comStar Firewall alert - PhaseThrough
comStar Firewall alert - PhaseThrough
comStar Firewall alert - PhaseThrough
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
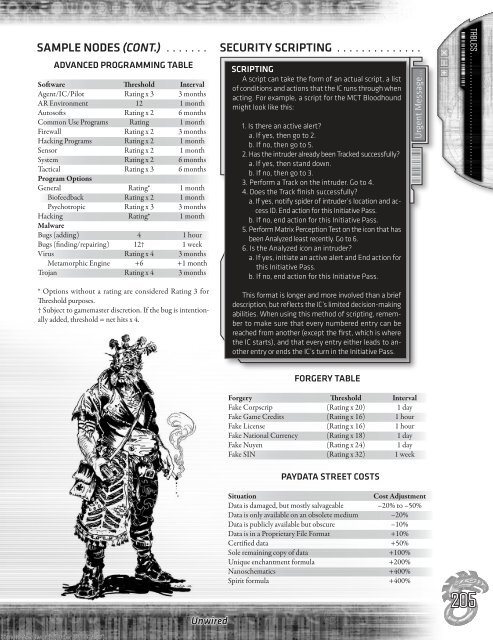
SaMpLe nodeS (cont.) . . . . . . . SecUritY Scripting . . . . . . . . . . . . . .<br />
advanced prograMMing taBLe<br />
Software Threshold Interval<br />
Agent/IC/Pilot Rating x 3 3 months<br />
AR Environment 12 1 month<br />
Autosofts Rating x 2 6 months<br />
Common Use Programs Rating 1 month<br />
<strong>Firewall</strong> Rating x 2 3 months<br />
Hacking Programs Rating x 2 1 month<br />
Sensor Rating x 2 1 month<br />
System Rating x 2 6 months<br />
Tactical Rating x 3 6 months<br />
Program Options<br />
General Rating* 1 month<br />
Biofeedback Rating x 2 1 month<br />
Psychotropic Rating x 3 3 months<br />
Hacking Rating* 1 month<br />
Malware<br />
Bugs (adding) 4 1 hour<br />
Bugs (finding/repairing) 12† 1 week<br />
Virus Rating x 4 3 months<br />
Metamorphic Engine +6 +1 month<br />
Trojan Rating x 4 3 months<br />
* Options without a rating are considered Rating 3 for<br />
Threshold purposes.<br />
† Subject to gamemaster discretion. If the bug is intentionally<br />
added, threshold = net hits x 4.<br />
Unwired<br />
Scripting<br />
A script can take the form of an actual script, a list<br />
of conditions and actions that the IC runs through when<br />
acting. For example, a script for the MCT Bloodhound<br />
might look like this:<br />
1. Is there an active <strong>alert</strong>?<br />
a. If yes, then go to 2.<br />
b. If no, then go to 5.<br />
2. Has the intruder already been Tracked successfully?<br />
a. If yes, then stand down.<br />
b. If no, then go to 3.<br />
3. Perform a Track on the intruder. Go to 4.<br />
4. Does the Track finish successfully?<br />
a. If yes, notify spider of intruder’s location and access<br />
ID. End action for this Initiative Pass.<br />
b. If no, end action for this Initiative Pass.<br />
5. Perform Matrix Perception Test on the icon that has<br />
been Analyzed least recently. Go to 6.<br />
6. Is the Analyzed icon an intruder?<br />
a. If yes, initiate an active <strong>alert</strong> and End action for<br />
this Initiative Pass.<br />
b. If no, end action for this Initiative Pass.<br />
This format is longer and more involved than a brief<br />
description, but reflects the IC’s limited decision-making<br />
abilities. When using this method of scripting, remember<br />
to make sure that every numbered entry can be<br />
reached from another (except the first, which is where<br />
the IC starts), and that every entry either leads to another<br />
entry or ends the IC’s turn in the Initiative Pass.<br />
Forgery Table<br />
Forgery Threshold Interval<br />
Fake Corpscrip (Rating x 20) 1 day<br />
Fake Game Credits (Rating x 16) 1 hour<br />
Fake License (Rating x 16) 1 hour<br />
Fake National Currency (Rating x 18) 1 day<br />
Fake Nuyen (Rating x 24) 1 day<br />
Fake SIN (Rating x 32) 1 week<br />
PAYDATA STREET COSTS<br />
Situation Cost Adjustment<br />
Data is damaged, but mostly salvageable –20% to –50%<br />
Data is only available on an obsolete medium –20%<br />
Data is publicly available but obscure –10%<br />
Data is in a Proprietary File Format +10%<br />
Certified data +50%<br />
Sole remaining copy of data +100%<br />
Unique enchantment formula +200%<br />
Nanoschematics +400%<br />
Spirit formula +400%<br />
205<br />
Simon Wentworth (order #1132857) 9<br />
tables . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .