - Provides detailed access control for<br />
authentication for network devices. TACACS+ is facilitated through Authentication commands via one or more<br />
centralized servers. The TACACS+ protocol encrypts all traffic between the Switch and the TACACS+ daemon,<br />
using the TCP protocol to ensure reliable delivery<br />
In order for the TACACS/XTACACS/TACACS+/RADIUS security function to work properly, a<br />
TACACS/XTACACS/TACACS+/RADIUS server must be configured on a device other than the<br />
Switch, called an Authentication Server Host and it must include usernames and passwords for<br />
authentication. When the user is prompted by the Switch to enter usernames and passwords for<br />
authentication, the Switch contacts the TACACS/XTACACS/TACACS+/RADIUS server to verify,<br />
and the server will respond with one of three messages:<br />
• The server verifies the username and password, and the user is granted normal user privileges on the Switch.<br />
• The server will not accept the username and password and the user is denied access to the Switch.<br />
• The server doesn't respond to the verification query. At this point, the Switch receives the timeout from the<br />
server and then moves to the next method of verification configured in the method list.<br />
The Switch has four built-in Authentication Server Groups, one for each of the TACACS, XTA-<br />
CACS, TACACS+ and RADIUS protocols. These built-in Authentication Server Groups are used to<br />
authenticate users trying to access the Switch. The users will set Authentication Server Hosts in a<br />
preferable order in the built-in Authentication Server Groups and when a user tries to gain access to<br />
123