technoMancers . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 130 > I know that Netcat’s rep score took a bit of a plunge when she revealed herself some time ago, but I don’t think there’s any better source on technomacers aside from technomancers themselves. I have approved two others to this Jackpoint discussion to provide some alternate viewpoints on the matter. Please welcome undernet guru Otaku-Zuku and Inbus, a technomancer who is working for Technicolor Wings. Let’s hope this discussion soothes some of the wounds generated over the past year. > FastJack eMerging Posted By: Netcat “How is it, being a technomancer?” I have been asked this question numerous times since my “coming out.” Even if you haven’t asked it openly, you’re probably wondering what it is like being a walking commlink. Though I still encounter mistrust, prejudice, and suspicion simply because of what I am—even here on Jackpoint—I’m paying back a favor to FastJack here by providing a personal report on my Emerging (that’s what us technomancers call the event that introduced us to the Resonance, sort of like how magicians refer to their Awakening) and how I experience the real and the digital world. Being in reSonance The first thing you have to understand is that I never asked to be what I am. I just am. In the years that followed the Crash 2.0, I made peace with myself and accepted that I am different now, that something changed me. I cannot say how it happened, though I can say that the Crash somehow triggered it. Here’s the story. Before ´64 I was a student on Matrix technology and system development, though that wasn’t my real passion. I was a passionate gamer and as interested in the code as any Matrix freak. I did some small scale hacking and code breaking under the same online handle I still use now—nothing spectacular, though, and definitely not on the level of our hacker wunderkind Slamm–0! > Don’t flatter me. No, just kidding. Continue. > Slamm–0! The day of the Crash, I was killing time as I often did, hacking through the levels of Paranormal Crisis to obtain some ultra-scarce modifications and gear for an avatar of mine. I don’t remember exactly what happened when the Crash hit, but like many others, I was trapped in the Matrix. I have some very faint memories—just a few images and sensations really, plus a fair bit of confusion. Then I came to in an Emergency Room. My roommate had found me slumped on the couch, still jacked in, with static on the display screen. He pulled the plug and got me to a hospital. It took a few days before I was released from the hospital. I was disoriented for most of that time, and the hospital was overwhelmed with other people who had suffered during the Crash—including dozens who had been trapped online, just like me. The doctors hadn’t found any lasting neurological damage they said, so they sent me home with a bottle of painkillers for the non-stop migraine I still had. At this point, I had no idea that my life had changed. Some weeks and months passed, during which I experienced a few … strange encounters. Sometimes there where whispers as if unseen people were talking to me. Today I know it was the noise and electronic prompts from devices I had unconsciously interacted with. Sometimes I saw things that weren’t there, data traffic shaped into images by my brain so that I could understand them. Electronic devices started to function strangely around me. I chalked it on my nerves and post-traumatic stress, trying to ignore it all until the changes were so blatant that I couldn’t turn a blind eye anymore. I was confused and frightened, looking for help, but most of the “experts” I visited thought I was a freak, crazy, or overstressed. I started to worry that I was going to be locked away. > Oh, cry me a river. You can pull our heart strings as long as you want, but that won’t persuade me that your kind and your AI allies/ creators are not a threat to metahumanity. It doesn’t matter if you were a hacker before—you’re a mutation now, a freak of nature. For me, you are just a ticking time bomb waiting to explode. > Clockwork > One very important point that needs to be made here is that not all technomancers were “created” by the Crash. Take me, for example. I was hiking in the mountains when the Crash hit, and didn’t even hear about until a few days afterward. Before my Emergence, I never met an AI, never saw a ghost in the machine, never had a run in with Black IC—heck, I never even hacked anything. Then one day back in ’68 I was doing maintenance on a drone, running diagnostics on its OS, when I realized my commlink had been accidentally turned off. It confused the hell out of me at first, I couldn’t figure out how I was accessing the drone with no ‘link. Over the next few weeks, though, I experimented a bit and managed to replicate the situation, and even go a bit further. The day I jumped into a drone, rigging it direct via VR, commlink-free, I knew I was something different. I’ve heard similar stories from other technomancers—some of them even dating to before the Crash. So don’t assume we’re a product of the Crash, or manipulated by AIs, or any other such nonsense. If you do, you’re just expressing your ignorance. > Inbus > The Sixth World has seen many strange things, and I’m sure we’ll see even stranger ones in the years to come. > Icarus With the installation of the new Matrix and the distribution of commlinks and all kinds of wireless devices, it became worse each week. To walk down a street and have thousands of prompts, data projections, and transmissions raining down on me every second was hard to bear. The more traffic there was clouding the digital ether, the more I had trouble adjusting and dealing with the data flow. > I imagine it would be much like constant, unstoppable mind reading. If telepaths existed, they would need to learn to shut out the thoughts of any person they interact with or who even comes close to them. I don’t envy technomancers, since there is surely a lot more traffic and devices than people. I’m no computer wiz, but I know there are a plethora of processes going on my commlink that Unwired Simon Wentworth (order #1132857) 9
Simon Wentworth (order #1132857) 9
- Page 1 and 2:
TM Simon Wentworth (order #1132857
- Page 3 and 4:
Simon Wentworth (order #1132857) 9
- Page 5 and 6:
Malware 86 Agents 87 Botnets 88 the
- Page 7 and 8:
JackPoint StatS___ 57 users current
- Page 9 and 10:
Simon Wentworth (order #1132857) 9
- Page 11 and 12:
AR transmissions are so easy to eav
- Page 13 and 14:
And I’m even happier when I can i
- Page 15 and 16:
tHe aUgMented worLd The augmented w
- Page 17 and 18:
people started cobbling together re
- Page 19 and 20:
While the cheaper commlinks are onl
- Page 21 and 22:
Matrix criMeS > I’ve downloaded a
- Page 23 and 24:
“protection rackets” against vi
- Page 25 and 26:
a general agreement that in order t
- Page 27 and 28:
Now, to operate in the sprawl, you
- Page 29 and 30:
capabilities and resources to do it
- Page 31 and 32:
popULar SoUSveiLLance videoS knight
- Page 33 and 34:
drug treatments during incarceratio
- Page 35 and 36:
Simon Wentworth (order #1132857) 9
- Page 37 and 38:
of more than one sprite at a time.
- Page 39 and 40:
intuitive Hacking Cost: 5 BP A char
- Page 41 and 42:
tweaking tHe rULeS Gamemasters and
- Page 43 and 44:
Simon Wentworth (order #1132857) 9
- Page 45 and 46:
‘link will s-l-o-w d-o-w-n, big t
- Page 47 and 48:
gram and a massive amount of time (
- Page 49 and 50:
. . . Matrix topoloGy . . . Hex was
- Page 51 and 52:
Simon Wentworth (order #1132857) 9
- Page 53 and 54:
track programs are not able to dete
- Page 55 and 56:
node attributes like a metaphor or
- Page 57 and 58:
datatrail Every interaction on the
- Page 59 and 60:
a castle could represent a control
- Page 61 and 62:
Simsense can also be used for exper
- Page 63 and 64:
Simon Wentworth (order #1132857) 9
- Page 65 and 66:
with their image links is an expens
- Page 67 and 68:
To avoid detection, the hacker can
- Page 69 and 70:
aLertS Another important line of de
- Page 71 and 72:
B A R S C I L W ESS 3 2 3 2 3 4 4 3
- Page 73 and 74:
encryption on the access log of the
- Page 75 and 76:
filled with a high-rating Data Bomb
- Page 77 and 78:
You also need to choose the Matrix
- Page 79 and 80:
Sculpting: The node looks a lot lik
- Page 81 and 82: Hardware: Saeder-Krupp Schwermetall
- Page 83 and 84: Simon Wentworth (order #1132857) 9
- Page 85 and 86: Don’t call me a script kid Don’
- Page 87 and 88: ight commands to bring those things
- Page 89 and 90: drivers on my commlink before I tur
- Page 91 and 92: what it sounds like: two or more ha
- Page 93 and 94: Yep. You can also stick malware int
- Page 95 and 96: gaMe inforMation The Hacker’s Han
- Page 97 and 98: paYdata General rules for fencing p
- Page 99 and 100: Pistons is researching the NeoNET A
- Page 101 and 102: Spoofing commands from a user with
- Page 103 and 104: to Mook or not to Mook? For some ch
- Page 105 and 106: Issuing commands to a smartgun thro
- Page 107 and 108: igger trickS Like hackers, riggers
- Page 109 and 110: Simon Wentworth (order #1132857) 9
- Page 111 and 112: Server-Side prograMS Server-side pr
- Page 113 and 114: cess (even if the agent tries to ha
- Page 115 and 116: worms). To match the opposition, ho
- Page 117 and 118: Mute Program Types: Common, Hacking
- Page 119 and 120: temporary degradation can be restor
- Page 121 and 122: advanced prograMMing taBLe Software
- Page 123 and 124: prone to degradation. This is in pa
- Page 125 and 126: dataworms Dataworms are a stealth t
- Page 127 and 128: military and police units, professi
- Page 129 and 130: them and plot them on a three-dimen
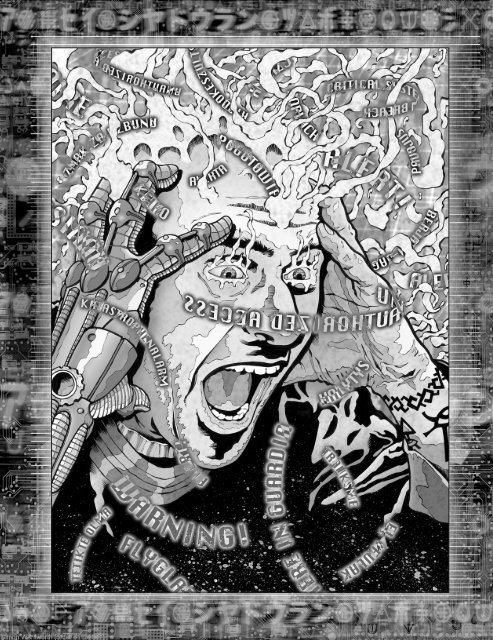
- Page 131: . . . technoMancers . . . The secur
- Page 135 and 136: attuning to a particular part of th
- Page 137 and 138: advanced tecHnoMancer rULeS The rec
- Page 139 and 140: Streams are still evolving and are
- Page 141 and 142: info Savants Fading: Intuition + Re
- Page 143 and 144: experience, induced by unfiltered e
- Page 145 and 146: don’t have to be strictly technom
- Page 147 and 148: new ecHoeS The following section ex
- Page 149 and 150: Sift Technomancers who possess this
- Page 151 and 152: Neuroleptic: This widget creates a
- Page 153 and 154: make are geared towards someone wit
- Page 155 and 156: Simon Wentworth (order #1132857) 9
- Page 157 and 158: Pilot Response Firewall Matrix INIT
- Page 159 and 160: traceroUte taBLe Subject Interacts
- Page 161 and 162: • It may raise one complex form i
- Page 163 and 164: . . . Matrix phenoMena . . . It’s
- Page 165 and 166: Simon Wentworth (order #1132857) 9
- Page 167 and 168: gaMe inforMation This section provi
- Page 169 and 170: (plus an additional box if the AI h
- Page 171 and 172: known aiS These are but a few examp
- Page 173 and 174: Uv nodeS—at tHe edge of reaLitY I
- Page 175 and 176: is something larger beyond the curt
- Page 177 and 178: the realm where the source code was
- Page 179 and 180: infektors The Infektors’ ultimate
- Page 181 and 182: corrupting it into a temporary diss
- Page 183 and 184:
Pilot Response Firewall Matrix INIT
- Page 185 and 186:
Simon Wentworth (order #1132857) 9
- Page 187 and 188:
former prematurely and leave them o
- Page 189 and 190:
playback gear On the most basic lev
- Page 191 and 192:
y default can be used repeatedly an
- Page 193 and 194:
to explain the missing time. Also,
- Page 195 and 196:
compartmentalized pieces of informa
- Page 197 and 198:
. . . Matrix Gear . . . Glitch was
- Page 199 and 200:
Simon Wentworth (order #1132857) 9
- Page 201 and 202:
eLectronicS Electronics follow all
- Page 203 and 204:
Hacker ServiceS See Buying a Better
- Page 205 and 206:
Software Suites Availability Cost H
- Page 207 and 208:
SaMpLe nodeS (cont.) . . . . . . .
- Page 209 and 210:
SaMpLe SpiderS (cont.) Security tec