Warning Analysis for the Information Age - Higgins Counterterrorism ...
Warning Analysis for the Information Age - Higgins Counterterrorism ...
Warning Analysis for the Information Age - Higgins Counterterrorism ...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
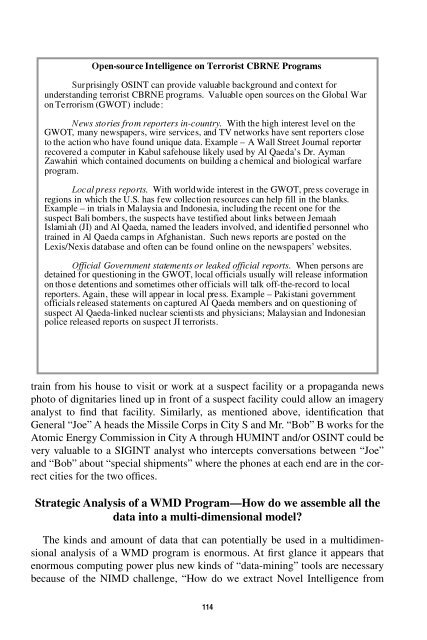
Open-source Intelligence on Terrorist CBRNE ProgramsSurprisingly OSINT can provide valuable background and context <strong>for</strong>understanding terrorist CBRNE programs. Valuable open sources on <strong>the</strong> Global Waron Terrorism (GWOT) include:News stories from reporters in-country. With <strong>the</strong> high interest level on <strong>the</strong>GWOT, many newspapers, wire services, and TV networks have sent reporters closeto <strong>the</strong> action who have found unique data. Example – A Wall Street Journal reporterrecovered a computer in Kabul safehouse likely used by Al Qaeda’s Dr. AymanZawahiri which contained documents on building a chemical and biological warfareprogram.Local press reports. With worldwide interest in <strong>the</strong> GWOT, press coverage inregions in which <strong>the</strong> U.S. has few collection resources can help fill in <strong>the</strong> blanks.Example – in trials in Malaysia and Indonesia, including <strong>the</strong> recent one <strong>for</strong> <strong>the</strong>suspect Bali bombers, <strong>the</strong> suspects have testified about links between JemaahIslamiah (JI) and Al Qaeda, named <strong>the</strong> leaders involved, and identified personnel whotrained in Al Qaeda camps in Afghanistan. Such news reports are posted on <strong>the</strong>Lexis/Nexis database and often can be found online on <strong>the</strong> newspapers’ websites.Official Government statements or leaked official reports. When persons aredetained <strong>for</strong> questioning in <strong>the</strong> GWOT, local officials usually will release in<strong>for</strong>mationon those detentions and sometimes o<strong>the</strong>r officials will talk off-<strong>the</strong>-record to localreporters. Again, <strong>the</strong>se will appear in local press. Example – Pakistani governmentofficials released statements on captured Al Qaeda members and on questioning ofsuspect Al Qaeda-linked nuclear scientists and physicians; Malaysian and Indonesianpolice released reports on suspect JI terrorists.train from his house to visit or work at a suspect facility or a propaganda newsphoto of dignitaries lined up in front of a suspect facility could allow an imageryanalyst to find that facility. Similarly, as mentioned above, identification thatGeneral “Joe” A heads <strong>the</strong> Missile Corps in City S and Mr. “Bob” B works <strong>for</strong> <strong>the</strong>Atomic Energy Commission in City A through HUMINT and/or OSINT could bevery valuable to a SIGINT analyst who intercepts conversations between “Joe”and “Bob” about “special shipments” where <strong>the</strong> phones at each end are in <strong>the</strong> correctcities <strong>for</strong> <strong>the</strong> two offices.Strategic <strong>Analysis</strong> of a WMD Program—How do we assemble all <strong>the</strong>data into a multi-dimensional model?The kinds and amount of data that can potentially be used in a multidimensionalanalysis of a WMD program is enormous. At first glance it appears thatenormous computing power plus new kinds of “data-mining” tools are necessarybecause of <strong>the</strong> NIMD challenge, “How do we extract Novel Intelligence from114