comStar Firewall alert - PhaseThrough
comStar Firewall alert - PhaseThrough
comStar Firewall alert - PhaseThrough
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
hacker’s handbook . . . . . . . . . . . . . . . . . . . . . . . . . .<br />
94<br />
crow service holds on to the money/goods, eventually returning<br />
them if the deal falls through.<br />
piracY<br />
Cracking copy protection on legally purchased software<br />
is covered on p. 228 of SR4 (see the Cracking Copy Protection<br />
table for suggested thresholds). Illegal software, however, be it<br />
home-coded hacking utilities or a copy of a cracked program,<br />
has difficulties all its own. Programs in the Sixth World are constantly<br />
changing to keep up with the cutting edge of technology,<br />
and periodic patches and updates are<br />
the norm rather than the exception.<br />
Unfortunately, these patches and updates<br />
are only for legal purchasers and<br />
licensers of the program—or in the<br />
case of hacker software, may not exist<br />
at all—and without them a program<br />
slowly slides into obsolescence. A<br />
hacker can stall this degeneration either<br />
by fixing the code herself, finding<br />
the patch or update somewhere else on<br />
the Matrix, or by simply downloading<br />
a newer, updated version of the<br />
same program. (See Legal vs. Pirated<br />
Software, p. 108.)<br />
finding pirate networks<br />
A regular Data Search on the open Matrix never reveals<br />
where a hacker can download a rated program or its updates patch<br />
for free, where a runner might find the detailed AR schematics for<br />
the latest wiz tech toy, or where the drivers for that used piece of<br />
cyberware are. Within minutes of such information being posted,<br />
law enforcement hackers appear in the node to investigate all such<br />
claims and trace and arrest whoever is making the claims or offers.<br />
However, with a little work a hacker can gain access to the<br />
peer-to-peer file sharing networks of the Cracker Underground<br />
(see Virtual Private Networks, below), where she can find and<br />
download programs for a nominal fee.<br />
Finding and getting access to an appropriate network requires<br />
an Extended Data Search + Browse (8, 1 day) Test. Once connected<br />
to such a network, the character doesn’t need to find another one<br />
unless the network gets shut down, or if it doesn’t have the program<br />
she’s looking for (both at the gamemaster’s discretion).<br />
downloading programs<br />
Once a character has made contact with the<br />
Cracker Underground, he can start looking for something<br />
to download. To find a specific program on the<br />
file sharing network, make an Extended Data Search +<br />
Browse (Availability + Desired rating, 1 Combat Turn)<br />
Test. Downloading the program to your commlink or<br />
terminal costs 10 percent of the street price of the program<br />
(see Program Costs and Availability, p. 228, SR4).<br />
A glitch on the Search Test indicates the program is<br />
not on the network, and the hacker must find another<br />
network and try again; a critical glitch indicates the<br />
character has downloaded a bogus program infected<br />
with one or more viruses.<br />
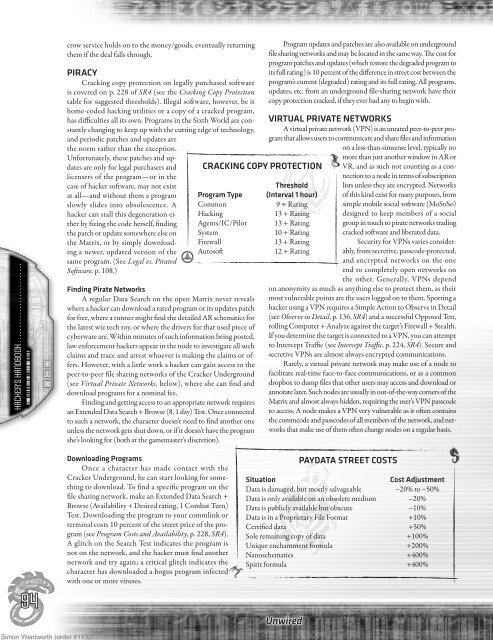
cracking copY protection<br />
threshold<br />
program type (interval 1 hour)<br />
Common 9 + Rating<br />
Hacking 13 + Rating<br />
Agents/IC/Pilot 13 + Rating<br />
System 10 + Rating<br />
<strong>Firewall</strong> 13 + Rating<br />
Autosoft 12 + Rating<br />
Program updates and patches are also available on underground<br />
file sharing networks and may be located in the same way. The cost for<br />
program patches and updates (which restore the degraded program to<br />
its full rating) is 10 percent of the difference in street cost between the<br />
program’s current (degraded) rating and its full rating. All programs,<br />
updates, etc. from an underground file-sharing network have their<br />
copy protection cracked, if they ever had any to begin with.<br />
virtUaL private networkS<br />
A virtual private network (VPN) is an unrated peer-to-peer program<br />
that allows users to communicate and share files and information<br />
on a less-than-simsense level, typically no<br />
Unwired<br />
more than just another window in AR or<br />
VR, and as such not counting as a connection<br />
to a node in terms of subscription<br />
lists unless they are encrypted. Networks<br />
of this kind exist for many purposes, from<br />
simple mobile social software (MoSoSo)<br />
designed to keep members of a social<br />
group in touch to pirate networks trading<br />
cracked software and liberated data.<br />
Security for VPNs varies considerably,<br />
from secretive, passcode-protected,<br />
and encrypted networks on the one<br />
end to completely open networks on<br />
the other. Generally, VPNs depend<br />
on anonymity as much as anything else to protect them, as their<br />
most vulnerable points are the users logged on to them. Spotting a<br />
hacker using a VPN requires a Simple Action to Observe in Detail<br />
(see Observe in Detail, p. 136, SR4) and a successful Opposed Test,<br />
rolling Computer + Analyze against the target’s <strong>Firewall</strong> + Stealth.<br />
If you determine the target is connected to a VPN, you can attempt<br />
to Intercept Traffic (see Intercept Traffic, p. 224, SR4). Secure and<br />
secretive VPNs are almost always encrypted communications.<br />
Rarely, a virtual private network may make use of a node to<br />
facilitate real-time face-to-face communications, or as a common<br />
dropbox to dump files that other users may access and download or<br />
annotate later. Such nodes are usually in out-of-the-way corners of the<br />
Matrix and almost always hidden, requiring the user’s VPN passcode<br />
to access. A node makes a VPN very vulnerable as it often contains<br />
the commcode and passcodes of all members of the network, and networks<br />
that make use of them often change nodes on a regular basis.<br />
paYdata Street coStS<br />
Situation cost adjustment<br />
Data is damaged, but mostly salvageable –20% to –50%<br />
Data is only available on an obsolete medium –20%<br />
Data is publicly available but obscure –10%<br />
Data is in a Proprietary File Format +10%<br />
Certified data +50%<br />
Sole remaining copy of data +100%<br />
Unique enchantment formula +200%<br />
Nanoschematics +400%<br />
Spirit formula +400%<br />
Simon Wentworth (order #1132857) 9