Product Manual
Product Manual
Product Manual
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
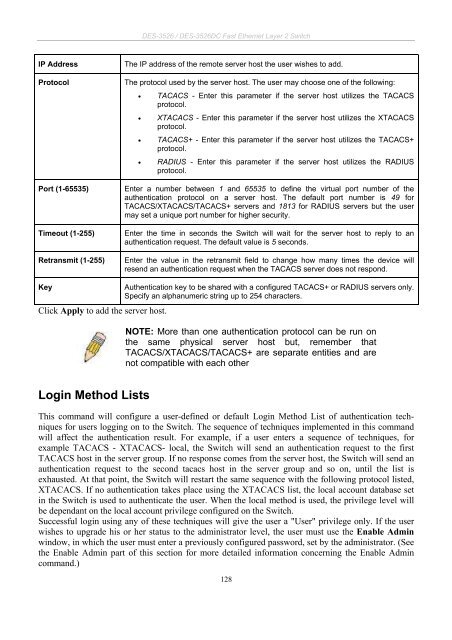
DES-3526 / DES-3526DC Fast Ethernet Layer 2 Switch<br />
IP Address The IP address of the remote server host the user wishes to add.<br />
Protocol The protocol used by the server host. The user may choose one of the following:<br />
• TACACS - Enter this parameter if the server host utilizes the TACACS<br />
protocol.<br />
• XTACACS - Enter this parameter if the server host utilizes the XTACACS<br />
protocol.<br />
• TACACS+ - Enter this parameter if the server host utilizes the TACACS+<br />
protocol.<br />
• RADIUS - Enter this parameter if the server host utilizes the RADIUS<br />
protocol.<br />
Port (1-65535) Enter a number between 1 and 65535 to define the virtual port number of the<br />
authentication protocol on a server host. The default port number is 49 for<br />
TACACS/XTACACS/TACACS+ servers and 1813 for RADIUS servers but the user<br />
may set a unique port number for higher security.<br />
Timeout (1-255) Enter the time in seconds the Switch will wait for the server host to reply to an<br />
authentication request. The default value is 5 seconds.<br />
Retransmit (1-255) Enter the value in the retransmit field to change how many times the device will<br />
resend an authentication request when the TACACS server does not respond.<br />
Key Authentication key to be shared with a configured TACACS+ or RADIUS servers only.<br />
Specify an alphanumeric string up to 254 characters.<br />
Click Apply to add the server host.<br />
Login Method Lists<br />
NOTE: More than one authentication protocol can be run on<br />
the same physical server host but, remember that<br />
TACACS/XTACACS/TACACS+ are separate entities and are<br />
not compatible with each other<br />
This command will configure a user-defined or default Login Method List of authentication techniques<br />
for users logging on to the Switch. The sequence of techniques implemented in this command<br />
will affect the authentication result. For example, if a user enters a sequence of techniques, for<br />
example TACACS - XTACACS- local, the Switch will send an authentication request to the first<br />
TACACS host in the server group. If no response comes from the server host, the Switch will send an<br />
authentication request to the second tacacs host in the server group and so on, until the list is<br />
exhausted. At that point, the Switch will restart the same sequence with the following protocol listed,<br />
XTACACS. If no authentication takes place using the XTACACS list, the local account database set<br />
in the Switch is used to authenticate the user. When the local method is used, the privilege level will<br />
be dependant on the local account privilege configured on the Switch.<br />
Successful login using any of these techniques will give the user a "User" privilege only. If the user<br />
wishes to upgrade his or her status to the administrator level, the user must use the Enable Admin<br />
window, in which the user must enter a previously configured password, set by the administrator. (See<br />
the Enable Admin part of this section for more detailed information concerning the Enable Admin<br />
command.)<br />
128