Matrix topoloGy . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 48 Hardware The basic building blocks of the Matrix in Shadowrun are devices of varying processing power (see Nodes, p. 57) and their interactions through fiberoptic cables, radio waves, satellites, and sometimes laser or microwave links (see Data Exchange, p. 53). In 2070, almost everything carries some kind of node with it. Whether it’s RFIDs in clothes, small processors in refrigerators, commlinks in jewelry, or full-blown servers in huge racks, nodes are all over the place. The air is constantly filled with a buzz of radio waves, coherent signals directed at satellites, and fiberoptic cables pulsing with the light of data transfer between continents. In short, the Matrix relies on the hardware that forms its parts—a fact that was known before the Crash 2.0 but often overlooked. nodeS Nodes are the most important building blocks of the Matrix. Every computerized device able to execute programs and instructions is a node. They provide the raw processing power of the global network and are the places of the Matrix (see Sculpting, p. 55). Everything governed by standard Matrix protocols happens in nodes. They run programs, store data, accept connections, and run personas and agents. Each node is governed by an operating system, from which it derives its <strong>Firewall</strong> and System attributes (see Operating Systems, p. 51). Its physical hardware components determine its Response and Signal attributes. There are three general categories of nodes: peripheral nodes, standard nodes, and nexi. Apart from the four Matrix attributes, a node is characterized by its access ID, persona limit, and processor limit. Access ID: Every node has a hardwired access ID, which serves as its address in the Matrix. If someone wants to find a node, they look up its access ID. Persona Limit: This is the maximum number of persona that may simultaneously run/originate on the device. Note that this only counts users who are using this node to get online, it does not count persona running on another node that access this node. Processor Limit: This is the number of programs the node can run before it starts to experience Response degradation (see Matrix Attributes, p. 212, SR4). For standard nodes, the processor limit is equal to System rating. SaMpLe peripHeraL nodeS Device Response Signal System <strong>Firewall</strong> AR Glove 2 2 1 1 Credstick 2 2 6 6 Fridge 1 3 2 1 RFID tag 1 1 1 1 Security Camera 2 3 2 4 Smartgun 2 1 3 4 peripheral nodes Peripheral nodes, or peripherals, and the devices they run on can be found in almost every single item in 2070. Peripheral nodes are common in objects that don’t require the computing, processing, and networking capabilities of standard nodes, but that benefit from being networked or accessed in some way. RFIDs carry peripheral nodes; toasters, fridges, and guns contain them; and even clothes facilitate peripheral nodes to process information. Peripherals use the same rules as standard nodes (see Devices and Software Ratings, p. 206, SR4), with some restrictions. They are only able to run a single persona and can only run programs they are designed to use. Matrix attributes of peripheral nodes range from 1 to 6 just like standard nodes, though most peripherals have low Response ratings. For simplicity, most peripheral nodes are given a single Device rating to represent all of their Matrix attributes (see Device Rating, p. 213, SR4), but gamemasters should feel free to adjust ratings as they feel appropriate. Since the operating systems of peripheral nodes are far more limited and focused, their System rating is not restricted by the Response rating, as is the case with standard nodes. In other words, the System rating of peripheral nodes may exceed Response rating without penalty. Peripheral nodes can only run one persona at a time, they are not designed for multiple users. For this reason, they only have admin accounts, but these accounts do not receive the +6 threshold modifier for hacking (treat them as standard accounts). They can, however, be clustered with other minor nodes, acting in concert as a single super-node (see Clusters, p. 55). To guard against their weak security, peripheral nodes are often slaved to more secure nodes (see Slaving, p. 59). Other functions, like data storage, communication with other nodes, or the representation of peripheral nodes in VR, work exactly like standard nodes. Standard nodes Standard nodes are run by commlinks, terminals, home telecoms, and almost any object that is portable and capable of running a single persona and a number of programs or agents. Standard nodes use the rules given for nodes (see Device and Software Ratings, p. 206, SR4). They have standard processor limits. Standard nodes may only run a single persona at a time, but the interface allows individual users to tailor the persona to their particular settings and preferences. Unwired Simon Wentworth (order #1132857) 9
Simon Wentworth (order #1132857) 9
- Page 1 and 2: TM Simon Wentworth (order #1132857
- Page 3 and 4: Simon Wentworth (order #1132857) 9
- Page 5 and 6: Malware 86 Agents 87 Botnets 88 the
- Page 7 and 8: JackPoint StatS___ 57 users current
- Page 9 and 10: Simon Wentworth (order #1132857) 9
- Page 11 and 12: AR transmissions are so easy to eav
- Page 13 and 14: And I’m even happier when I can i
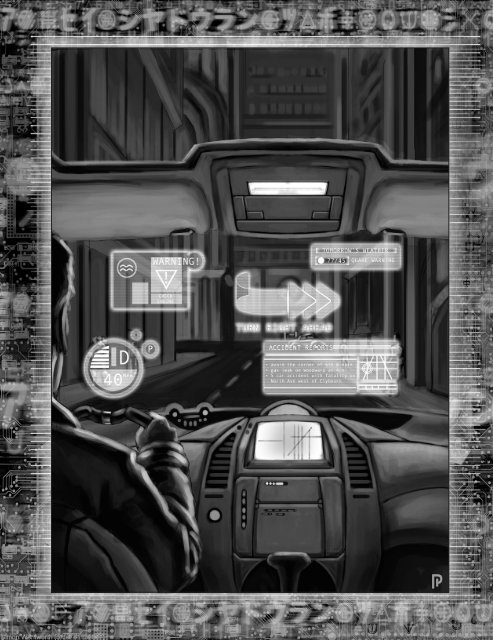
- Page 15 and 16: tHe aUgMented worLd The augmented w
- Page 17 and 18: people started cobbling together re
- Page 19 and 20: While the cheaper commlinks are onl
- Page 21 and 22: Matrix criMeS > I’ve downloaded a
- Page 23 and 24: “protection rackets” against vi
- Page 25 and 26: a general agreement that in order t
- Page 27 and 28: Now, to operate in the sprawl, you
- Page 29 and 30: capabilities and resources to do it
- Page 31 and 32: popULar SoUSveiLLance videoS knight
- Page 33 and 34: drug treatments during incarceratio
- Page 35 and 36: Simon Wentworth (order #1132857) 9
- Page 37 and 38: of more than one sprite at a time.
- Page 39 and 40: intuitive Hacking Cost: 5 BP A char
- Page 41 and 42: tweaking tHe rULeS Gamemasters and
- Page 43 and 44: Simon Wentworth (order #1132857) 9
- Page 45 and 46: ‘link will s-l-o-w d-o-w-n, big t
- Page 47 and 48: gram and a massive amount of time (
- Page 49: . . . Matrix topoloGy . . . Hex was
- Page 53 and 54: track programs are not able to dete
- Page 55 and 56: node attributes like a metaphor or
- Page 57 and 58: datatrail Every interaction on the
- Page 59 and 60: a castle could represent a control
- Page 61 and 62: Simsense can also be used for exper
- Page 63 and 64: Simon Wentworth (order #1132857) 9
- Page 65 and 66: with their image links is an expens
- Page 67 and 68: To avoid detection, the hacker can
- Page 69 and 70: aLertS Another important line of de
- Page 71 and 72: B A R S C I L W ESS 3 2 3 2 3 4 4 3
- Page 73 and 74: encryption on the access log of the
- Page 75 and 76: filled with a high-rating Data Bomb
- Page 77 and 78: You also need to choose the Matrix
- Page 79 and 80: Sculpting: The node looks a lot lik
- Page 81 and 82: Hardware: Saeder-Krupp Schwermetall
- Page 83 and 84: Simon Wentworth (order #1132857) 9
- Page 85 and 86: Don’t call me a script kid Don’
- Page 87 and 88: ight commands to bring those things
- Page 89 and 90: drivers on my commlink before I tur
- Page 91 and 92: what it sounds like: two or more ha
- Page 93 and 94: Yep. You can also stick malware int
- Page 95 and 96: gaMe inforMation The Hacker’s Han
- Page 97 and 98: paYdata General rules for fencing p
- Page 99 and 100: Pistons is researching the NeoNET A
- Page 101 and 102:
Spoofing commands from a user with
- Page 103 and 104:
to Mook or not to Mook? For some ch
- Page 105 and 106:
Issuing commands to a smartgun thro
- Page 107 and 108:
igger trickS Like hackers, riggers
- Page 109 and 110:
Simon Wentworth (order #1132857) 9
- Page 111 and 112:
Server-Side prograMS Server-side pr
- Page 113 and 114:
cess (even if the agent tries to ha
- Page 115 and 116:
worms). To match the opposition, ho
- Page 117 and 118:
Mute Program Types: Common, Hacking
- Page 119 and 120:
temporary degradation can be restor
- Page 121 and 122:
advanced prograMMing taBLe Software
- Page 123 and 124:
prone to degradation. This is in pa
- Page 125 and 126:
dataworms Dataworms are a stealth t
- Page 127 and 128:
military and police units, professi
- Page 129 and 130:
them and plot them on a three-dimen
- Page 131 and 132:
. . . technoMancers . . . The secur
- Page 133 and 134:
Simon Wentworth (order #1132857) 9
- Page 135 and 136:
attuning to a particular part of th
- Page 137 and 138:
advanced tecHnoMancer rULeS The rec
- Page 139 and 140:
Streams are still evolving and are
- Page 141 and 142:
info Savants Fading: Intuition + Re
- Page 143 and 144:
experience, induced by unfiltered e
- Page 145 and 146:
don’t have to be strictly technom
- Page 147 and 148:
new ecHoeS The following section ex
- Page 149 and 150:
Sift Technomancers who possess this
- Page 151 and 152:
Neuroleptic: This widget creates a
- Page 153 and 154:
make are geared towards someone wit
- Page 155 and 156:
Simon Wentworth (order #1132857) 9
- Page 157 and 158:
Pilot Response Firewall Matrix INIT
- Page 159 and 160:
traceroUte taBLe Subject Interacts
- Page 161 and 162:
• It may raise one complex form i
- Page 163 and 164:
. . . Matrix phenoMena . . . It’s
- Page 165 and 166:
Simon Wentworth (order #1132857) 9
- Page 167 and 168:
gaMe inforMation This section provi
- Page 169 and 170:
(plus an additional box if the AI h
- Page 171 and 172:
known aiS These are but a few examp
- Page 173 and 174:
Uv nodeS—at tHe edge of reaLitY I
- Page 175 and 176:
is something larger beyond the curt
- Page 177 and 178:
the realm where the source code was
- Page 179 and 180:
infektors The Infektors’ ultimate
- Page 181 and 182:
corrupting it into a temporary diss
- Page 183 and 184:
Pilot Response Firewall Matrix INIT
- Page 185 and 186:
Simon Wentworth (order #1132857) 9
- Page 187 and 188:
former prematurely and leave them o
- Page 189 and 190:
playback gear On the most basic lev
- Page 191 and 192:
y default can be used repeatedly an
- Page 193 and 194:
to explain the missing time. Also,
- Page 195 and 196:
compartmentalized pieces of informa
- Page 197 and 198:
. . . Matrix Gear . . . Glitch was
- Page 199 and 200:
Simon Wentworth (order #1132857) 9
- Page 201 and 202:
eLectronicS Electronics follow all
- Page 203 and 204:
Hacker ServiceS See Buying a Better
- Page 205 and 206:
Software Suites Availability Cost H
- Page 207 and 208:
SaMpLe nodeS (cont.) . . . . . . .
- Page 209 and 210:
SaMpLe SpiderS (cont.) Security tec