- Page 2: Cover: The cover highlights four st
- Page 6 and 7: DEDICATION This book is dedicated t
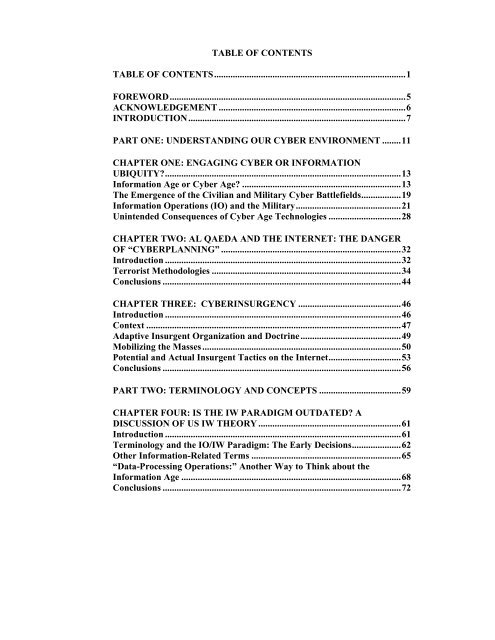
- Page 10 and 11: CHAPTER FIVE: COMPARING US, RUSSIAN
- Page 12 and 13: New Concept Weapons ...............
- Page 14 and 15: ACKNOWLEDGEMENT The author used onl
- Page 16 and 17: uzzword for IO writers. For example
- Page 18 and 19: ook) may contain the term Informati
- Page 20 and 21: PART ONE: UNDERSTANDING OUR CYBER E
- Page 22 and 23: the Internet; 7 (2.) “cyber is a
- Page 24 and 25: cutting-edge robotics to operate on
- Page 26 and 27: well as the Appendix “Summary of
- Page 28 and 29: This means that we are truly in a n
- Page 30 and 31: that computers are affecting our in
- Page 32 and 33: uncertainty is apparent in the fact
- Page 34 and 35: Civilians, on the other hand, are n
- Page 36 and 37: Unintended Consequences of Cyber Ag
- Page 38 and 39: accountability that we will eventua
- Page 40 and 41: CHAPTER TWO: AL QAEDA AND THE INTER
- Page 42 and 43: the net, even if they have the capa
- Page 44 and 45: on 21 June at www.drasat.com in Mic
- Page 46 and 47: ment groups present at the G8 confe
- Page 48 and 49: and without resorting to illegal me
- Page 50 and 51: offsetting the credibility of the R
- Page 52 and 53: to include computers in foreign cou
- Page 54 and 55: CHAPTER THREE: CYBERINSURGENCY Intr
- Page 56 and 57: websites has made it nearly impossi
- Page 58 and 59:
insurgency, but equally as deadly,
- Page 60 and 61:
of the SITE Institute, a nonprofit
- Page 62 and 63:
times. 104 Thus, the Cyber Age is o
- Page 64 and 65:
files and know they are an integral
- Page 66 and 67:
change and adapt to the insurgents
- Page 68 and 69:
PART TWO: TERMINOLOGY AND CONCEPTS
- Page 70 and 71:
than the existing doctrines of psyc
- Page 72 and 73:
primarily to systems and equipment
- Page 74 and 75:
if they are applicable to the US pa
- Page 76 and 77:
computer chips. US specialists tend
- Page 78 and 79:
Thus the data processor, possessed
- Page 80 and 81:
Conclusions The rapid pace of devel
- Page 82 and 83:
CHAPTER FIVE: COMPARING US, RUSSIAN
- Page 84 and 85:
The employment of the core capabili
- Page 86 and 87:
years earlier to write a book calle
- Page 88 and 89:
operational level fronts, fleets, a
- Page 90 and 91:
present) conflict. In the first con
- Page 92 and 93:
Dai listed three characteristics of
- Page 94 and 95:
would go to developing IW units. 15
- Page 96 and 97:
and sort out what happened thereby
- Page 98 and 99:
August 2000 issue of that journal.
- Page 100 and 101:
Finally, the main targets are enemy
- Page 102 and 103:
example, General Hal Hornburg, USAF
- Page 104 and 105:
This list is significantly differen
- Page 106 and 107:
Chinese IW expert Wang Baocun, writ
- Page 108 and 109:
a system meets a like system or if
- Page 110 and 111:
in technology and equipment. The la
- Page 112 and 113:
104
- Page 114 and 115:
PART THREE: APPLICATIONS AND CASE S
- Page 116 and 117:
us—virtual reality games, for exa
- Page 118 and 119:
A huge TV screen was located in the
- Page 120 and 121:
commander and operated together wit
- Page 122 and 123:
• Maintaining or restoring local
- Page 124 and 125:
What is new about the international
- Page 126 and 127:
or protracted—before it spreads o
- Page 128 and 129:
another as special interests (both
- Page 130 and 131:
interests) or balancing diffuse for
- Page 132 and 133:
with unmanned aerial vehicles (UAVs
- Page 134 and 135:
line of sight, monitoring) which ha
- Page 136 and 137:
peacemaking. This was also one of t
- Page 138 and 139:
Third, it is important that softwar
- Page 140 and 141:
132
- Page 142 and 143:
planning and strategic guidance def
- Page 144 and 145:
were about to be hit. The testimony
- Page 146 and 147:
NATO’s Information Superiority Th
- Page 148 and 149:
and the Department of Defense versu
- Page 150 and 151:
them, or did they really experience
- Page 152 and 153:
He noted that even the most advance
- Page 154 and 155:
prevent its air defense assets from
- Page 156 and 157:
Milosevic was to some extent irrati
- Page 158 and 159:
• Total information superiority d
- Page 160 and 161:
offsets and technological counters?
- Page 162 and 163:
international community needs to id
- Page 164 and 165:
important element to ascertaining t
- Page 166 and 167:
with people from differing cultures
- Page 168 and 169:
giving them a sense of loss of cont
- Page 170 and 171:
• Vector Technology - This includ
- Page 172 and 173:
uildups. These activities can uncov
- Page 174 and 175:
CHAPTER TEN: INFORMATION WARFARE IN
- Page 176 and 177:
the main prism through which Russia
- Page 178 and 179:
• Means for creating virtual real
- Page 180 and 181:
system was deployed in one of the a
- Page 182 and 183:
But new equipment also was on hand
- Page 184 and 185:
combat capabilities of ground troop
- Page 186 and 187:
Informed sources report that the GR
- Page 188 and 189:
destruction capability = exposure o
- Page 190 and 191:
Nikolayevich Zaritskiy added that t
- Page 192 and 193:
that time it had lost 100% in infos
- Page 194 and 195:
Finally, Pain noted that Russia’s
- Page 196 and 197:
population of the opposing side, ne
- Page 198 and 199:
civilians). Servicemen were also ta
- Page 200 and 201:
Nezavisimaya Gazeta [Independent Ne
- Page 202 and 203:
watchdog.cz-Prague watchdog on the
- Page 204 and 205:
equired to implement this work. The
- Page 206 and 207:
Conclusions Military reform in the
- Page 208 and 209:
PART FOUR: CYBER THREATS TO THE MIN
- Page 210 and 211:
CHAPTER ELEVEN: THE CYBER THREAT EN
- Page 212 and 213:
and other precision-guided missiles
- Page 214 and 215:
intent may in fact be invasive viru
- Page 216 and 217:
One answer to the problem of anomal
- Page 218 and 219:
He must be able to analyze and not
- Page 220 and 221:
Gulf, but wherever there are finger
- Page 222 and 223:
“new persuaders?” 387 They may
- Page 224 and 225:
ecause one side was helped. When he
- Page 226 and 227:
originator= s objectives. In variou
- Page 228 and 229:
The problem with today’s near-ins
- Page 230 and 231:
• Pretending there is unity of th
- Page 232 and 233:
emember that the manipulation of ev
- Page 234 and 235:
must ascertain what has been manipu
- Page 236 and 237:
• We must learn how to neutralize
- Page 238 and 239:
CHAPTER THIRTEEN: HUMAN NETWORK ATT
- Page 240 and 241:
A widespread Chinese view is that i
- Page 242 and 243:
egarding IT. One must also create n
- Page 244 and 245:
IW's Relation to Psychological Oper
- Page 246 and 247:
knowledge and innovate. The informa
- Page 248 and 249:
Russian Nontraditional Practices Th
- Page 250 and 251:
additional means, such as nuclear a
- Page 252 and 253:
what conditions the spirit of the s
- Page 254 and 255:
not the point. The issue is they fo
- Page 256 and 257:
didn’t commit this atrocity. I am
- Page 258 and 259:
eflexive control. He noted: The mos
- Page 260 and 261:
The chief task of reflexive control
- Page 262 and 263:
Given his advanced thinking about r
- Page 264 and 265:
and role-based characteristics appl
- Page 266 and 267:
Further, Leonenko noted that “how
- Page 268 and 269:
difference between the assessments
- Page 270 and 271:
advanced in having developed practi
- Page 272 and 273:
findings in great detail to Western
- Page 274 and 275:
PART FIVE: CONCLUSIONS AND APPENDIX
- Page 276 and 277:
CHAPTER FIFTEEN: CONCLUSIONS Termin
- Page 278 and 279:
If this is the key assumption of th
- Page 280 and 281:
of the mechanization and motorizati
- Page 282 and 283:
• The website www.almijlah.net/vb
- Page 284 and 285:
Muslim World Outreach Strategy. Rad
- Page 286 and 287:
A sixth conclusion is that the subj
- Page 288 and 289:
what information can or cannot pote
- Page 290 and 291:
market by telling the mob to buy or
- Page 292 and 293:
that produced a daily intelligence
- Page 294 and 295:
function. The use of blinding laser
- Page 296 and 297:
workstations, which led to inconsis
- Page 298 and 299:
APPENDIX ONE: IW ARTICLES BY THE AU
- Page 300 and 301:
“Russia’s ‘Netwar’ Capabili
- Page 302 and 303:
What Is Asymmetry? Judging by the m
- Page 304 and 305:
informational, and cultural securit
- Page 306 and 307:
Asymmetry can even express itself a
- Page 308 and 309:
democracy, free markets, [and] the
- Page 310 and 311:
APPENDIX THREE: THE COMPUTER: CYBER
- Page 312 and 313:
used. For instance, if an incident
- Page 314 and 315:
could manipulate electronic transac
- Page 316 and 317:
into the system. Copyrighted music
- Page 318 and 319:
(3) Computer and/or Hardware Can Be
- Page 320 and 321:
Making Digital Forensics a Discipli
- Page 322 and 323:
intellectual property. The Computer
- Page 324 and 325:
The second investigation path was t
- Page 326 and 327:
and only if data suggests a crime,
- Page 328 and 329:
Physical level analysis of a comput
- Page 330 and 331:
• File Comparison Utilities - Thi
- Page 332 and 333:
each element is a standard way of f
- Page 334 and 335:
Network Monitoring Some data as we
- Page 336 and 337:
servers, immediate disaster recover
- Page 338 and 339:
the computer attacker’s identity,
- Page 340 and 341:
attack. 547 Such action is justifie
- Page 342 and 343:
weapons and poison gas. Nations can
- Page 344 and 345:
Bibliography for Appendix 3 Casey,
- Page 347:
339