CLI Guide - TP-Link
CLI Guide - TP-Link
CLI Guide - TP-Link
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
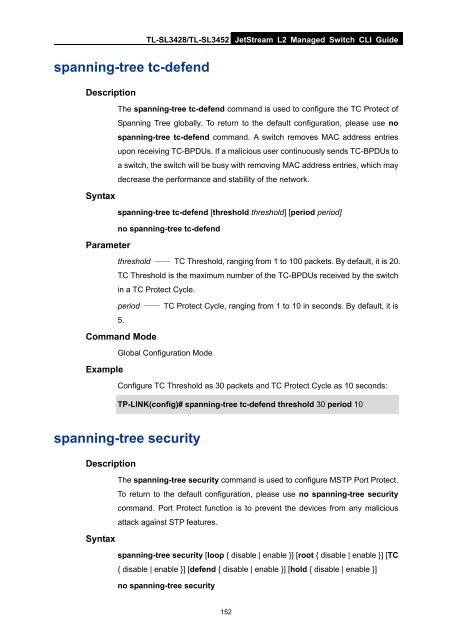
spanning-tree tc-defend<br />
TL-SL3428/TL-SL3452 JetStream L2 Managed Switch <strong>CLI</strong> <strong>Guide</strong><br />
Description<br />
The spanning-tree tc-defend command is used to configure the TC Protect of<br />
Spanning Tree globally. To return to the default configuration, please use no<br />
spanning-tree tc-defend command. A switch removes MAC address entries<br />
upon receiving TC-BPDUs. If a malicious user continuously sends TC-BPDUs to<br />
a switch, the switch will be busy with removing MAC address entries, which may<br />
decrease the performance and stability of the network.<br />
Syntax<br />
spanning-tree tc-defend [threshold threshold] [period period]<br />
no spanning-tree tc-defend<br />
Parameter<br />
threshold —— TC Threshold, ranging from 1 to 100 packets. By default, it is 20.<br />
TC Threshold is the maximum number of the TC-BPDUs received by the switch<br />
in a TC Protect Cycle.<br />
period —— TC Protect Cycle, ranging from 1 to 10 in seconds. By default, it is<br />
5.<br />
Command Mode<br />
Global Configuration Mode<br />
Example<br />
Configure TC Threshold as 30 packets and TC Protect Cycle as 10 seconds:<br />
<strong>TP</strong>-LINK(config)# spanning-tree tc-defend threshold 30 period 10<br />
spanning-tree security<br />
Description<br />
The spanning-tree security command is used to configure MS<strong>TP</strong> Port Protect.<br />
To return to the default configuration, please use no spanning-tree security<br />
command. Port Protect function is to prevent the devices from any malicious<br />
attack against S<strong>TP</strong> features.<br />
Syntax<br />
spanning-tree security [loop { disable | enable }] [root { disable | enable }] [TC<br />
{ disable | enable }] [defend { disable | enable }] [hold { disable | enable }]<br />
no spanning-tree security<br />
152