comStar Firewall alert - PhaseThrough
comStar Firewall alert - PhaseThrough
comStar Firewall alert - PhaseThrough
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
gaMe inforMation<br />
The Hacker’s Handbook is designed to give player characters<br />
more options for using the Matrix with their games, expanding<br />
the opportunities for both hackers and non-hackers to interact<br />
through the Matrix. The rules and material presented in this<br />
chapter can add depth to a campaign, making shadowruns more<br />
challenging and rewarding for clever players and gamemasters.<br />
BUYing a Better Hacker<br />
Not every character is cut out to be a hacker, and not every<br />
hacker has the time and Karma to be the best in every possible<br />
corner of the Matrix. There’s no shame (well, okay, maybe a little)<br />
in paying another hacker to do what you can’t do, or what you<br />
could do if you had the time and equipment. What follows below<br />
is a list of common services hackers are hired to perform and the<br />
usual street costs and availability for them. A hacker player character<br />
looking to do a little freelancing in the downtime between<br />
runs might look for some of these jobs herself.<br />
anonymization<br />
When somebody in 2070 wants to call a friend, he simply<br />
dials his friend’s commcode. The commlink then connects to the<br />
MSP that issued the commcode and retrieves the access ID of the<br />
receiver. Using that access ID, it establishes the data request connection<br />
to the commlink receiving the call. In this process, the<br />
receiving commlink is aware of the access ID of the sending commlink<br />
(see Data Exchange, p. 53).<br />
Anonymization services work as mediators between the two<br />
participants of a commcall or any other data request. The data<br />
package is received by the anonymizing node and then forwarded<br />
to the receiver using the anonymizer’s access ID as sending ID<br />
(see Proxy Servers, p. 104). A trace will not reveal the access ID of<br />
the original sender, but rather the access ID of the mediator. To<br />
retrieve the real access ID, one must hack the proxy server node. If<br />
multiple proxy servers are used, each must be hacked.<br />
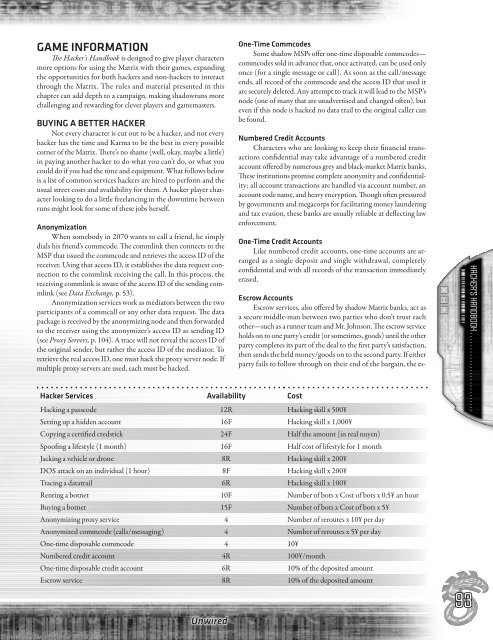
Hacker Services Availability Cost<br />
Unwired<br />
one-time commcodes<br />
Some shadow MSPs offer one-time disposable commcodes—<br />
commcodes sold in advance that, once activated, can be used only<br />
once (for a single message or call). As soon as the call/message<br />
ends, all record of the commcode and the access ID that used it<br />
are securely deleted. Any attempt to track it will lead to the MSP’s<br />
node (one of many that are unadvertised and changed often), but<br />
even if this node is hacked no data trail to the original caller can<br />
be found.<br />
numbered credit accounts<br />
Characters who are looking to keep their financial transactions<br />
confidential may take advantage of a numbered credit<br />
account offered by numerous grey and black-market Matrix banks.<br />
These institutions promise complete anonymity and confidentiality;<br />
all account transactions are handled via account number, an<br />
account code name, and heavy encryption. Though often pressured<br />
by governments and megacorps for facilitating money laundering<br />
and tax evasion, these banks are usually reliable at deflecting law<br />
enforcement.<br />
one-time credit accounts<br />
Like numbered credit accounts, one-time accounts are arranged<br />
as a single deposit and single withdrawal, completely<br />
confidential and with all records of the transaction immediately<br />
erased.<br />
escrow accounts<br />
Escrow services, also offered by shadow Matrix banks, act as<br />
a secure middle-man between two parties who don’t trust each<br />
other—such as a runner team and Mr. Johnson. The escrow service<br />
holds on to one party’s credit (or sometimes, goods) until the other<br />
party completes its part of the deal to the first party’s satisfaction,<br />
then sends the held money/goods on to the second party. If either<br />
party fails to follow through on their end of the bargain, the es-<br />
Hacking a passcode 12R Hacking skill x 500¥<br />
Setting up a hidden account 16F Hacking skill x 1,000¥<br />
Copying a certified credstick 24F Half the amount (in real nuyen)<br />
Spoofing a lifestyle (1 month) 16F Half cost of lifestyle for 1 month<br />
Jacking a vehicle or drone 8R Hacking skill x 200¥<br />
DOS attack on an individual (1 hour) 8F Hacking skill x 200¥<br />
Tracing a datatrail 6R Hacking skill x 100¥<br />
Renting a botnet 10F Number of bots x Cost of bots x 0.5¥ an hour<br />
Buying a botnet 15F Number of bots x Cost of bots x 5¥<br />
Anonymizing proxy service 4 Number of reroutes x 10¥ per day<br />
Anonymized commcode (calls/messaging) 4 Number of reroutes x 5¥ per day<br />
One-time disposable commcode 4 10¥<br />
Numbered credit account 4R 100¥/month<br />
One-time disposable credit account 6R 10% of the deposited amount<br />
Escrow service 8R 10% of the deposited amount<br />
Simon Wentworth (order #1132857) 9<br />
93<br />
hacker’s handbook . . . . . . . . . . . . . . . . . . . . . . . . . .